The digital security landscape witnessed a significant blow this week as the Google Threat Intelligence Group (GTIG), working in close concert with several key industry collaborators, successfully executed a coordinated disruption targeting IPIDEA, one of the most extensive and widely utilized residential proxy networks known to facilitate malicious cyber operations. This action represents a major victory in the ongoing battle against the exploitation of legitimate consumer devices for criminal endeavors, effectively severing the command and control (C2) architecture that underpinned the network’s vast operations.
The comprehensive takedown strategy involved the immediate neutralization of numerous domains critical to IPIDEA’s service delivery, including those responsible for managing compromised devices and routing the torrent of illicit proxy traffic. Crucially, the operation extended beyond infrastructure neutralization; GTIG disseminated detailed intelligence regarding the Software Development Kits (SDKs) employed by IPIDEA, the very mechanisms used to distribute the proxy functionality across millions of endpoints. This shared intelligence is vital for remediation across the software ecosystem.
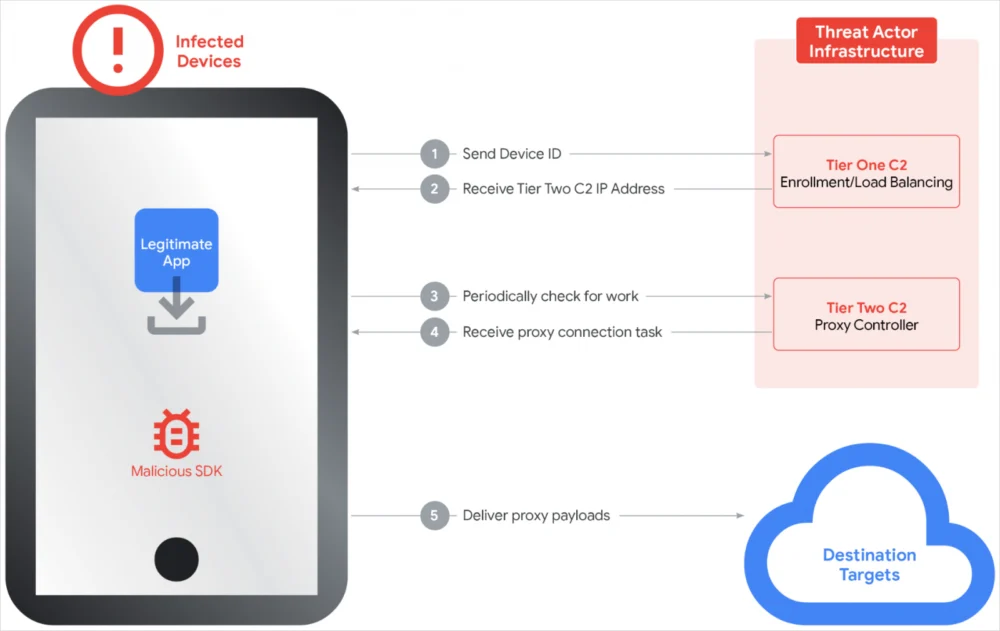
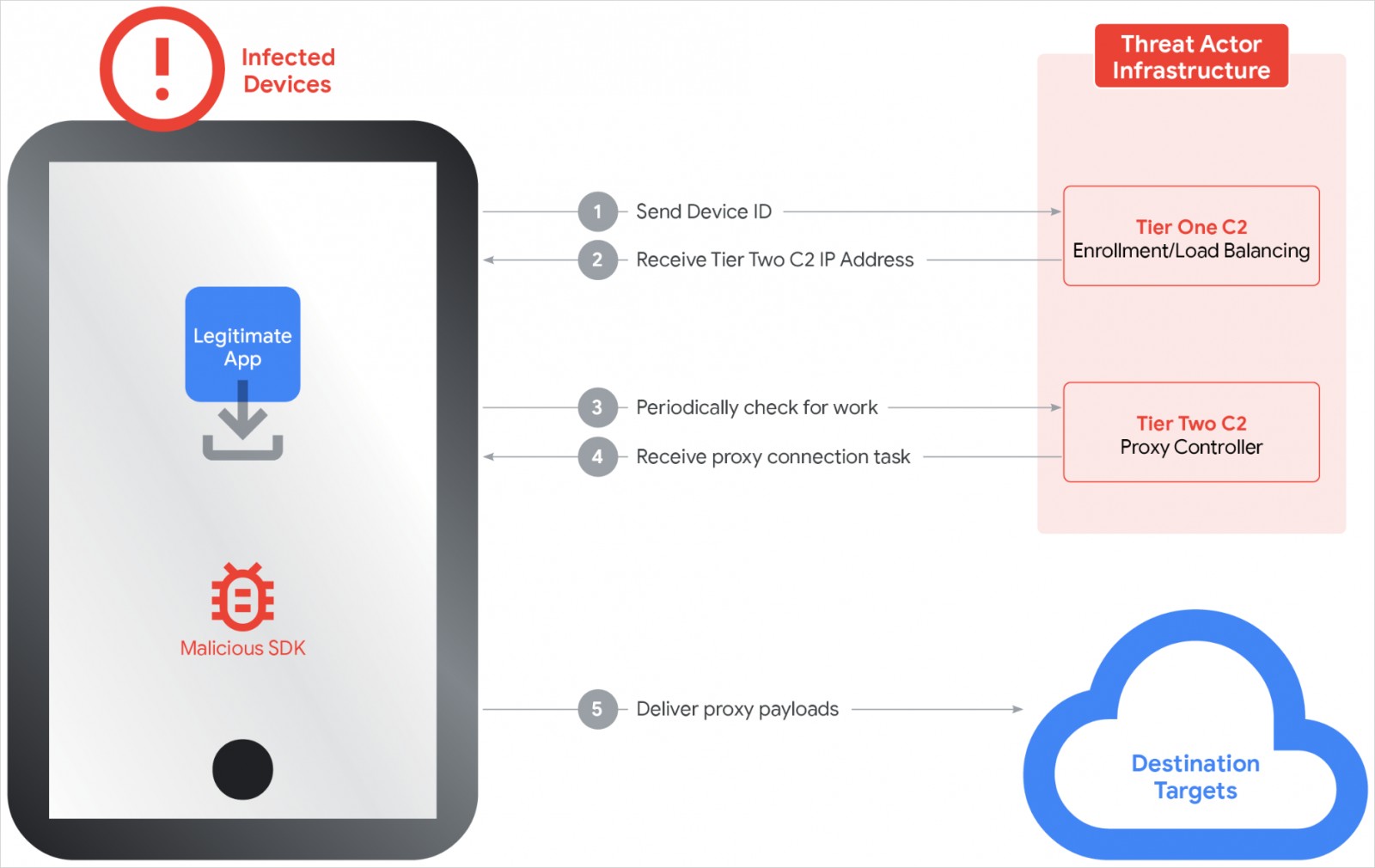
IPIDEA, which aggressively marketed itself to an estimated 6.7 million users globally, deceptively presented its offering as a standard Virtual Private Network (VPN) service, promising users encryption and the obfuscation of their true IP addresses. However, the reality was far more insidious. Residential proxy networks operate by commandeering the IP addresses of genuine home users or small business subscribers. This infection vector is typically realized through trojanized applications—software deceptively packaged as useful utilities—that, once installed, silently enroll the host device into the proxy network.
The gravity of this operation is underscored by recent court filings from Google, which explicitly detail how threat actors leverage these hijacked residential IPs. The primary uses identified include sophisticated account takeovers (ATOs), the mass creation of fraudulent accounts for spam or synthetic identity fraud, large-scale credential stuffing and theft, and the exfiltration of sensitive corporate or personal data. The core benefit to the adversary lies in camouflage: by routing their malicious traffic through a geographically diverse array of consumer IP addresses, attackers effectively cloak their true origin, creating immense hurdles for security teams attempting to detect, attribute, and block malicious flows.

GTIG analysis revealed the sheer scale of abuse facilitated by IPIDEA. In a single seven-day period, researchers documented over 550 unique threat groups utilizing the network’s exit nodes. The geographical diversity of these actors was striking, implicating groups originating from established threat landscapes, including China, Iran, Russia, and North Korea. The activities observed through these compromised nodes spanned the spectrum of modern cybercrime, from targeted attacks on victim Software-as-a-Service (SaaS) platforms and organized password spraying campaigns to the command and control of botnets and the obfuscation of attacker infrastructure.
This is not the first time IPIDEA has drawn the attention of the security community. Previous deep-dive reports, notably from Cisco Talos, had already connected the network to massive, sustained brute-forcing operations targeting VPN endpoints and Secure Shell (SSH) services globally. Furthermore, the infrastructure provided essential routing for some of the most notorious, high-volume Distributed Denial of Service (DDoS) botnets ever recorded, including the Aisuru botnet, previously linked to a staggering 297 Terabits per second (Tbps) attack, and the Kimwolf botnet, which specialized in abusing residential proxies to pivot and infect internal enterprise networks.
The method of mass enrollment employed by IPIDEA was technologically sophisticated and pervasive. Google identified that the network successfully enrolled devices via at least 600 distinct trojanized Android applications. These apps embedded proprietary proxying SDKs—specifically named Packet SDK, Castar SDK, Hex SDK, and Earn SDK—which performed the silent enrollment. On the desktop front, the network relied on over 3,000 trojanized Windows binaries masquerading as critical system components, such as legitimate Microsoft OneDriveSync updates or Windows Update packages, ensuring deep integration and persistence.
The business model behind IPIDEA was a tapestry of deception. Google’s investigation uncovered that the operators managed a minimum of 19 separate residential proxy businesses, all operating under the guise of legitimate commercial services. These entities sold access to the compromised pool of devices, which were infected with the sophisticated BadBox 2.0 malware variant. While the specific brand names were numerous, the critical finding was that these disparate services ultimately converged on a single, centralized C2 infrastructure controlled exclusively by the unidentified architects of IPIDEA.
In a direct defensive countermeasure on the mobile front, Google confirmed that Google Play Protect is now actively detecting and blocking applications containing the malicious IPIDEA-related SDKs on all up-to-date, certified Android devices. This automated protection is crucial for stemming the flow of new infections through the primary mobile vector.

Analysis of the network architecture revealed a layered Command and Control (C2) framework, designed for resilience and efficiency. The system utilized a two-tier structure. The first tier was responsible for high-level orchestration—providing essential configuration parameters, timing synchronization, and, most importantly, the dynamically updated lists of available proxy nodes for the second tier. The second tier, researchers estimate, comprised approximately 7,400 dedicated servers responsible for task assignment and the actual relaying of the vast quantities of proxy traffic. This separation provided a layer of abstraction, making it harder to trace the ultimate source of the control signals.
A key element of IPIDEA’s deceptive strategy involved offering seemingly benign services. Many of the associated applications provided the exact VPN or proxy functionality they advertised to the end-user. However, this legitimate functionality was merely the bait; concurrently, the device was registered as an exit node in the IPIDEA network, effectively forcing the user to unknowingly donate their bandwidth and IP address for criminal use.
The immediate consequence of the GTIG-led action is a severe degradation, if not total collapse, of IPIDEA’s existing operational capacity. However, the cybersecurity community must maintain vigilance. The takedown of infrastructure rarely equates to the permanent neutralization of the operators. It is highly probable that the threat actors behind IPIDEA are already engaged in contingency planning, seeking to acquire new domains, reconstitute their C2 structure, and repackage their SDKs for future deployment. As of this reporting, no arrests or formal indictments have been publicly announced, suggesting the operators remain at large and capable of future attempts at rebuilding.
Industry Implications and Expert Analysis
This successful disruption serves as a crucial reminder of the endemic risks associated with the residential proxy market. For enterprise defenders, the IPIDEA case highlights a paradigm shift in attacker methodology: the move from exploiting known vulnerabilities to leveraging the trust inherent in consumer software and hardware.
From an expert standpoint, the scale of IPIDEA—with 6.7 million reported users—underscores the critical vulnerability introduced when consumer utility apps prioritize convenience or free service over robust security vetting. Security leaders must now recognize that any free VPN, bandwidth-sharing app, or utility promising minor rewards for unused resources should be treated with extreme suspicion. These "earn-to-use" models are frequently a Trojan horse for malware delivery or, in this case, involuntary network participation.
The collaboration between Google and industry partners is another vital takeaway. Disassembling a global infrastructure of this complexity requires the aggregation of threat intelligence, domain registration data, network flow analysis, and malware forensics—capabilities that no single entity typically possesses entirely. This action reinforces the necessity of cross-sector information sharing to dismantle transnational cybercrime organizations that exploit global connectivity.
The use of the BadBox 2.0 malware specifically points to an evolution in how proxy malware maintains persistence and evades sandbox detection. Advanced malware variants often employ checks to ensure they are not operating within a virtualized or controlled analysis environment, allowing them to function normally on a genuine user’s device while communicating covertly with the C2 network.
Future Impact and Trends
The future response to residential proxy networks will likely intensify along several vectors. Firstly, legislative and regulatory bodies may face increased pressure to create clearer frameworks defining the liability of service providers whose SDKs are used to compromise end-user devices without explicit, informed consent. While IPIDEA operated under the guise of a VPN, the mass installation via trojanized apps bypasses typical user agency.
Secondly, the development community needs to prioritize tamper-proofing mechanisms within SDKs. The reliance on SDKs to propagate the proxy capability across hundreds of distinct applications suggests that the operators may have focused efforts on embedding the malicious code deeply within the build pipeline, making post-distribution detection more challenging. Future security standards for mobile application development may need to mandate deeper runtime verification of third-party libraries.
Finally, this event will likely spur further development in advanced traffic analysis focused on IP address reputation scoring. Traditional firewall rules based on known malicious IPs are insufficient against residential proxies, as the exit IPs appear legitimate. Security tooling must evolve to analyze session behavior—such as a single residential IP engaging in multiple, disparate, high-risk activities (e.g., credential stuffing followed immediately by scraping a financial site)—to infer that the IP is compromised, regardless of its surface-level legitimacy.
While the immediate infrastructure disruption of IPIDEA is a success, the underlying monetization of compromised residential IPs remains a lucrative proposition for cybercriminals. The industry must anticipate the emergence of successor networks, likely with refined obfuscation techniques and more appealing, seemingly legitimate front operations. The current focus shifts now to digital forensics on the disclosed SDKs and tracking the financial flows associated with the nineteen alleged proxy businesses to potentially uncover the human element behind the infrastructure. Until then, users must heed the warning: if a service seems too good to be true—especially if it involves "earning" money by sharing bandwidth—it is almost certainly compromising their digital security.