The contemporary digital landscape is defined by an inescapable reality: security breaches are not a matter of if, but when. This fundamental shift in perception has catalyzed a necessary evolution in organizational security philosophy, moving away from legacy, perimeter-centric defenses toward a holistic concept known as cyber resilience. Cyber resilience encapsulates an organization’s complete capacity to anticipate emerging adversarial tactics, absorb the inevitable impact of an active intrusion, execute swift and precise containment measures, and ultimately restore critical business operations with minimal degradation to service continuity. The relentless sophistication of modern threat actors—leveraging automation, zero-day exploits, and increasingly intricate social engineering—has rendered purely reactive security postures obsolete. Relying solely on prevention, which inherently assumes perfection, is a recipe for catastrophic failure when that perimeter inevitably yields. Therefore, the imperative across all industry sectors is the adoption of deeply proactive strategies fundamentally centered on resilience.
The Erosion of Traditional Security Paradigms
For decades, cybersecurity investment was heavily weighted toward preventative measures: firewalls, antivirus signatures, and rudimentary access controls. While these layers remain foundational, they are demonstrably inadequate against today’s advanced persistent threats (APTs) and fileless malware. Industry analysis consistently reveals that the dwell time—the period between initial system compromise and successful detection—remains alarmingly high, often stretching into weeks or months. During this window, attackers conduct reconnaissance, elevate privileges, and establish deep persistence mechanisms, transforming a potential security event into a systemic crisis.
This failure of prevention highlights a critical industry implication: true organizational security is measured not by the number of attacks blocked, but by the velocity of detection and the efficacy of response once the boundary is crossed. This necessitates a platform approach that transcends siloed tools. The market is increasingly demanding integrated solutions capable of merging Security Information and Event Management (SIEM) functions—log aggregation, correlation, and compliance reporting—with Extended Detection and Response (XDR) capabilities, which focus on endpoint and workload telemetry for deeper contextual threat hunting.
Defining Resilience: Beyond the Firewall
Achieving genuine cyber resilience demands a strategic framework that operates continuously across the entire security lifecycle. It requires a paradigm shift from managing vulnerabilities in isolation to managing the organization’s ability to function under duress. This preparedness hinges upon several interconnected, proactive pillars that must be operationalized within security frameworks:
- Continuous Observability and Contextual Awareness: Security teams must possess an uninterrupted, holistic view across the entire IT estate—endpoints, cloud infrastructure, network traffic, and identity management. This visibility must be rich enough to provide context, enabling analysts to distinguish benign anomalies from nascent attack patterns.
- Real-Time Threat Correlation and Prioritization: Given the sheer volume of security data generated daily, automated systems are essential for sifting through noise to identify high-fidelity alerts. Effective resilience requires correlation engines capable of connecting disparate events across time and geography to map out an attacker’s complete kill chain.
- Automated Containment and Remediation: Waiting for human intervention during a fast-moving attack often means conceding the advantage to the adversary. Resilience demands the capacity for pre-defined, automated responses—such as isolating an infected host, revoking temporary credentials, or terminating malicious processes—executed within seconds of confirmed threat identification.
- Proactive Security Hygiene and Posture Management: Resilience is built on a foundation of strong baseline security. This includes rigorous vulnerability scanning, patch management enforcement, configuration auditing, and ensuring adherence to established security policies (e.g., least privilege). Weak hygiene provides the easy footholds attackers exploit.
- Adaptability and Feedback Loops: The threat landscape is dynamic. A resilient architecture must incorporate mechanisms for rapid ingestion of new threat intelligence and translate that intelligence into immediate adjustments in detection rules and response playbooks, ensuring defenses evolve faster than attack techniques.
Operationalizing Resilience: The Role of Unified Platforms
The challenge for security architects is implementing these complex strategies using disparate, often proprietary tools that fail to communicate effectively. This fragmentation introduces latency and blind spots—the very antithesis of resilience. This is where integrated, open-source security platforms, such as Wazuh, offer a compelling proposition by unifying previously disparate functions into a cohesive operational ecosystem.
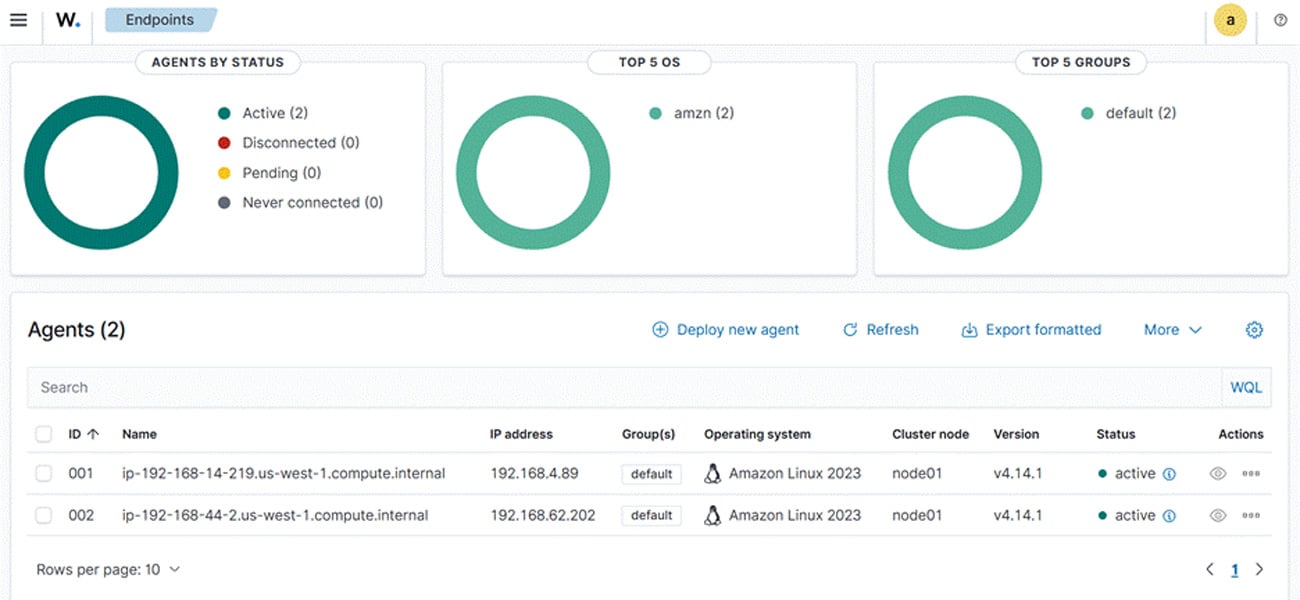
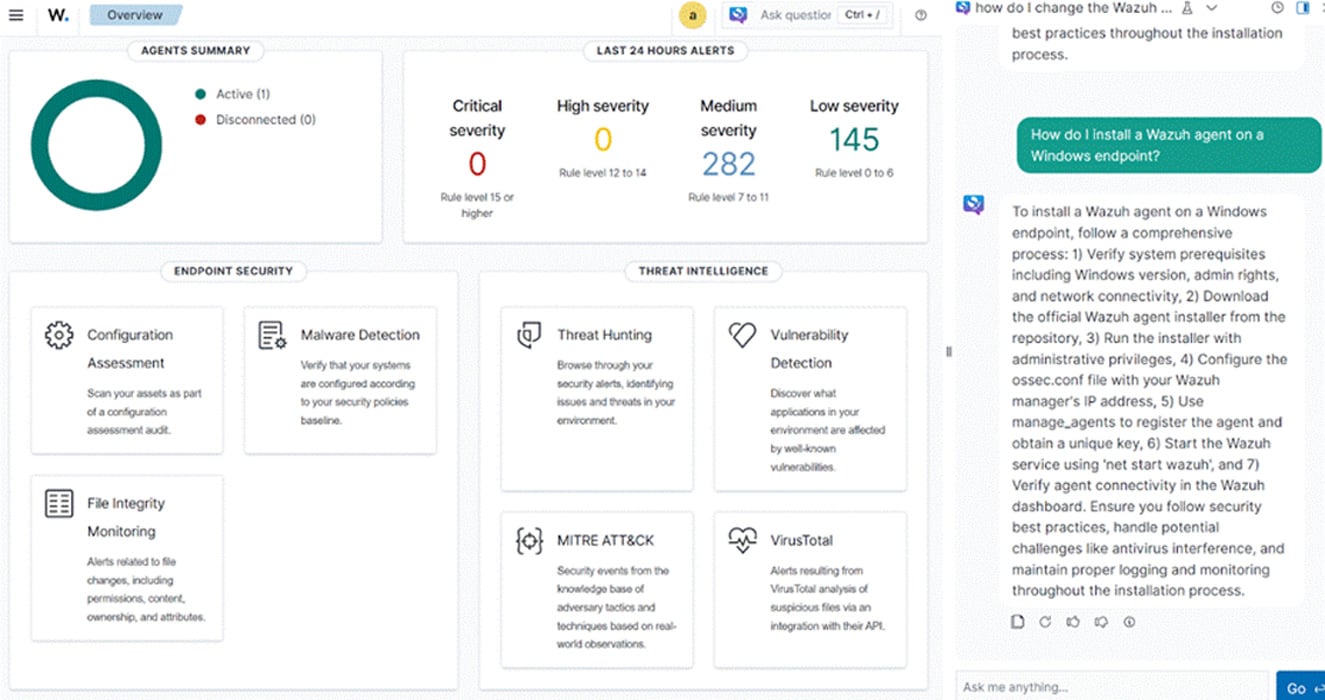
Wazuh, functioning as a unified SIEM/XDR engine, directly addresses the architectural limitations of reactive defenses by embedding proactive capabilities into the core security workflow. Its strength lies in its distributed agent architecture combined with centralized correlation, which provides the necessary deep telemetry for resilience.
Centralized Visibility and Agent-Based Telemetry
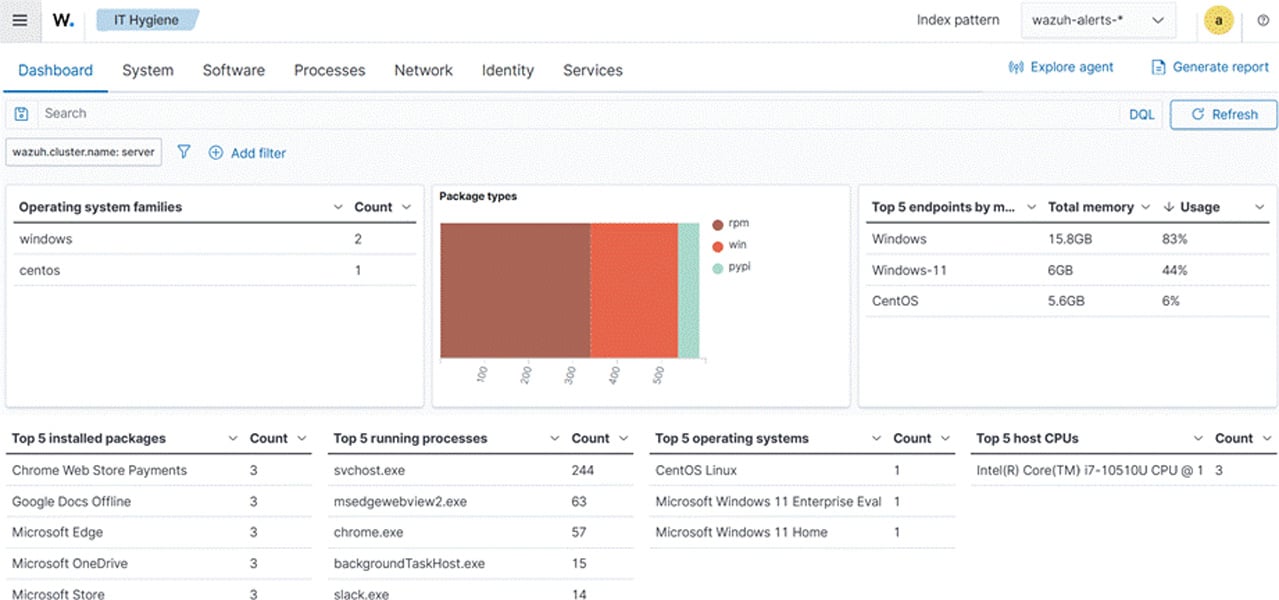
Wazuh’s core function involves deploying lightweight agents across endpoints, servers, and cloud workloads. Unlike simple log forwarders, these agents perform crucial local security functions: file integrity monitoring (FIM), security event logging (e.g., Windows Event Logs, Linux Auditd), active response capabilities, and vulnerability detection. This data is streamed back to the central manager, where it is correlated against global threat intelligence feeds and established baselines.
For an organization striving for resilience, this means achieving "single-pane-of-glass" observability across heterogeneous environments. When a lateral movement attempt begins on an aging Linux server, the agent detects the unusual execution of a system binary, while simultaneously, the central engine correlates that event with a failed login attempt reported by the identity provider (IdP) logs. Without this unified view, these two indicators might remain siloed, appearing as low-priority noise. With Wazuh, they coalesce into a high-severity incident mapping to the initial stages of a recognized attack chain.
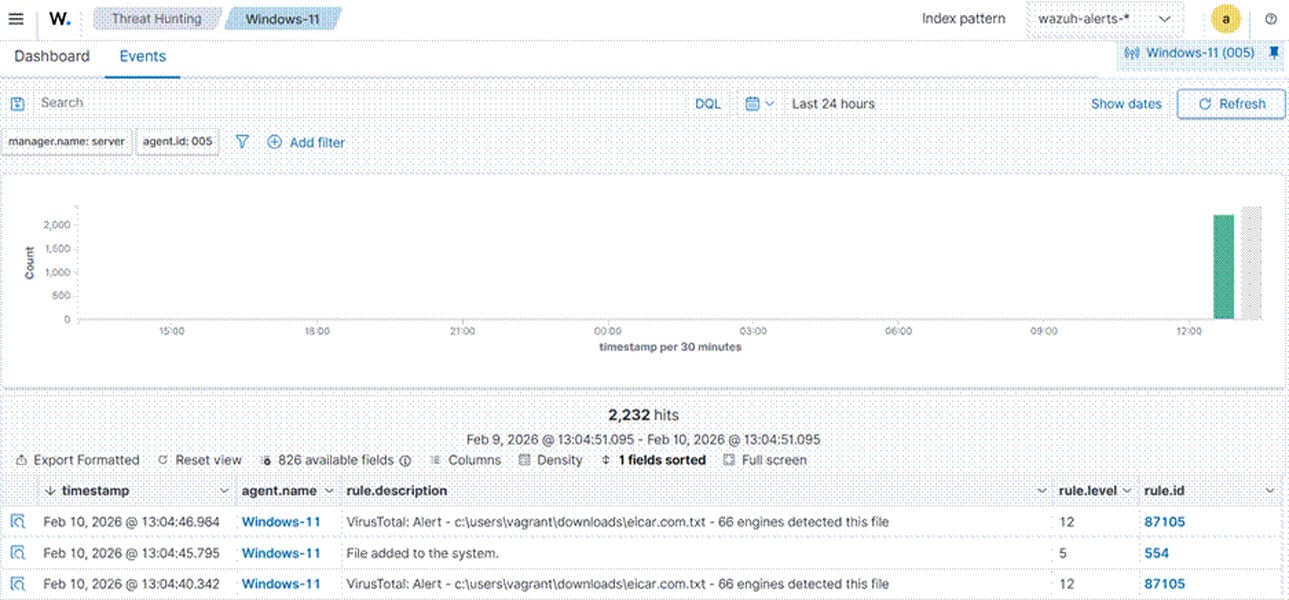
Real-Time Threat Detection Through Behavior Analysis
Moving beyond signature-based detection, resilience requires behavioral anomaly detection. Wazuh leverages rule engines and machine learning capabilities to establish normal operating parameters for assets. For example, monitoring the typical process execution chain on a database server. If an attacker compromises the server and attempts to use PowerShell or obscure scripting languages—processes rarely seen in a legitimate database maintenance context—the system flags this deviation immediately.
Furthermore, the platform supports Security Posture Assessment (SPA). This proactive function continuously audits configurations against industry best practices (like CIS benchmarks) or internal policy standards. Identifying that a critical cloud storage bucket is publicly accessible before an attacker exploits it is a prime example of resilience built into the system’s continuous assessment cycle, rather than waiting for an external audit or a public breach notification.
Automated Response and Orchestration
The speed of modern attacks necessitates automated response mechanisms integrated directly with detection logic. Wazuh’s Active Response module allows security engineers to pre-define actions triggered by specific alert severity or threat type.
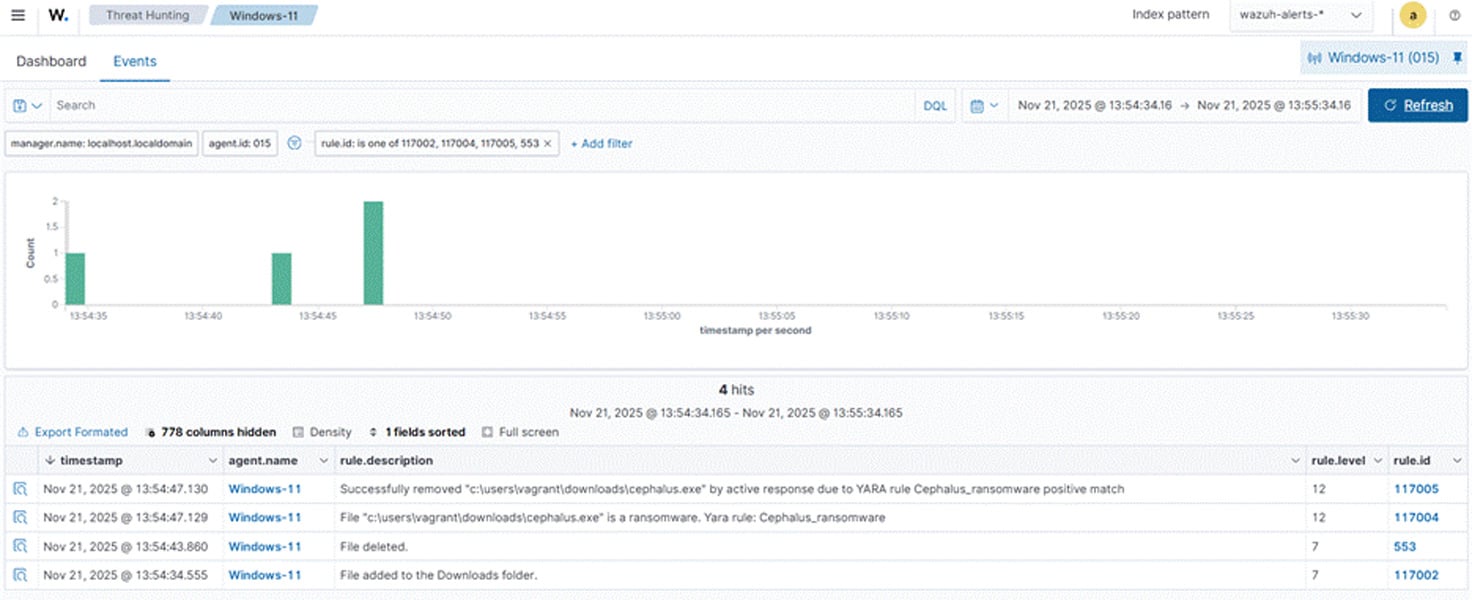
Consider a scenario where an endpoint agent detects malware attempting to communicate with a known Command and Control (C2) server IP address identified in recent threat feeds. A resilient configuration within Wazuh can be set to:
- Immediately isolate the affected host from the main network segment (network quarantine).
- Force a system reboot or initiate an automated malware scan/cleanup script via the agent.
- Generate a high-priority ticket in the Security Orchestration, Automation, and Response (SOAR) platform, enriching it with all contextual data gathered by the Wazuh manager.
This tiered, immediate response minimizes the attacker’s window of opportunity to exfiltrate data or deploy ransomware across the network, effectively containing the incident at the earliest possible stage.
Industry Implications and Expert Analysis
The adoption of resilient frameworks, powered by platforms like Wazuh, carries significant implications for organizational governance and financial liability. Regulators globally (e.g., in finance, healthcare, and critical infrastructure sectors) are increasingly demanding evidence not just of preventative controls, but of demonstrated recovery capabilities. A CISO can no longer simply state they have a firewall; they must demonstrate measurable mean time to detect (MTTD) and mean time to respond (MTTR).
From an expert analytical perspective, the open-source nature of Wazuh provides a crucial advantage in maintaining long-term resilience. Vendor lock-in in security solutions often stifles the agility required to adapt to novel threats. Because Wazuh is open source, organizations are not beholden to a vendor’s roadmap for feature development or vulnerability patching. This transparency allows security teams to inspect the engine, customize rulesets precisely to their unique business logic, and integrate custom detection modules developed in-house or sourced from the community. This flexibility ensures the security controls can evolve symbiotically with the rapidly changing business environment and threat landscape.
Future Impact and Evolving Threat Vectors
Looking ahead, cyber resilience will become increasingly intertwined with operational technology (OT) and the burgeoning Internet of Things (IoT) environments. These environments are notoriously difficult to secure due to legacy systems, infrequent patching cycles, and a historical lack of security focus. Future resilience strategies must account for non-standard protocols and low-power devices. Platforms capable of extending deep telemetry and response capabilities into these previously dark corners of the network—as modern XDR platforms are beginning to do—will define the next generation of cyber defense.
Furthermore, the integration of Generative AI in threat generation (e.g., crafting highly personalized spear-phishing campaigns or rapidly generating polymorphic malware) means that the speed of automated defense must accelerate exponentially. Resilience will rely heavily on platforms that can leverage AI/ML not just for detection, but for automated playbook generation and self-healing capabilities, minimizing the human element in the critical first minutes of an incident.
Conclusion: Sustained Defense Through Unified Architecture
Cyber resilience is the pragmatic acceptance that breaches are inevitable and shifts the focus to survival and rapid restoration. It moves beyond the static controls of prevention toward a dynamic state of continuous vigilance, rapid detection, coordinated response, and ongoing adaptation. Relying on a fragmented collection of point solutions guarantees blind spots and unacceptable response latency. Wazuh consolidates the critical functions of threat detection (SIEM/XDR), automated enforcement, and continuous security posture evaluation into a single, extensible, and community-driven platform. This unified approach empowers organizations to transition from perpetually reacting to inevitable failures toward establishing a sustainable, resilient operational posture capable of weathering the modern threat environment.
To explore the depth of this unified security framework and integrate these resilience capabilities into your infrastructure, review the extensive Wazuh documentation and engage with the vibrant professional community driving its continuous innovation.
This content is provided through a partnership with Wazuh.