The notorious ShinyHunters extortion collective has publicly claimed responsibility for a significant data breach targeting Odido, one of the Netherlands’ preeminent telecommunications providers. This alleged infiltration has reportedly yielded millions of customer records, thrusting the Dutch digital infrastructure back into the international spotlight regarding data security resilience. Odido, which services a vast swathe of the Dutch population with integrated mobile, broadband, and television offerings, confirmed an initial security incident in mid-February, marking a critical juncture in their operational security posture.
The timeline of the incident, as detailed by Odido, points to unauthorized access occurring on February 7th, with the scope of the compromise affecting the company’s customer contact system. While Odido moved swiftly to disclose the breach on February 12th and implement containment measures, the extent of the pilfered data remains a central point of contention between the company and the threat actors. Crucially, Odido asserted early in its investigation that highly sensitive data—including Mijn Odido account credentials, detailed call logs, precise location data, comprehensive billing information, and digitized identity documentation scans—remained secure and untouched by the intrusion.
However, the profile of the exposed data, while stopping short of complete financial or authentication details, is still deeply concerning. According to the telecom operator, the compromised records are granular and customer-specific, potentially encompassing full names, residential addresses, postal codes, contact mobile numbers, unique customer identification numbers, associated email addresses, IBANs (International Bank Account Numbers), dates of birth, and, alarmingly, partial identification details such as passport or driver’s license numbers along with their expiration dates. Local reporting at the time suggested the breach impacted approximately 6.2 million individual customers, a staggering figure for a nation the size of the Netherlands.
In response to the confirmed intrusion, Odido initiated standard regulatory protocols, formally notifying the Autoriteit Persoonsgegevens (the Dutch Data Protection Authority), and immediately revoked the attackers’ access pathways. Furthermore, the organization engaged third-party cybersecurity forensics specialists to conduct a thorough incident response and remediation analysis. When pressed for details regarding attribution or potential ransom demands—a hallmark of extortion campaigns—Odido maintained a tight-lipped stance, citing the integrity of the ongoing internal and external investigations.
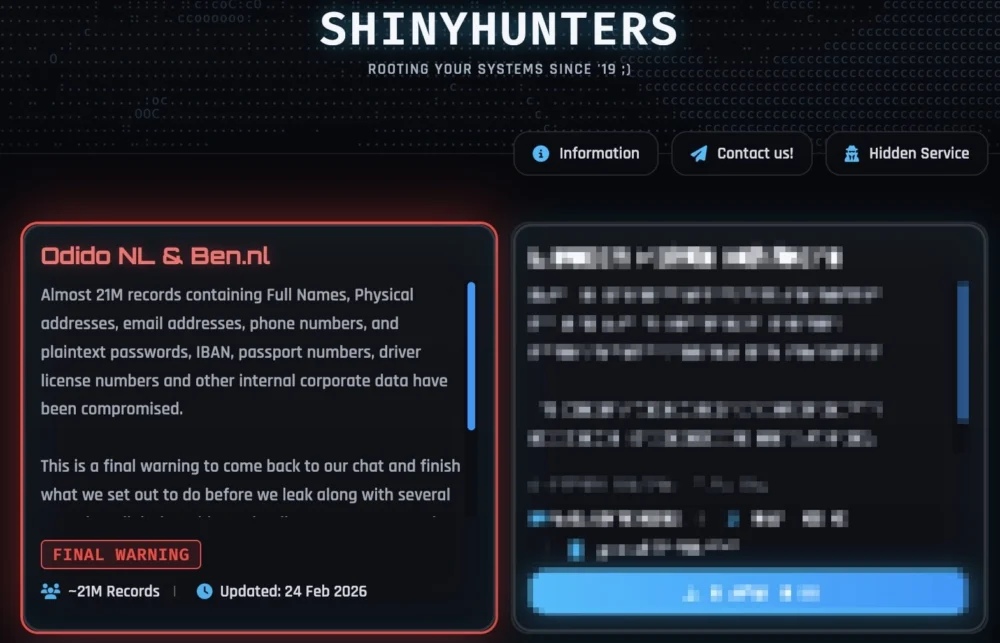
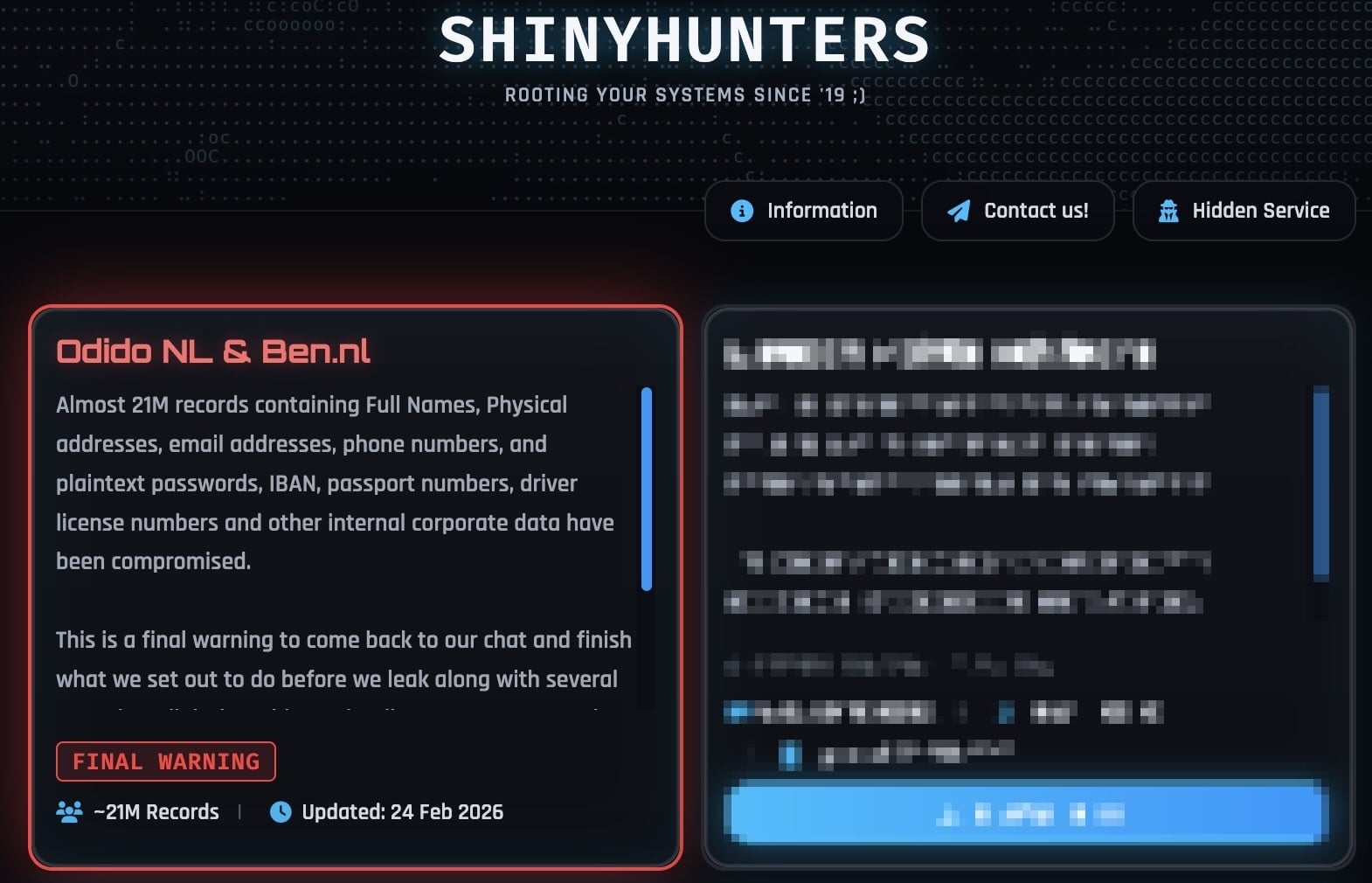
The narrative shifted when ShinyHunters decided to bypass corporate silence, adding Odido to their dedicated dark web leak site. The group claims possession of nearly 21 million records, an assertion that either implies a larger scope than initially disclosed by Odido or encompasses data duplications and peripheral information related to the initial set of compromised records. An image captured from the group’s leak page explicitly lists Odido, providing visual confirmation of their intent to exploit the exposed data.

Adding further gravity to their claim, ShinyHunters communicated directly, asserting that the stolen cache extends beyond customer personal identifiable information (PII) to include sensitive internal corporate data and, critically, plaintext user passwords. This latter claim directly contradicts Odido’s initial assurances regarding the exclusion of authentication credentials. The gang issued a pointed ultimatum on their leak platform, employing typical scare tactics: "This is a final warning to come back to our chat and finish what we set out to do before we leak along with several annoying (digital) problems that’ll come your way… Make the right decision, don’t be the next headline. You know where to find us."
Odido’s response to these specific allegations has been a firm denial, reiterated in subsequent statements, emphasizing that core security elements like user passwords, detailed call metadata, social security numbers (BSN in the Dutch context), and full billing records remain outside the scope of the breach. This discrepancy in data scope—between the publicly stated minimum by the victim and the maximum claimed by the attacker—is a common feature in modern extortion scenarios, often designed to maximize pressure on the compromised entity.
The Broader Context of ShinyHunters’ Campaign
The Odido incident is not an isolated event but rather a continuation of ShinyHunters’ highly active and aggressive campaign targeting high-profile entities globally. In recent weeks, this group has associated itself with numerous substantial data compromises across diverse sectors. Noteworthy recent targets include major North American entities like Panera Bread (where the actual impact was later revised upwards to 51 million accounts), the fintech platform Betterment, the entertainment giant SoundCloud, luxury brand Canada Goose, the adult content platform PornHub, and the extensive Match Group portfolio, which encompasses dating giants such as Tinder, Hinge, and OkCupid.
This breadth of targets suggests a sophisticated, industrialized approach to cyber extortion, capable of exploiting vulnerabilities across multiple technology stacks and geographic regions. An analysis of ShinyHunters’ methodology reveals a distinct preference for exploiting weak identity and access management controls, often leveraging sophisticated social engineering techniques to gain initial footholds.
Specifically, a significant portion of their recent success has been attributed to highly targeted voice phishing, or "vishing," campaigns aimed at compromising Single Sign-On (SSO) environments utilized by major tech providers like Google, Microsoft, and Okta. In these complex attacks, threat actors pose as internal IT support staff, engaging employees over the phone. Through impersonation, they manipulate victims into voluntarily entering their primary credentials and, crucially, their Multi-Factor Authentication (MFA) codes onto meticulously crafted phishing portals that mirror legitimate corporate login screens. This circumvents traditional MFA defenses by tricking the user into providing the time-sensitive token directly to the attacker.
More recently, the group has reportedly adapted its tactics to incorporate "device code vishing," a technique that exploits the OAuth 2.0 device authorization grant flow. This advanced method allows attackers to target and compromise Microsoft Entra ID (formerly Azure Active Directory) authentication tokens. By acquiring these tokens, ShinyHunters gains the keys necessary to pivot laterally across an organization’s connected enterprise services. Once an SSO account is hijacked, the attackers gain potential access to a vast ecosystem of integrated cloud services, including Salesforce, Microsoft 365 suites, Google Workspace, SAP environments, communication platforms like Slack and Zendesk, and data repositories such as Dropbox and Atlassian products. The Odido breach, while seemingly focused on customer records, may well have originated from a similar identity-centric compromise within their operational infrastructure.

Industry Implications and Expert Analysis
The Odido incident provides a textbook example of the cascading risks associated with poorly segmented customer databases, even when core financial data is purportedly secured. The exposure of names, addresses, dates of birth, and partial ID numbers creates a rich profile ripe for follow-on attacks, such as targeted spear-phishing, account takeover attempts (using the partial ID data as a secondary verification factor), and sophisticated identity fraud.
From an industry perspective, the consistent success of ShinyHunters underscores a critical failure in enterprise security architecture: the over-reliance on human vigilance to counter advanced social engineering. Experts in identity security emphasize that while technological defenses like robust MFA are vital, they are insufficient against adversaries skilled in exploiting the human element, particularly in high-pressure, remote-work environments where internal IT communications can be more easily spoofed.
The divergence between Odido’s stated minimal impact and ShinyHunters’ maximal claims highlights the inherent information asymmetry in post-breach scenarios. Security firms often advise organizations to conduct forensic analysis to definitively map the scope of data exfiltration, as initial attacker claims are frequently inflated for negotiation leverage. However, the mere presence of plaintext passwords, if confirmed, suggests a failure in data handling protocols far more serious than the unauthorized access to the customer contact system itself. Passwords, even if weakly hashed, represent a long-term liability that can be cracked offline and reused across other services, given the prevalence of credential stuffing attacks.
Furthermore, the regulatory environment in the EU, governed by GDPR, places severe obligations on data controllers like Odido. Even if only PII is exposed, the potential for widespread identity theft and subsequent regulatory fines necessitates transparency and robust remediation. The swift involvement of the Dutch DPA signals that regulatory scrutiny will be intense, focusing not just on the initial intrusion vector but also on the adequacy of the controls protecting the specific customer contact system that was breached.
Future Impact and Security Trends
The Odido breach, framed by the activities of ShinyHunters, illuminates several emerging trends that security architects must confront:
-
The Persistence of Identity-Centric Attacks: The continued emphasis on vishing and device code abuse demonstrates that attackers view SSO platforms as the highest-value targets. Organizations must move beyond standard MFA deployment toward phishing-resistant authentication methods, such as FIDO2 security keys, which are inherently immune to credential harvesting via phishing sites.
-
Supply Chain Risk Amplification: While the Odido breach seems internal, the nature of data exfiltration often points to third-party integrations or weak legacy systems integrated into the main environment. Telecom infrastructure is notoriously complex, often involving multiple legacy CRM and billing platforms, each presenting a potential weak link that an attacker like ShinyHunters can exploit for lateral movement.
-
The Evolving Extortion Playbook: ShinyHunters is moving beyond simple data leakage for ransom. The threat to leak "annoying (digital) problems" suggests a possible pivot toward operational disruption or even data corruption, raising the stakes from mere reputation damage to tangible business interruption. This necessitates stronger Business Continuity Planning (BCP) integrated directly with cyber incident response.
-
Data Minimization as a Security Mandate: The incident reinforces the principle of data minimization. Every piece of PII retained by a company represents a liability during a breach. For a telecom provider, the justification for storing specific identification document numbers or precise location histories must be rigorously reviewed against GDPR requirements and practical security risks. Odido’s defense hinges on the fact that some critical data was excluded; future resilience depends on reducing the amount of data available to steal in the first place.
Ultimately, the digital confrontation between Odido and ShinyHunters serves as a potent warning to the critical infrastructure sector across Europe. As threat actors refine their social engineering techniques to defeat modern technical safeguards, organizational resilience will increasingly depend on the depth of defense-in-depth strategies, rigorous employee training against advanced social engineering, and a commitment to shedding redundant or unnecessary customer data. The cost of failing to secure the human layer, as demonstrated by this high-profile Dutch incident, continues to rise exponentially.