A sophisticated and concerning trend in contemporary cyber warfare involves the calculated exploitation of the legitimate Open Authorization (OAuth) redirection mechanism. Security researchers have identified threat actors systematically abusing the standard error handling within the OAuth 2.0 protocol to successfully circumvent established email and browser-based anti-phishing defenses. This technique allows adversaries to steer unsuspecting users directly into environments controlled by malicious infrastructure, facilitating the delivery of advanced persistent threats (APTs) and malware payloads.
The observed campaigns demonstrate a high degree of technical nuance, specifically targeting high-value sectors, including government agencies and critical public-sector organizations. The initial vector relies on social engineering, where phishing lures are crafted to appear as urgent, legitimate communications. These might manifest as prompts for e-signature verification, official notices regarding Social Security information, urgent meeting invitations, mandatory password resets, or sensitive financial or political alerts. Crucially, embedded within these deceptive messages are specially crafted OAuth redirect Uniform Resource Locators (URLs). In an effort to further obfuscate their activities and bypass traditional static analysis filters, attackers have occasionally concealed these malicious URLs within seemingly innocuous document formats, such as embedded links within PDF files.
The Mechanics of Redirect Abuse
To understand the severity of this exploit, one must appreciate the intended function of OAuth. OAuth is the industry-standard protocol used by applications to gain delegated, scoped access to user resources held by an identity provider (IdP), such as Microsoft Entra ID (formerly Azure Active Directory). An application registers with the IdP and uses the protocol flow to request tokens on behalf of a user.

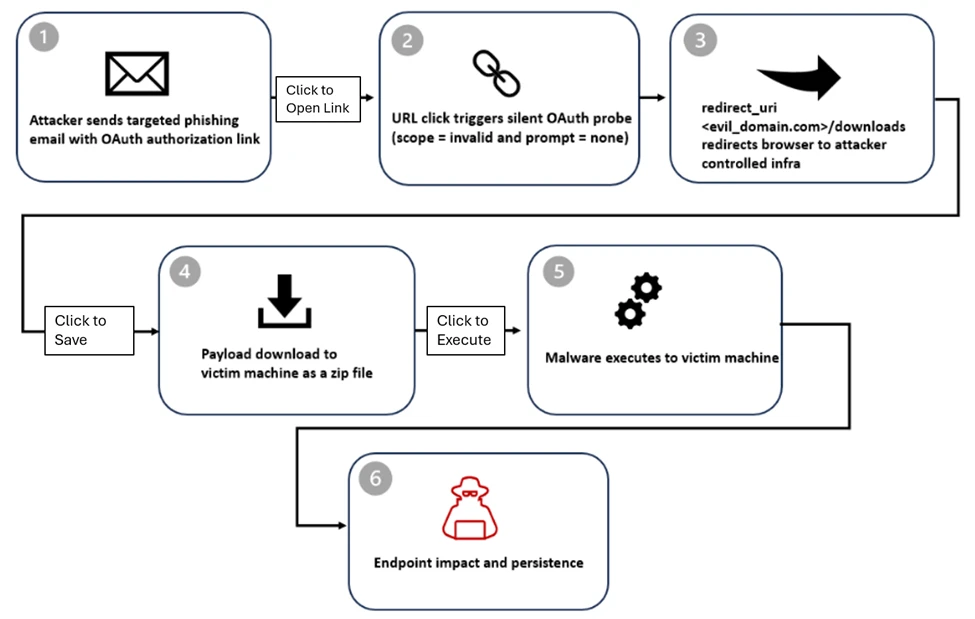
In the specific attack pattern documented by security analysts, threat actors first establish an illicit presence by registering their own malicious OAuth applications within an identity tenant under their control. The critical configuration step involves setting the redirect_uri parameter within the application registration to an endpoint under the attacker’s command structure.
The core ingenuity of the attack lies in intentionally provoking an error state within the authorization request. While the initial URL presented to the user appears structurally identical to a standard, benign authorization request directed at the legitimate IdP endpoint (e.g., Entra ID), the attackers manipulate the parameters sent during the request. Specifically, they invoke the endpoint with parameters designed to enforce silent authentication—using directives like prompt=none—while simultaneously requesting an invalid or nonexistent authorization scope. This combination of constraints ensures that the IdP cannot fulfill the request interactively or successfully grant access.
According to the established OAuth specification, when an identity provider encounters such an unresolvable authorization error, it is mandated to redirect the user agent back to the pre-configured redirect_uri. Because the attacker controls this URI, the user is seamlessly shunted from a seemingly trusted Microsoft domain directly into the adversary’s infrastructure. This process effectively hijacks the implicit trust users place in the authorization handshake process itself.
Escalation Paths: Phishing and Session Hijacking
Once redirected, the user faces one of two primary objectives. In scenarios focused on credential harvesting, the destination is a sophisticated phishing page. These pages are frequently powered by advanced attacker-in-the-middle (AiTM) frameworks, such as EvilProxy or similar toolsets. These frameworks are designed to mimic the genuine login interface of the targeted service with high fidelity.
A particularly insidious refinement noted during these investigations involves the manipulation of the state parameter within the OAuth request. In legitimate flows, the state parameter is a security mechanism used to maintain state between the request and the callback, often used to prevent Cross-Site Request Forgery (CSRF). Here, the attackers repurpose this field to auto-populate the victim’s email address into the username field of the phishing credential box. This small detail significantly enhances the perceived legitimacy of the login prompt, reducing user suspicion and increasing the likelihood of successful credential submission. If the victim enters their credentials, the AiTM framework intercepts the subsequent session cookies, potentially bypassing even robust Multi-Factor Authentication (MFA) measures that rely solely on the initial authentication phase.
The Malware Delivery Chain
In parallel attack tracks, the redirection leads not to a credential harvester, but directly to a malware payload delivery system. The malicious redirect URI is configured to point to a specific path, often designated as /download. Upon arrival, this path automatically initiates the download of a compressed archive, typically a ZIP file.
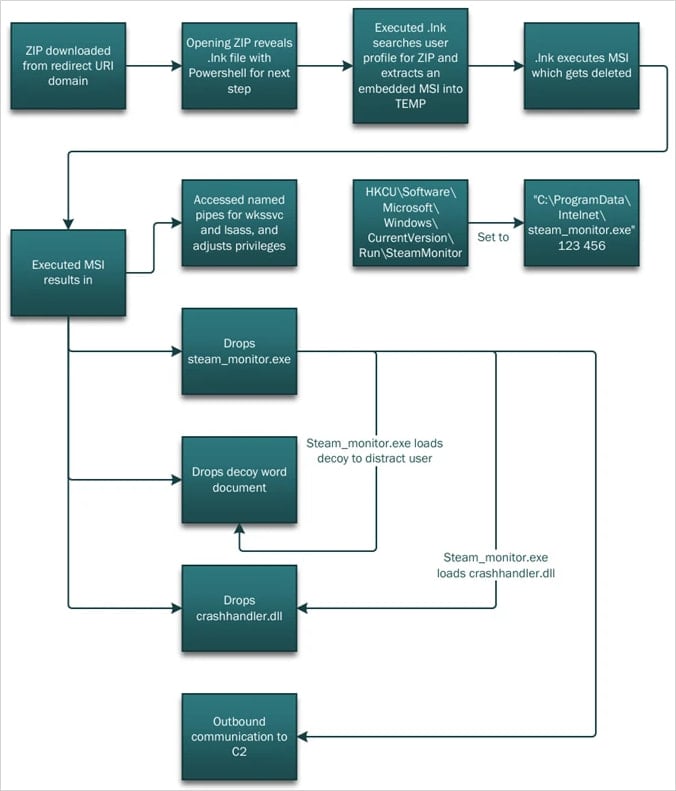
This archive is specifically engineered to bypass static file scanning, containing elements like malicious Windows Shortcut files (.LNK) alongside tools associated with HTML smuggling techniques. The use of .LNK files is a well-known technique to launch Windows commands indirectly, thereby avoiding direct execution of scripts.
When a victim opens the .LNK file, the initial action is the silent invocation of PowerShell. This scripting engine does not immediately deploy the final payload. Instead, it executes a reconnaissance phase on the compromised host, gathering system information necessary to ensure persistence and tailor the subsequent infection stage.
The subsequent stage leverages a highly evasive technique known as DLL side-loading. The PowerShell script extracts the necessary components for this operation. A malicious Dynamic Link Library (DLL), often named something innocuous like crashhandler.dll, is decrypted and loaded directly into the memory space of a legitimate, trusted system executable, such as stream_monitor.exe. This legitimate application is used as a host process to mask the malicious activity. While the malicious DLL executes the core malware functions—decrypting and loading the final payload (crashlog.dat) into memory—the legitimate executable simultaneously launches a decoy process or displays a benign visual element designed to distract or occupy the victim, ensuring the background activity goes unnoticed.
Industry Implications and Defense Posture
This attack methodology represents a significant evolution in identity-based threats. It moves beyond exploiting simple credential stuffing or brute-force attacks, instead targeting the fundamental trust relationship established between an application and an identity provider via a standardized protocol. For organizations relying heavily on cloud identity services like Microsoft Entra ID for access management, this vulnerability exposes a systemic weakness rooted in protocol configuration rather than a specific software bug.
The implication for security operations centers (SOCs) is profound. Traditional perimeter defenses and email gateway scanners struggle to flag these links because the initial URL resolves to a legitimate IdP domain. The malicious action only occurs after the IdP validates the request and executes the mandated error redirect. This necessitates a shift in monitoring focus from the initial email content to the subsequent user journey across identity and endpoint layers.
Expert Analysis and Future Trends:
Security architects must acknowledge that threat actors are becoming adept at weaponizing standardized protocol behaviors—a form of “living off the land” at the protocol level. The observed abuse of the scope and prompt=none parameters highlights an attacker’s deep understanding of OAuth RFC specifications, transforming error handling into an offensive capability.
Looking forward, the industry must adapt rapidly. The future of defense against these identity-centric threats lies in layered, context-aware security controls:
- Application Permission Granularity: Organizations must rigorously audit and restrict the permissions granted to all registered OAuth applications, enforcing the principle of least privilege not just for user accounts, but for the applications themselves. Any newly registered application should undergo stringent review, especially if it is configured with broad redirection capabilities.
- Conditional Access (CA) Hardening: Identity providers must enhance Conditional Access policies to analyze the context of authorization requests beyond just the user and device. CA policies should ideally flag or challenge sessions originating from an authentication flow that immediately results in an error redirect to an unapproved external domain, even if the initial request seemed valid.
- Cross-Domain Telemetry Fusion: Effective detection requires correlating signals across the entire security stack. A successful defense strategy must fuse email gateway logs (identifying the initial deceptive link), identity logs (noting the rapid authorization failure and subsequent redirect), and endpoint telemetry (detecting the download initiation and subsequent PowerShell execution). This holistic view is essential for catching the multi-stage attack chain before payload execution.
- Protocol Awareness in Sandboxing: Browser and email security solutions need enhanced capabilities to deeply inspect the intended outcome of OAuth flows. If a redirect immediately follows an invalid authorization request, the security layer should treat the resulting destination with extreme suspicion, irrespective of its domain’s immediate reputation.
The ongoing weaponization of OAuth error flows serves as a stark reminder that security vulnerabilities are not confined to coding flaws; they frequently reside in the complex interplay between established standards and real-world implementation environments. Organizations must proactively harden their identity governance frameworks to neutralize these increasingly sophisticated, protocol-level attacks.

