The foundational infrastructure of the internet, meticulously designed for operational integrity, is increasingly becoming a vector for sophisticated cyberattacks. Recent threat intelligence has illuminated a worrying trend where malicious actors are systematically abusing the special-use .arpa top-level domain, specifically leveraging the intricacies of IPv6 reverse DNS resolution, to deploy phishing campaigns that are highly effective at circumventing conventional security controls. This technique exploits the very mechanisms intended for network diagnostics, turning necessary infrastructure functions into pathways for compromise.
The Architecture of Evasion: Understanding .arpa and Reverse DNS
To appreciate the novelty of this attack, one must first grasp the role of the .arpa domain. Unlike standard, user-facing TLDs such as .com or .org, .arpa is reserved strictly for internet infrastructure tasks. Its primary utility lies in supporting reverse DNS lookups—the process of resolving an IP address back to a human-readable hostname. This functionality is crucial for network diagnostics, logging, and ensuring proper email server authentication.
For IPv4 addresses, the resolution path traverses the in-addr.arpa zone. For the more expansive IPv6 addressing scheme, the corresponding structure is ip6.arpa. In both cases, the IP address is converted into a specialized hostname format, written in reverse octets (or nibbles for IPv6), and appended to the appropriate .arpa domain. For instance, resolving the IPv4 address 192.178.50.36 involves querying the PTR record for 36.50.178.192.in-addr.arpa. A similar, albeit more complex, process applies to the much longer IPv6 addresses, utilizing the ip6.arpa suffix. These lookups typically resolve to a canonical hostname associated with the network block or service provider.
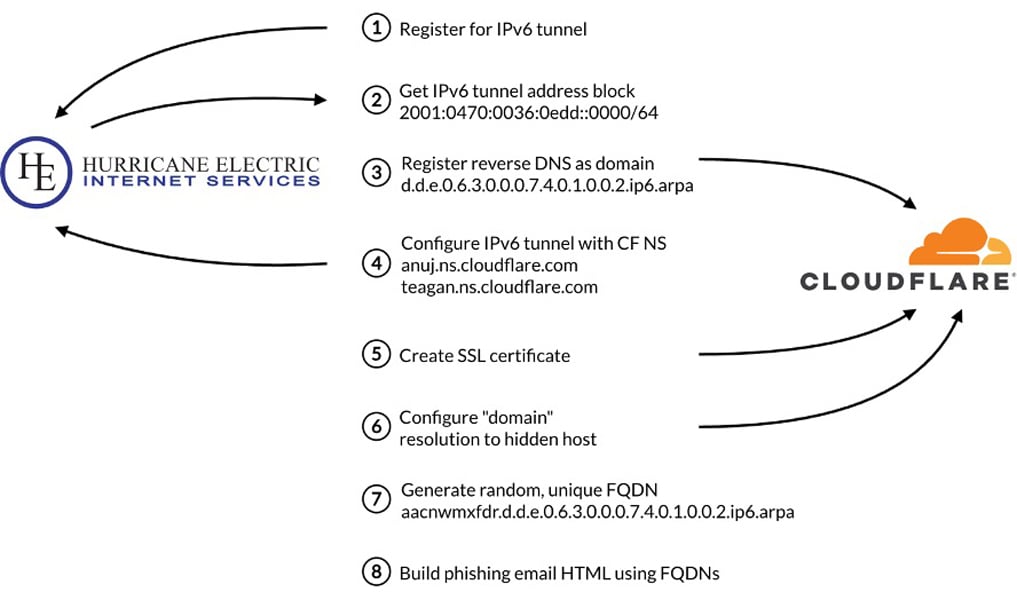
The core of the current evasion strategy hinges on gaining control over the delegated DNS zone associated with a specific range of IPv6 addresses. While an organization typically delegates control over the PTR records within their assigned IP space, attackers have discovered loopholes within certain DNS management platforms. By acquiring—often via ephemeral tunneling services—a block of IPv6 addresses, threat actors gain administrative control over the corresponding ip6.arpa reverse zone for that range.
The Technical Pivot: A-Records in Infrastructure Zones
The critical deviation from expected behavior occurs at this stage. In standard reverse DNS operations, the expectation is that queries against the ip6.arpa structure will yield only Pointer (PTR) records, confirming the associated hostname. However, security researchers have found that compromised or permissive DNS providers allow these infrastructure zones to host non-standard record types.

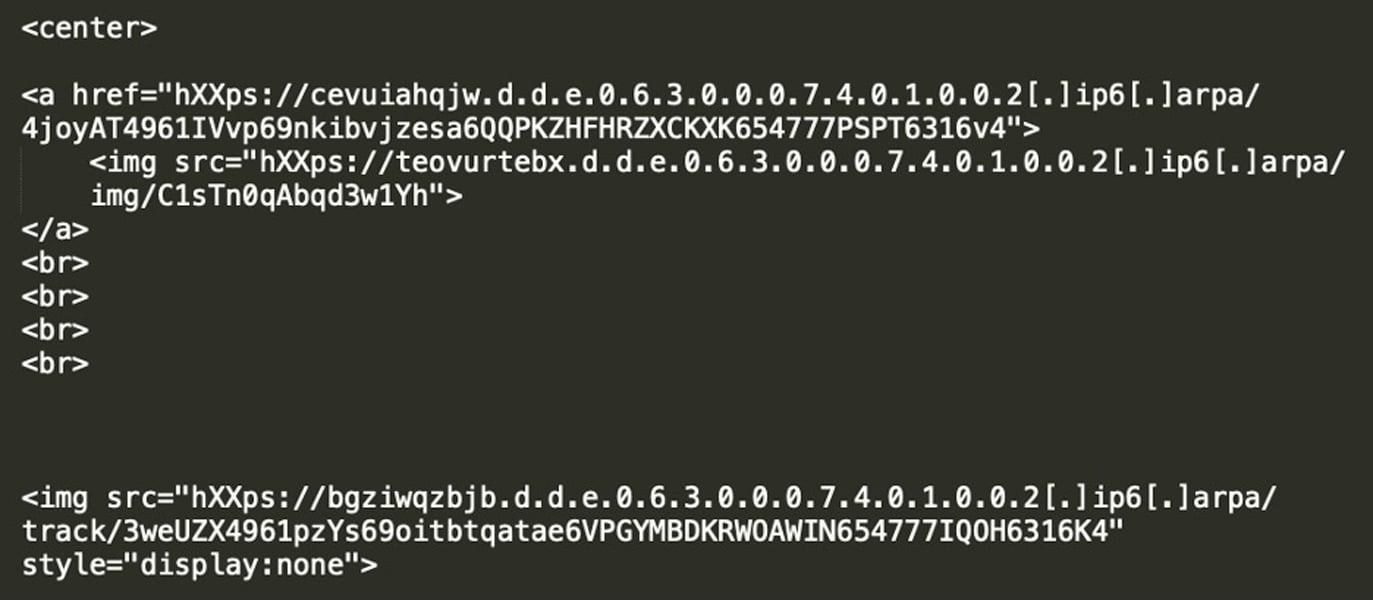
Instead of merely setting correct PTR records, the attackers are creating Address (A) records within their controlled ip6.arpa subzones. These A records point the reverse-engineered hostname directly to servers hosting the malicious payload—the phishing landing pages.
This creates a situation where a seemingly innocuous, infrastructure-related domain name is actually resolving to an active, attacker-controlled web resource. The sophisticated nature of the attack lies in how this is presented to the end-user and, more importantly, to automated security scanning tools.
Obfuscation and Reputation Laundering
The primary objective of this technique is stealth. Traditional domain reputation systems, email security gateways (ESGs), and endpoint detection and response (EDR) solutions rely heavily on analyzing the FQDN (Fully Qualified Domain Name) presented in an email or link. They check domain age, registration data (WHOIS), historical threat scores, and whether the domain is known to serve malware.
The abuse of .arpa sidesteps these checks entirely for several reasons. First, the .arpa TLD is inherently whitelisted or treated with extreme leniency because it is vital for global internet function. Security filters are not designed to aggressively block or score domains within this zone. Second, because these are infrastructure lookups, the WHOIS records are often sparse or point toward the registrar or tunneling service, not the end attacker. Furthermore, the domains used are dynamically generated, often utilizing long strings of seemingly random hexadecimal characters derived from the IPv6 address itself (e.g., 4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa). This randomness prevents historical blacklisting.
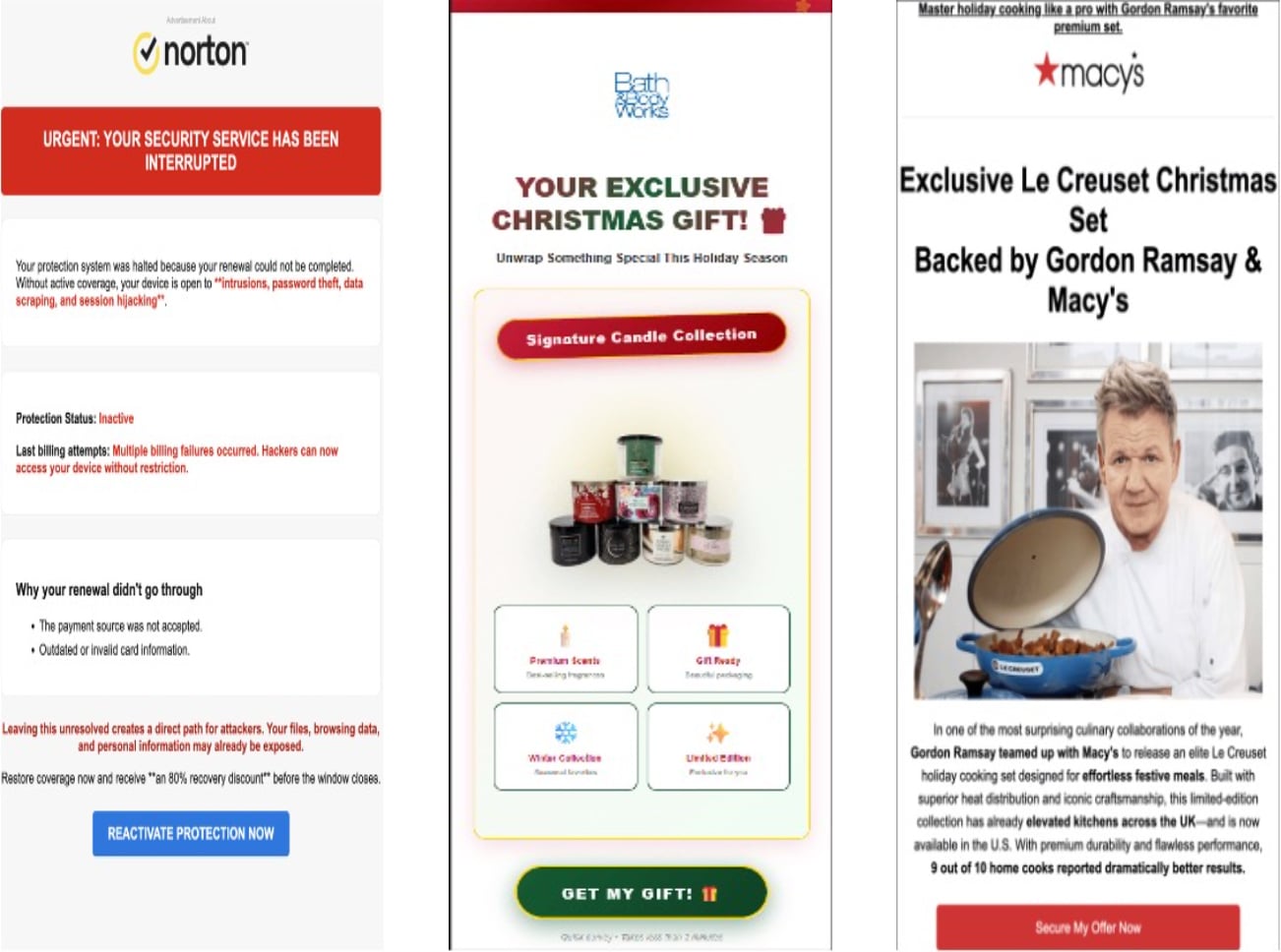
The final layer of obfuscation is deployed in the phishing email itself. Attackers embed the malicious link not as visible text, but as the source for an image or an invisible hyperlink within the email body. Crucially, the URL presented to the user is often masked. The link points to the dynamically generated .ip6.arpa address, but the visible text or the rendered image link might point to something innocuous, or the link might not be rendered in a way that exposes the full infrastructure URL to basic parsing engines. The victim only sees a seemingly benign prompt—a notification about an account update, a survey incentive, or a prize notification—leading them to click.
When the user clicks, the device initiates a DNS query to resolve the link. The resolution process, following the attacker’s configuration, leads the query through the standard DNS resolver, which ultimately queries the authoritative name servers the attacker controls within the designated IPv6 reverse zone. These name servers respond with the A record, pointing the client to the actual phishing server.
Leveraging Reputable Infrastructure for Camouflage
A significant contributing factor to the success of these campaigns is the choice of hosting providers for the authoritative name servers. Intelligence indicates that threat actors are utilizing major, reputable DNS providers—including giants like Hurricane Electric and Cloudflare—to host the zone files for their abused .ip6.arpa addresses.
This "reputation laundering" is strategic. When a security tool performs a deep inspection of the initial DNS query path, the authoritative name servers themselves appear legitimate and trusted. If the reverse DNS domain resolves to Cloudflare IPs, for instance, the tool might mistakenly assign a lower risk score to the connection, assuming the traffic is routing through a well-known Content Delivery Network (CDN) rather than a bespoke malicious endpoint. This effectively shields the true location and nature of the backend phishing infrastructure.
The entire attack chain often concludes with a Traffic Distribution System (TDS). Upon reaching the initial landing page via the .arpa resolution, the visitor is subjected to fingerprinting. The TDS analyzes environmental factors—User Agent, IP geolocation, referrer headers, and browser capabilities—to determine if the visitor is a genuine, high-value target. If the visitor is flagged as a security researcher, bot, or an invalid target, they are shunted to a benign, legitimate website, thus preventing the capture of forensic data or the successful exploitation of the payload. Only validated targets are passed through to the final credential harvesting or malware delivery stage.
Industry Implications and Defense Gaps
This exploitation of reverse DNS functionality highlights a critical vulnerability in the security industry’s reliance on traditional domain-based reputation models. The attack moves the malicious signifier away from the traditional domain name system (DNS) and into the technical metadata layer of DNS resolution itself.
For Domain Reputation Systems: Current reputation engines are heavily weighted toward scanning the root TLD and second-level domain for indicators of compromise. They are ill-equipped to handle legitimate infrastructure zones being co-opted for application-layer attacks. A fundamental shift is required toward deeper inspection of DNS query responses, including the authoritative source and the record types returned, especially for infrastructure-related queries.
For Email Security Gateways (ESGs): ESGs often perform URL unwrapping and reputation checks upon receiving an email. If the URL is hidden behind an image tag linking to a complex, dynamically generated .ip6.arpa string, the initial checks might fail to flag the threat until the user action triggers the resolution process. This means detection shifts from pre-delivery analysis to post-click behavioral analysis, which is inherently reactive.
The Ephemeral Nature of Threats: A further complicating factor is the short lifespan of these phishing links. Reports suggest these infrastructure setups are intentionally transient, remaining active for only a few days before the attackers dismantle the configuration or allow the links to expire, resulting in errors or redirection to legitimate content. This brevity severely hampers the ability of security researchers and automated threat hunting systems to gather persistent artifacts for rule creation and network defense updates.
The IPv6 Transition Context
This abuse vector is inextricably linked to the global migration towards IPv6. As organizations deploy IPv6 infrastructure, the use of ip6.arpa reverse lookups becomes more common for legitimate operational monitoring. Attackers are capitalizing on this growing complexity and the relative unfamiliarity of IPv6 security paradigms compared to mature IPv4 security standards. IPv6, by design, generates significantly longer and more complex hostnames during reverse lookups, which further aids in obscuring malicious intent when embedded in URLs.
The reliance on tunneling services to secure initial IPv6 address space acquisition also points to a failure in oversight within the allocation and management of these network blocks, even if temporary. The ease with which actors can secure routable IPv6 space and delegate its DNS control to reputable providers is a major enabler.
Advanced Evasion Tactics Observed
Beyond the core .arpa abuse, the threat actors are employing a suite of related techniques to maximize their evasion success. These supplementary methods reinforce the difficulty in tracking and blocking the campaign:
- Hijacking Dangling CNAME Records: This technique involves identifying legitimate, often aged, subdomains belonging to major organizations (government agencies, universities, large retailers) that have a Canonical Name (CNAME) record pointing to a resource that no longer exists or has been decommissioned. The attacker registers the now-available target of the CNAME record. When the original, legitimate subdomain is queried, the dangling CNAME redirects traffic to the attacker’s infrastructure, borrowing the trust associated with the primary organization’s domain name. Over 100 such instances involving major entities have been cataloged.
- Subdomain Shadowing: Related to CNAME hijacking, subdomain shadowing involves registering a domain that mimics a legitimate organization’s subdomain structure but leverages a different TLD or configuration. If a company uses
secure.legitcorp.com, an attacker might registersecure.legitcorp-update.comor similar, exploiting user inattentiveness.
The convergence of these techniques—leveraging infrastructure abuse (.arpa), reputation masking (Cloudflare/Hurricane Electric hosting), and classic domain manipulation (CNAME/shadowing)—presents a multi-layered defense challenge.
Future Trajectories and Remediation Imperatives
The weaponization of infrastructure domains signals a maturation in threat actor methodologies, moving beyond simple domain squatting to actively manipulating fundamental internet protocols. To counter this evolving threat landscape, security architecture must adapt:
Firstly, Protocol-Aware Security Analysis is paramount. Security solutions must gain deeper contextual awareness of DNS queries, differentiating between standard operational lookups and queries that result in A-records within zones reserved for reverse mapping (like ip6.arpa). Monitoring for non-PTR record creation within these zones should be treated as a high-severity anomaly.
Secondly, Enhanced Post-Click Verification: Since pre-click analysis is being consistently bypassed, security protocols must strengthen post-click monitoring. This involves isolating link resolution in sandboxes that emulate real user environments, scrutinizing the entire DNS resolution chain, and delaying full payload delivery until the resolved IP and certificate chain are thoroughly vetted, regardless of the apparent reputation of the authoritative name servers.
Finally, DNS Provider Accountability: There needs to be increased pressure on major DNS hosting services to implement stricter governance over zone file modifications for delegated infrastructure blocks, ensuring that only appropriate record types (like PTRs for reverse zones) are permitted unless explicit, audited configuration changes are made by the registered IP block owner.
The exploitation of .arpa demonstrates that the perceived security of infrastructure protocols cannot be taken for granted. As the internet continues its structural evolution, the cat-and-mouse game between defenders and attackers will increasingly focus on the obscure, technically complex corners of the network stack, demanding constant vigilance and adaptive defense strategies. The guiding principle remains: avoiding interaction with unsolicited links is the most robust defense against these highly engineered, protocol-level attacks.

