The digital security landscape is continually reshaped by the evolving tactics of malicious actors, and a recent discovery underscores a significant pivot toward leveraging highly trusted, cloud-native platforms for clandestine operations. Cybersecurity analysts have uncovered an expansive Android malware campaign that strategically weaponizes the Hugging Face platform, traditionally revered as the central hub for open-source artificial intelligence (AI), machine learning (ML), and data science collaboration. This operation utilizes Hugging Face’s robust hosting and content delivery network (CDN) infrastructure to serve thousands of polymorphic variants of a potent Android Remote Access Trojan (RAT) designed specifically for high-value credential harvesting from financial and payment applications.
Hugging Face’s reputation as a repository for cutting-edge research and legitimate software components grants it an implicit level of trust within automated security scanning environments. This trust is precisely what the threat actors are exploiting. While the platform has faced previous incidents involving the hosting of compromised or malicious AI models—a testament to the inherent risks in any open-source repository—this new campaign marks a more sophisticated abuse vector: the systematic use of its dataset feature to camouflage and distribute executable malware payloads (APKs).
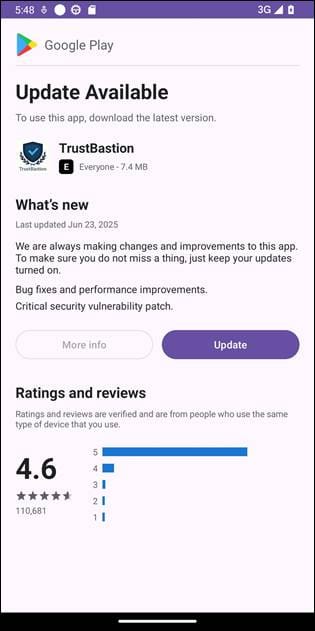
The initial infiltration vector, as detailed by researchers at the Romanian cybersecurity firm Bitdefender, relies on classic social engineering amplified by scareware tactics. Victims are first tricked into downloading a dropper application, codenamed "TrustBastion." This application masquerades convincingly as a critical security or optimization utility. Its primary lure involves aggressive, full-screen advertisements claiming the user’s device is riddled with infections, scams, or phishing vulnerabilities. By framing itself as the solution to these fabricated threats, TrustBastion gains initial user trust.

Upon installation, the deception deepens. TrustBastion immediately triggers what appears to be a mandatory system update notification, meticulously designed with visual elements that mimic the official Google Play Store interface. This critical stage bypasses standard user scrutiny because the prompt originates from an app already installed on the device, and the visual spoofing creates a sense of official necessity.
Crucially, the malware does not host the final malicious package directly on its initial landing server. Instead, the TrustBastion dropper communicates with a dedicated command-and-control (C2) infrastructure linked to the domain trustbastion[.]com. This server acts as a sophisticated intermediary, issuing a redirect that points the victim’s device directly to a specific dataset repository hosted on Hugging Face. The final, weaponized Android Package Kit (APK) is then downloaded dynamically from the Hugging Face infrastructure, leveraging the platform’s global CDN for rapid and stealthy delivery.
The Polymorphic Evasion Technique
The primary mechanism ensuring the longevity and resilience of this campaign is server-side polymorphism, a technique rarely seen deployed with such high frequency in mobile malware distribution schemes. According to the analysis, the threat actor configured the system to generate entirely new, distinct payload variants every 15 minutes. This rapid mutation rate effectively neutralizes static signature-based detection methods. As soon as a specific APK hash is identified and flagged by security vendors, the C2 server instantly pushes out a completely new, yet functionally identical, binary via the Hugging Face link.
During the investigation period, researchers observed that the initial repository hosting these thousands of variants was remarkably active, accumulating over 6,000 commits in approximately 29 days. This high volume of activity suggests automated generation and uploading processes, characteristic of a highly organized threat operation rather than opportunistic hacking. Although security researchers successfully coordinated the takedown of the initial Hugging Face repository, the operation demonstrated remarkable agility, swiftly migrating its hosting infrastructure to a new repository under the moniker "Premium Club," retaining the core malicious code while merely refreshing the visual presentation (icons) to maintain user appeal.

Deep System Compromise via Accessibility Services
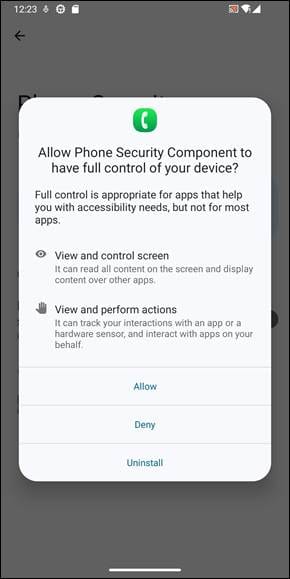
The core functionality of the undisclosed final payload—the RAT—is built around the aggressive exploitation of Android’s Accessibility Services. This feature, designed to assist users with disabilities, is notoriously abused by malware because it grants profound control over the operating system when enabled. TrustBastion cleverly frames the request for Accessibility Service permissions as an unavoidable prerequisite for its supposed security functions, often stating that such access is required to "scan for advanced threats."
Once granted, this permission transforms the compromised device into a fully controllable remote endpoint. The malware gains capabilities far exceeding typical data theft: it can inject overlay screens onto legitimate applications, capture real-time screen recordings, simulate user inputs (swipes and taps), and, critically, intercept system prompts. Furthermore, the malware implements anti-removal measures, often using the Accessibility Service hooks to block user attempts to navigate to the settings menu or directly uninstall the offending application, effectively locking the malware onto the device.
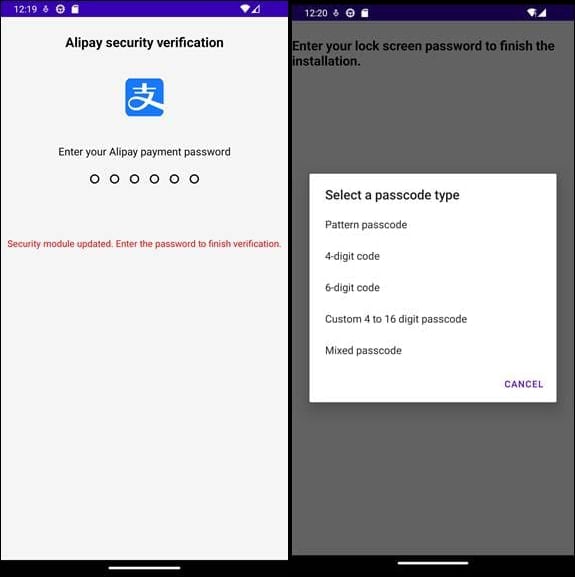
The primary objective of this specific RAT variant is financial credential harvesting. The malware actively monitors foreground applications. When a user opens a targeted financial or payment application—such as Alipay or WeChat—the malware deploys highly convincing, context-aware phishing overlays. These overlays precisely mimic the login or PIN entry screens of the legitimate application. When the user inputs their credentials or lock screen PIN into this overlay, the data is immediately captured and exfiltrated to the operators’ C2 servers. Beyond capturing active credentials, the malware also attempts to harvest the device’s persistent lock screen code, ensuring continued access even after reboots.
The continuous communication channel maintained with the C2 server is vital. It not only serves as the data siphon for stolen credentials and screen captures but also acts as a dynamic instruction set. The C2 can remotely command the RAT to execute arbitrary code, push updated configuration files, and even inject fresh, context-specific fake content into the TrustBastion shell to sustain the illusion of legitimacy and bypass further behavioral analysis.
Industry Implications: The Erosion of Platform Trust
This campaign highlights a critical vulnerability in the software supply chain paradigm, specifically concerning platforms designed for developer enablement. Hugging Face, like GitHub or other trusted cloud services, operates under the assumption that users are primarily collaborating on research and development, not engineering sophisticated malware distribution networks.
The strategic choice of Hugging Face infrastructure over traditional, easily blocked malicious hosting services offers several significant advantages to the threat actor:
- Reputation Shielding: Traffic originating from Hugging Face domains carries a significantly lower suspicion score across enterprise firewalls, security gateways, and mobile endpoint protection platforms (EPP) compared to traffic from unknown or newly registered domains.
- Scalability and Resilience: Utilizing Hugging Face’s robust, globally distributed CDN ensures high availability for the malware payload, making takedown operations a cat-and-mouse game requiring platform-specific intervention rather than simple domain blocking.
- Polymorphism Persistence: The ease of creating new "datasets" and committing frequent updates allowed the rapid generation of polymorphic payloads, bypassing behavioral heuristics that rely on tracking persistent file hashes.
This development forces a necessary re-evaluation of how "trusted" developer platforms manage content integrity. While platforms like Hugging Face are indispensable for the advancement of open AI, their infrastructure is now demonstrably attractive to adversaries looking for resilient, high-reputation endpoints to host destructive code. This blurs the line between legitimate open-source hosting and malicious staging environments, placing a greater burden on platform providers to implement stringent, context-aware content moderation.
Expert Analysis and Future Trends
From an expert security perspective, the integration of sophisticated C2 communication with rapid polymorphism and deep system exploitation (via Accessibility Services) signals the maturation of mobile financial fraud operations. These are no longer simple one-off phishing apps; they represent modular, persistent threats capable of operating undetected for extended periods.
The reliance on polymorphic generation every 15 minutes is particularly noteworthy. In traditional malware, generating new binaries requires substantial overhead. If the threat actor successfully automated the process of generating a functional, albeit slightly varied, APK and instantly committing it to a Hugging Face dataset, it implies a significant investment in developing robust, low-friction malware automation tooling. This level of automation suggests the operation is likely financially motivated and generating substantial returns, justifying the complex setup.
Furthermore, the targeting of major international payment systems like Alipay and WeChat suggests a global reach, moving beyond geographically constrained campaigns focused solely on US or European banking apps. This broad targeting increases the potential blast radius significantly.
Looking forward, we can anticipate several trends stemming from this exploit:
- Increased Platform Weaponization: Threat actors will continue to probe other high-reputation, developer-centric platforms—including code repositories, cloud storage services favored by researchers, and specialized data-sharing sites—seeking environments with low detection thresholds.
- AI-Enhanced Phishing: The malware uses basic overlay phishing, but the proximity of the host platform (Hugging Face) to cutting-edge generative AI suggests future iterations may incorporate more sophisticated, context-aware phishing dialogs generated by Large Language Models (LLMs) to trick users more effectively.
- Focus on Developer Tooling Security: Security solutions will need to pivot from solely inspecting end-user applications to actively monitoring the activity patterns within developer repositories themselves, looking for unusual file type uploads (like APKs in a data science context) or rapid, automated commit cycles.
In response to the findings, Bitdefender responsibly engaged Hugging Face, leading to the prompt removal of the offending repositories. They also released detailed Indicators of Compromise (IOCs) concerning the dropper, network C2 addresses, and package signatures to aid the broader security community in mitigation efforts.
For end-users, the lesson remains perennial but is reinforced by this novel attack vector: absolute vigilance is required when installing software outside of vetted, primary application stores. Users must meticulously review the permissions requested by any application, especially those claiming security functions that demand deep system access like Accessibility Services. If an app’s requested permissions significantly exceed its stated purpose—for instance, a "cleaner app" demanding the ability to read screen content or block settings—installation should be immediately aborted, regardless of where the app was sourced. The age of trusting infrastructure based solely on reputation is over; verification must be continuous.

