The calculus of cloud security is undergoing a fundamental shift, as evidenced by recent telemetry indicating that sophisticated exploitation of software vulnerabilities has decisively surpassed reliance on rudimentary tactics like weak credentials or simple misconfigurations for initial access to cloud environments. According to a comprehensive analysis spanning the latter half of 2025, security incident responders are increasingly identifying zero-day and newly disclosed flaws as the primary conduit for intrusion, dramatically compressing the operational window for defenders. This evolution suggests a maturing adversary landscape, one that has successfully bypassed the security hardening applied to common authentication vectors.
The data reveals a stark divergence in initial access methodologies. Bug exploits were identified as the leading cause of investigated cloud intrusions, accounting for nearly 44.5% of successful breaches. Conversely, compromised credentials—whether weak, reused, or obtained via social engineering—slid to 27% of recorded breaches. This reversal is a critical data point, signaling that the multi-factor authentication mandates, strong password policies, and identity governance frameworks widely adopted across enterprise cloud tenants are effectively raising the baseline cost for attackers relying on identity compromise.
This transition is not accidental; it is a calculated adaptation by threat actors responding to elevated security controls. Industry analysts have long predicted that as defenses against brute force and credential stuffing hardened, attackers would pivot to the most technically challenging, yet potentially rewarding, avenue: software flaws. The report explicitly notes that this behavioral change is "potentially due to Google’s secure-by-default strategy and enhanced credential protections successfully closing traditional, more easily exploitable paths, raising the barrier to entry for threat actors." This validation underscores the efficacy of modern identity-centric security postures, even as it reveals the next frontier of risk.
The most immediately weaponized flaws cluster around Remote Code Execution (RCE) vulnerabilities. The speed at which these flaws are being integrated into active attack chains is alarming. Google observed cryptominers being deployed in some instances within a mere 48 hours of a vulnerability disclosure, suggesting that threat groups maintain highly sophisticated, automated exploit development pipelines ready to operationalize proof-of-concepts almost instantly. Notable examples cited include the exploitation of the React2Shell flaw (CVE-2025-55182) and the XWiki vulnerability (CVE-2025-24893), the latter famously leveraged by the RondoDox botnet to seize control of vulnerable servers.
The Collapse of the Patch Cycle and Industry Implications
The compression of the exploitation window—from weeks to mere days—represents a significant challenge for traditional patch management cycles. Historically, organizations operated on a timeline where vulnerability disclosure afforded weeks to test, stage, and deploy fixes across diverse cloud workloads. The new reality demands near-instantaneous remediation for critical flaws, particularly those leading to RCE.
This necessitates a paradigm shift toward continuous vulnerability management and automated remediation tools capable of isolating or patching systems before manual security teams can even triage the alert. For organizations leveraging hybrid or multi-cloud architectures, the complexity is compounded, as standardized vulnerability scanning and remediation tooling often fail to cover the disparate control planes of AWS, Azure, and GCP with equal efficacy. The industry implication is clear: speed of defense must now match the speed of offense. Failure to prioritize RCE vulnerabilities immediately post-disclosure moves from a compliance risk to an existential threat for cloud deployments.

While RCE dominates initial access statistics, it is crucial to note that compromised identities remain a potent secondary vector, particularly for state-sponsored and financially motivated espionage groups. Phishing and vishing attacks, often impersonating internal IT help desk personnel, continue to successfully obtain access to organizational cloud platforms. However, when these compromises occur, the subsequent objectives often favor stealth and data persistence over immediate financial gain, contrasting sharply with the goals of ransomware groups.
Deep Dive into State-Sponsored Espionage and Long-Term Persistence
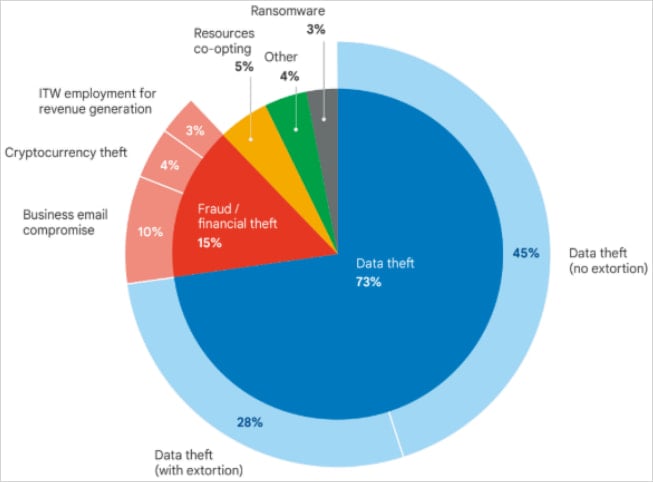
The analyzed intrusions showcase the divergent goals of different threat actor categories. Financially motivated actors often seek quick monetization, while advanced persistent threat (APT) groups prioritize long-term, low-and-slow access for intelligence gathering.
Google’s findings highlight campaigns by actors linked to Iran and China, demonstrating sustained access to victim environments exceeding eighteen months. One notable case involved the Iran-linked group UNC1549, which maintained a foothold for over two years utilizing stolen VPN credentials and the proprietary MiniBike malware. This extended access enabled the exfiltration of nearly one terabyte of sensitive proprietary data, underscoring that high-value data theft often requires prolonged, patient persistence, something easier to maintain once initial access is secured via a sophisticated exploit or a deep-seated identity compromise.
Similarly, the China-sponsored actor UNC5221 employed the BrickStorm malware to maintain clandestine access to VMware vCenter servers for at least 18 months, specifically targeting source code theft. These examples illustrate that while the initial entry point may now favor RCE bugs, the long-term objective—espionage—still requires techniques to maintain persistence that bypass standard network monitoring.
The North Korean Financial Engine and Supply Chain Subversion
Attacks attributed to North Korean entities reveal a focus squarely on revenue generation, often exploiting the intersection of human trust and technological complexity. Google identified that 3% of analyzed intrusions were linked to North Korean state actors (UNC5267) leveraging fraudulent identities to secure employment, effectively weaponizing the insider threat vector for state gain.
A more direct financial assault was executed by UNC4899, which specialized in compromising cloud environments to steal digital assets, specifically cryptocurrency. In a highly intricate scenario, UNC4899 deceived a developer into downloading a malicious archive, disguised as part of an open-source project collaboration. The subsequent infection chain is a masterclass in modern cloud infiltration:
- Initial Foothold: The developer transferred the file from a personal machine to a corporate workstation using AirDrop, opening it within an AI-assisted Integrated Development Environment (IDE).
- Payload Deployment: Malicious Python code deployed a binary masquerading as a legitimate Kubernetes command-line tool.
- C2 Communication: The binary established communication with UNC4899-controlled domains, creating a persistent backdoor onto the workstation, thereby granting the threat actors a beachhead within the corporate network perimeter.
- Lateral Movement: UNC4899 pivoted into the cloud environment, performing deep reconnaissance within the Kubernetes cluster. Crucially, they acquired a token for a high-privileged Continuous Integration/Continuous Deployment (CI/CD) service account.
- Privilege Escalation & Egress: Using the elevated CI/CD privileges, the actors moved laterally to a container responsible for enforcing network policies, enabling a container breakout to plant further persistence mechanisms. Subsequent reconnaissance targeted systems holding customer data, account security details, and—critically—insecurely stored database credentials containing cryptocurrency wallet data.
This sequence resulted in the compromise of user accounts and the theft of millions of U.S. dollars in digital assets. The sophistication lies in the blend of social engineering (the pretext of open-source collaboration), the abuse of local development tools (AI-IDE), and the exploitation of cloud-native trust mechanisms (Kubernetes tokens).

Abuse of Identity Federation: The OIDC Pathway
The report also highlights the increasing risk associated with identity federation, specifically the abuse of OpenID Connect (OIDC). In an incident tied to the "s1ngularity" supply-chain attack (August 2025), an attacker compromised an npm package named QuietVault. This compromise allowed the threat actor to steal a developer’s GitHub token.
The subsequent action involved leveraging the GitHub-to-AWS OIDC trust relationship to create a new, rogue administrator account within the target AWS environment. This exploit chain was executed with breathtaking speed:
Within three days of the initial package compromise, the attacker used AI prompting capabilities within local command-line tools to harvest the developer’s GitHub and NPM API keys. They then abused the CI/CD pipeline, leveraging the compromised OIDC trust, to mint the organization’s AWS API keys. The final objectives included data exfiltration from S3 storage, followed by destructive actions across production and cloud environments.
This incident underscores a profound industry risk: the security of cloud infrastructure is now intrinsically linked to the security of the developer supply chain and the integrity of identity federation protocols. Compromising a single artifact in a dependency chain can lead directly to administrative control over critical cloud resources if OIDC configurations are not meticulously scrutinized for least privilege.
The Resurgence of the Insider Threat Leveraging Cloud Services
While external threats dominate headlines, the analysis of data exfiltration trends reveals a disturbing upward trajectory in the use of legitimate cloud services by malicious insiders. Traditional exfiltration methods—email and portable storage—remain prevalent, but cloud storage platforms are rapidly becoming the preferred clandestine channels for data theft.
An analysis of 1,002 insider data theft incidents showed that 771 occurred while the individual was still employed, with 255 occurring post-termination. The platforms seeing increased insider abuse include AWS, Google Cloud, Microsoft Azure, Google Drive, Apple iCloud, Dropbox, and Microsoft OneDrive.
Security experts now contend that trend analysis suggests cloud services are poised to overtake email as the dominant method for insider data egress. This is largely because cloud storage offers higher volume capacity, better encryption, and lower detection rates compared to monitoring outbound email traffic. The implication for corporate data governance is the need for enhanced Data Loss Prevention (DLP) controls that monitor activity within sanctioned cloud environments, not just traffic leaving the corporate perimeter.
Furthermore, attackers, both external and internal, are actively engaging in counter-forensics. In a growing number of cases, threat actors are systematically deleting backups, erasing log files, and wiping forensic artifacts immediately after achieving their objective. This deliberate obfuscation drastically hampers breach investigation, evidence recovery, and root cause analysis, adding another layer of complexity to incident response.
Future Trajectories: Automation as the Only Viable Defense
The speed of modern cloud exploitation is now measured in minutes, not hours. Payloads have been observed being deployed within one hour of a new cloud instance being spun up, rendering manual incident response protocols obsolete. Google emphatically asserts that automated incident response (AIR) capabilities are no longer a luxury but an urgent necessity. Organizations must invest heavily in Security Orchestration, Automation, and Response (SOAR) platforms capable of quarantining compromised instances, revoking temporary credentials, and enforcing network segmentation without human intervention.
Looking ahead, the security landscape is expected to become more volatile. Geopolitical tensions, large-scale global events like the FIFA World Cup, and significant political milestones such as the U.S. midterm elections are projected to act as accelerants, driving increased malicious activity tailored to specific regional or ideological targets. Threat actors are increasingly aligning their operational tempo with global events to maximize impact or exploit heightened distraction levels.
In summary, the narrative of cloud security has shifted decisively from defending static perimeters against unsophisticated credential theft to actively managing a dynamic, high-velocity environment where zero-day vulnerabilities are weaponized at machine speed. Success in this new era hinges on predictive security modeling, automated defense mechanisms, and a radical re-evaluation of trust boundaries within the software supply chain and identity federation frameworks.

