The contemporary threat landscape is witnessing an alarming trend where sophisticated threat actors are weaponizing legitimate, widely used software frameworks to achieve stealth and evade traditional security measures. The relatively new ransomware operation known as LeakNet exemplifies this evolution, deploying a calculated attack chain that marries social engineering with the exploitation of modern, open-source development runtimes. Active since the close of 2024, LeakNet has maintained a steady, albeit modest, pace of approximately three successful compromises per month. However, the recent integration of these advanced evasion techniques suggests a potential inflection point, signaling readiness for significant operational scaling.
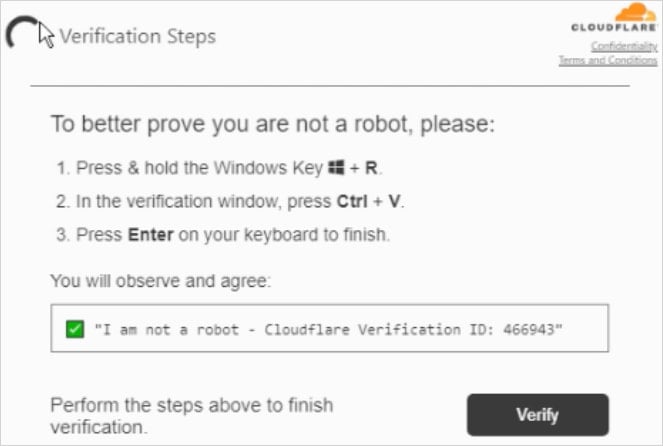
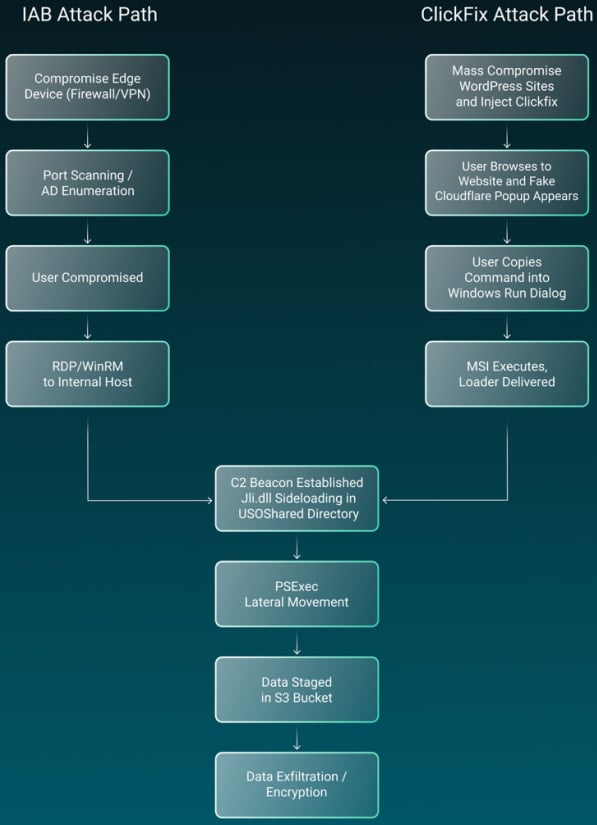
The initial vector employed by LeakNet centers around the "ClickFix" social engineering paradigm. This tactic relies on manipulating end-users into executing malicious commands, often masked as necessary system updates or IT fixes presented through deceptive prompts. This technique is not exclusive to LeakNet; it has been documented in the operations of other ransomware syndicates, including Termite and Interlock, underscoring its proven efficacy in breaching the human element of organizational security perimeters. In the context of LeakNet’s deployment, the success of the ClickFix lure leads directly to the installation and execution of a highly specialized malware loader built atop the Deno runtime environment.
Deno, recognized as a secure, modern runtime for executing JavaScript and TypeScript outside of a web browser, is being repurposed here in what researchers are terming a "Bring Your Own Runtime" (BYOR) attack. This strategy represents a significant tactical leap. By utilizing Deno—an executable that is cryptographically signed, legitimate, and inherently trusted by many security systems designed to monitor for unauthorized binaries—the attackers achieve an immediate advantage. Custom malware loaders are often heuristically flagged or blacklisted by endpoint detection and response (EDR) solutions; Deno, conversely, is expected to be present and active on systems belonging to developers or IT staff.
Security analysts have elucidated the core benefit of this approach: "Rather than deploying a custom malware loader that’s more likely to get flagged, the attackers install the legitimate Deno executable and use it to run malicious code," highlighting the deliberate choice to blend malicious activity with benign operational processes. The execution sequence observed involves initial scripting stages, often utilizing Visual Basic Script (VBS) or PowerShell, cleverly disguised with non-suspicious nomenclature such as Romeo*.ps1 and Juliet*.vbs. These scripts orchestrate the deployment of the Deno runtime and subsequently instruct it to process and execute the malicious payload entirely within the system’s volatile memory.
The critical nature of this in-memory execution cannot be overstated. By keeping the core malicious code off the disk—or at least executing it directly from memory without writing an intermediate dropper file—the threat actors drastically reduce the forensic footprint left behind. Disk-based analysis, a cornerstone of digital forensics, becomes significantly complicated, as the malware’s true nature is obscured, often appearing merely as a legitimate Deno process engaging in script interpretation. This low-artifact methodology directly challenges traditional signature-based detection and post-incident investigation methodologies.

Once the Deno-based loader achieves execution in memory, the malware initiates the standard reconnaissance and command-and-control (C2) phase. The initial script actively fingerprints the compromised host environment, establishing unique identifiers for the victim. This identifier is crucial for subsequent ransom negotiations and tracking. Simultaneously, the loader establishes a persistent connection back to the attacker-controlled C2 infrastructure. This C2 channel is not merely used for initial payload delivery; it is configured for continuous, persistent polling, allowing the threat actors to issue dynamic, second-stage commands in real-time, maximizing operational flexibility during the post-exploitation phase.
The subsequent stages of the LeakNet operation demonstrate a standard but effective playbook for deep network infiltration and data exfiltration. Following the initial beaconing, the threat actors engage in techniques designed to establish persistence and expand their foothold laterally. One observed technique involves DLL sideloading, specifically noting the loading of jli.dll through a legitimate Java process located in the unusual C:ProgramDataUSOShared directory—a deviation from standard installation paths that should raise immediate security alarms.
Credential discovery is executed through enumeration commands such as klist, targeting Kerberos tickets, which can provide access tokens for other services or systems within the domain. Lateral movement is then facilitated through established administrative tools, notably PsExec, indicating a high degree of trust or compromised credentials that allow for legitimate-looking remote service execution across the network. This combination of legitimate tools (PsExec, Deno) used maliciously is a hallmark of modern "living off the land" (LotL) techniques, which prioritize stealth over brute-force payload deployment.
The final stages involve data staging and exfiltration, a key component of modern double-extortion ransomware attacks. LeakNet has been observed abusing legitimate cloud storage infrastructure, specifically Amazon S3 buckets, to stage and siphon stolen corporate data out of the network perimeter. The exploitation of S3, a ubiquitous tool in modern cloud architecture, provides attackers with high-bandwidth, relatively inconspicuous egress channels that are often subject to less rigorous outbound traffic inspection than direct, unknown IP connections.
Industry Implications and the BYOR Arms Race
The adoption of Deno by LeakNet signals a critical maturation in ransomware operational security (OpSec). This move from custom binaries to legitimate runtimes places significant pressure on defensive architectures. For organizations relying heavily on application allow-listing or signature-based detection for executable files, Deno bypasses these controls by presenting as an authorized program.
This trend elevates the importance of behavioral analytics. Security tooling must evolve beyond merely checking what binary is running to scrutinizing how that binary is being utilized. The context surrounding Deno execution—such as its invocation via VBScript, its deployment outside typical development repositories, or its subsequent communication patterns—becomes the primary indicator of compromise (IOC). This forces security teams to invest heavily in advanced behavioral monitoring and process lineage tracking, areas traditionally reserved for high-tier security operations centers (SOCs).
Furthermore, the ClickFix vector highlights the persistent vulnerability in user training and security awareness programs. While technical defenses are hardening, the human interface remains the weakest link. The success rate of social engineering attacks, even those requiring user interaction, suggests that organizations must adopt continuous, context-aware security education rather than periodic, compliance-driven training modules.
Expert Analysis: The Erosion of Trust in Development Tools
From an expert perspective, the weaponization of Deno reflects a broader industry challenge: the proliferation of versatile, multi-purpose development tools creates an expanded attack surface. Software supply chain security concerns are no longer limited to third-party libraries or upstream dependencies; they now encompass the runtime environments themselves.
The BYOR methodology is fundamentally about obfuscation through legitimacy. It forces defenders into a difficult triage: distinguishing between a legitimate developer debugging code using Deno and an attacker encrypting a server farm using the same tool. This ambiguity grants the attacker crucial dwell time. The observed persistence mechanism—a continuous polling loop to the C2—suggests an attacker intent on maintaining long-term access post-initial compromise, potentially positioning LeakNet not just as a pure encryption threat but as a sophisticated initial access broker or long-term espionage tool that culminates in data extortion.
The use of well-known LotL tools like PsExec, coupled with modern memory-resident execution, paints a picture of a threat actor that is highly adaptable and willing to invest time in reconnaissance and preparation rather than relying on immediate, noisy deployment. This calculated approach is characteristic of more mature, well-resourced groups aiming for maximum data extraction before detection.
Future Impact and Defensive Posture
The trajectory suggested by LeakNet’s tactics points toward an acceleration in the adoption of non-traditional execution environments by ransomware actors. We can anticipate further weaponization of other legitimate scripting runtimes (e.g., Node.js, specialized compilers, or even container orchestration tools) to execute the initial stages of an attack.
For defenders, hardening procedures must focus on application control that is aware of context, not just identity. Key defensive imperatives stemming from the LeakNet analysis include:
- Runtime Context Monitoring: Implementing EDR policies that specifically flag the execution of runtimes like Deno or Node.js when initiated by non-standard parent processes (like VBScript or external browsers) or when arguments suggest execution from temporary directories or unusual locations.
- Network Anomaly Detection: Establishing strict baselines for outbound traffic. Unexpected connections from services like Deno or PowerShell to cloud storage providers (like S3) or known C2 ranges must trigger immediate high-severity alerts.
- Privilege Reduction: Minimizing the necessary permissions for standard user accounts to execute administrative tools like PsExec remotely. Limiting lateral movement potential severely curtails the blast radius of successful initial access.
- Memory Forensics Readiness: Ensuring that incident response protocols incorporate memory capture and analysis capabilities as a primary investigation step, acknowledging that disk artifacts may be sparse or misleading.
The LeakNet operation serves as a potent reminder that as endpoint security evolves to block known malicious files, threat actors pivot to leveraging the tools already trusted by the enterprise. Success in mitigating such threats requires security teams to look past the file hash and deeply scrutinize the operational context of every running process. The arms race is shifting from fighting malware signatures to policing legitimate application behavior.

