The digital landscape of cryptocurrency-enabled commerce faced a significant disruption earlier this month when Bitrefill, a prominent platform facilitating the purchase of global gift cards using digital assets, confirmed it had been the target of a sophisticated cyberattack. Following an intensive internal forensic investigation, the company has publicly attributed the breach to operatives linked to the Democratic People’s Republic of Korea (DPRK), specifically pointing fingers at the Lazarus Group’s specialized sub-unit, Bluenoroff. This attribution is not merely speculative; Bitrefill’s security team identified a constellation of technical and operational indicators that strongly align with the established modus operandi of this highly persistent and state-sponsored threat actor.
Bitrefill operates at the intersection of fiat accessibility and decentralized finance, providing users across 150 countries with the ability to convert cryptocurrencies into tangible purchasing power across thousands of global brands and over 600 mobile operators. This utility—bridging the volatility of crypto markets with everyday consumer needs ranging from groceries and apparel to utility payments and transportation—makes it a high-value target for entities seeking to monetize cyber operations.
The initial signs of trouble surfaced on March 1st, when the platform experienced widespread technical anomalies impacting both its website and mobile applications, signaling a major operational failure. Within 24 hours, the scope of the problem escalated, prompting Bitrefill to take all services completely offline to contain the breach and conduct a thorough security assessment. While the company was quick to assure users that core account balances remained untouched—a critical point given the nature of its business—the full remediation and gradual restoration of services have proven to be a complex, ongoing process.
The discovery of the intrusion was triggered by internal monitoring flagging highly irregular activity related to vendor purchasing patterns, unauthorized depletion of gift card stock, and suspicious activity surrounding low-security, high-liquidity cryptocurrency holding addresses, often referred to as "hot wallets." This triangulation of indicators pointed away from a simple denial-of-service attack or minor vulnerability exploitation toward a targeted, data-exfiltration and asset-theft operation.
Forensic analysis pinpointed the initial vector: a compromised employee workstation. The attackers successfully leveraged legacy authentication credentials, likely acquired through phishing or credential stuffing campaigns targeting the employee, to gain initial network access. This foothold was then exploited to locate and exfiltrate a snapshot containing critical production secrets. From this initial foothold, the threat actors systematically escalated their privileges across the Bitrefill infrastructure, ultimately gaining access to sensitive sections of the customer database and, most critically, cryptocurrency wallet management systems.
The compromise resulted in the exposure of data pertaining to approximately 18,500 purchase transactions. This exposed data set includes customer email addresses, associated IP addresses used during transactions, and the cryptocurrency payment addresses utilized. For a smaller subset of approximately 1,000 of these transactions, full customer names were also compromised. Bitrefill acknowledged a severe risk factor: while this sensitive customer data was stored in an encrypted format, the possibility exists that the decryption keys necessary to unlock this information were also among the stolen production secrets.
Despite the severity of the access gained, Bitrefill characterized the financial impact as "minimal losses," which the company intends to absorb directly from its corporate capital reserves. This suggests the attackers, while gaining access to wallets, may not have succeeded in draining the largest, most secure cold storage reserves, or that Bitrefill’s rapid containment limited the extent of crypto asset theft. Crucially, the company’s assessment suggests the primary objective was the theft of cryptocurrency assets and the exploitation of the high-value gift card inventory, rather than a sustained campaign focused purely on harvesting personally identifiable information (PII) for espionage or identity fraud purposes.

The identification of Bluenoroff as the perpetrator is significant, as this group, often interchangeably referenced with APT38, has a well-documented history dating back to at least 2014. While Lazarus Group is broadly known for large-scale, disruptive attacks—including the infamous Sony Pictures breach and the WannaCry ransomware campaign—Bluenoroff has specialized almost exclusively in financially motivated cyber espionage. Their recent operational pivot has heavily favored the cryptocurrency sector, viewing decentralized finance platforms as lucrative, often less regulated targets compared to traditional banking institutions.
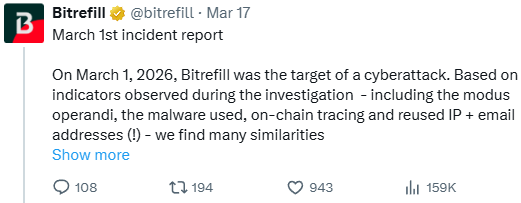
Bitrefill’s internal statement explicitly cited the parallels: "Based on indicators observed during the investigation – including the modus operandi, the malware used, on-chain tracing and reused IP + email addresses (!) – we find many similarities between this attack and past cyberattacks by the DPRK Lazarus / Bluenoroff group against other companies in the crypto industries." The inclusion of "on-chain tracing" suggests that blockchain analytics tools were instrumental in linking the attack’s transaction footprint to known Lazarus operational wallets or pathways previously identified by cybersecurity researchers tracking DPRK illicit financing.
This incident serves as a stark reminder of the evolving threat landscape facing FinTech and cryptocurrency service providers. The attack on Bitrefill was not a zero-day exploit targeting a novel software flaw; it was a highly organized, persistent social engineering and credential theft operation culminating in privilege escalation—a classic, yet devastatingly effective, playbook favored by state-sponsored actors who possess virtually limitless time and resources for reconnaissance and execution.
Industry Implications and the Evolving Threat Model
The attribution to Bluenoroff has profound implications for the broader crypto-commerce ecosystem. The Lazarus Group rarely engages in opportunistic attacks; their operations are typically strategic, designed to generate significant foreign currency revenue for the regime. When they target a specific sector, it signals a sustained strategic interest. The focus on a gift card intermediary like Bitrefill suggests a calculated attempt to launder stolen digital assets into widely usable, difficult-to-trace fiat-adjacent instruments. Gift cards are often less scrutinized than direct cryptocurrency exchanges, providing an effective cash-out mechanism.
For mid-sized platforms operating in this niche, the implications are severe. While major centralized exchanges invest heavily in nation-state-level defense infrastructure, smaller, specialized services often rely on standard enterprise security packages, which may prove insufficient against an adversary capable of patient, targeted reconnaissance against individual employees.
The attack vector—compromised employee laptop leading to legacy credential theft—highlights a persistent weakness across the digital enterprise: identity and access management (IAM). Even with robust multi-factor authentication (MFA) deployed on primary systems, the persistence of legacy credentials, potentially stored insecurely or used for less-protected ancillary services, remains a critical chink in the armor. Bluenoroff’s ability to pivot from a low-level endpoint compromise to accessing a "snapshot with production secrets" suggests a failure in network segmentation and least-privilege enforcement policies surrounding highly sensitive data repositories.
Expert Analysis: The Sophistication of DPRK Cyber Operations
From a cybersecurity perspective, the characteristics cited by Bitrefill are textbook indicators of Bluenoroff activity. Their operations are known for meticulous reconnaissance, often involving weeks or months of monitoring employee communications and habits before launching the final infiltration attempt. The utilization of reused IP and email addresses, though seemingly rudimentary, is often a hallmark of state-sponsored groups who maintain large, diverse pools of compromised infrastructure (bulletproof hosting or hijacked VPNs) that they cycle through, but sometimes reuse patterns emerge across unrelated campaigns.
The use of custom or modified malware is also a Bluenoroff specialty. They frequently employ tools designed to evade standard endpoint detection and response (EDR) solutions by blending in with legitimate system processes or utilizing fileless execution techniques. In the context of crypto theft, their malware is often tuned to specifically target digital wallet configuration files, API keys, or session tokens that grant access to hot wallets or custodial services.
The on-chain tracing element is perhaps the most powerful indicator. State-sponsored actors are experts at obfuscating their financial trails using mixers, privacy coins, and complex layering techniques. However, the sheer volume of funds they move and the operational necessity to eventually convert those funds into usable currency create friction points on the blockchain. If Bitrefill’s analysts could link the compromised wallet drainage to known historical DPRK addresses—even transient ones—the confidence in the attribution skyrockets. This level of analysis requires access to high-end blockchain intelligence platforms, underscoring the seriousness of the threat the company faced.
Future Impact and Trend Forecasting
The Bitrefill incident reinforces several critical trends shaping cybersecurity for digital asset platforms:
-
The Permanent Targeting of the Crypto Ecosystem: The era where cryptocurrency platforms were an occasional target is over. For groups like Lazarus, crypto assets represent a comparatively low-risk, high-reward avenue for generating untraceable state revenue. This focus will only intensify, leading to an arms race between platform security enhancements and attacker ingenuity.
-
Elevation of Insider Threat Vectors (Even Indirectly): While this was not an intentional insider threat, the compromise originated from an employee endpoint. This underscores that perimeter defense is insufficient. Security frameworks must shift focus towards continuous monitoring of user behavior, strict enforcement of zero-trust architectures, and rigorous access control, even for seemingly low-risk employees who might possess legacy access rights to critical data snapshots.
-
The Necessity of Enhanced Data Hygiene: The exposure of encrypted data, coupled with the potential theft of decryption keys, highlights that encryption alone is not a panacea. Data governance—classifying data sensitivity, restricting access to encryption keys, and ensuring that production secrets are not stored in easily accessible archives—must be prioritized alongside cryptographic strength.
In response to the breach, Bitrefill is undertaking a comprehensive overhaul of its security posture. This includes expanding third-party penetration testing, implementing more stringent access controls across all environments, and significantly upgrading logging and monitoring capabilities to detect anomalous behavior faster. Furthermore, the refinement of automated shutdown mechanisms suggests a commitment to reducing the "dwell time" of an attacker—the period between initial compromise and detection—which is the primary determinant of the scope of financial loss in these scenarios.
For the time being, most services are stabilized, and customers are advised primarily to maintain vigilance regarding external communications, suggesting a fear that phishing campaigns leveraging the stolen emails or personal data might follow. The resilience demonstrated by Bitrefill in absorbing the loss and rapidly implementing systemic security improvements suggests that, while this was their most severe incident in a decade, the core business model and operational integrity have proven durable enough to withstand a highly sophisticated, state-sponsored assault. However, the incident serves as a critical data point confirming that the digital black market financing operations run by Pyongyang are actively innovating their methods to target the infrastructure underpinning global digital commerce.

