The digital ecosystem is currently grappling with a sophisticated social engineering and malware campaign that weaponizes the trust placed in ubiquitous, benign software. Researchers have uncovered a pervasive threat where a meticulously crafted counterfeit website for the popular file archiving utility, 7-Zip, is distributing an installer deeply laced with proxy-enabling malware. This Trojanized application successfully installs the legitimate 7-Zip functionality, thereby masking its malicious payload, while simultaneously enrolling the unsuspecting user’s machine into a sprawling residential proxy network.
This technique leverages the high volume of users seeking essential, free utilities. Residential proxies, fundamentally, are networks built by commandeering the legitimate, dynamic IP addresses associated with home internet connections. While legitimate use cases exist for such proxy services—such as market research or geo-unblocking—the primary illicit appeal lies in their capacity to mask malicious operations. By routing illicit traffic through compromised home devices, threat actors can execute activities like large-scale credential stuffing attacks, sophisticated phishing campaigns, and the dissemination of further malware, all while maintaining a veneer of legitimacy derived from a typical residential IP address, making immediate blocking far more challenging for security providers.
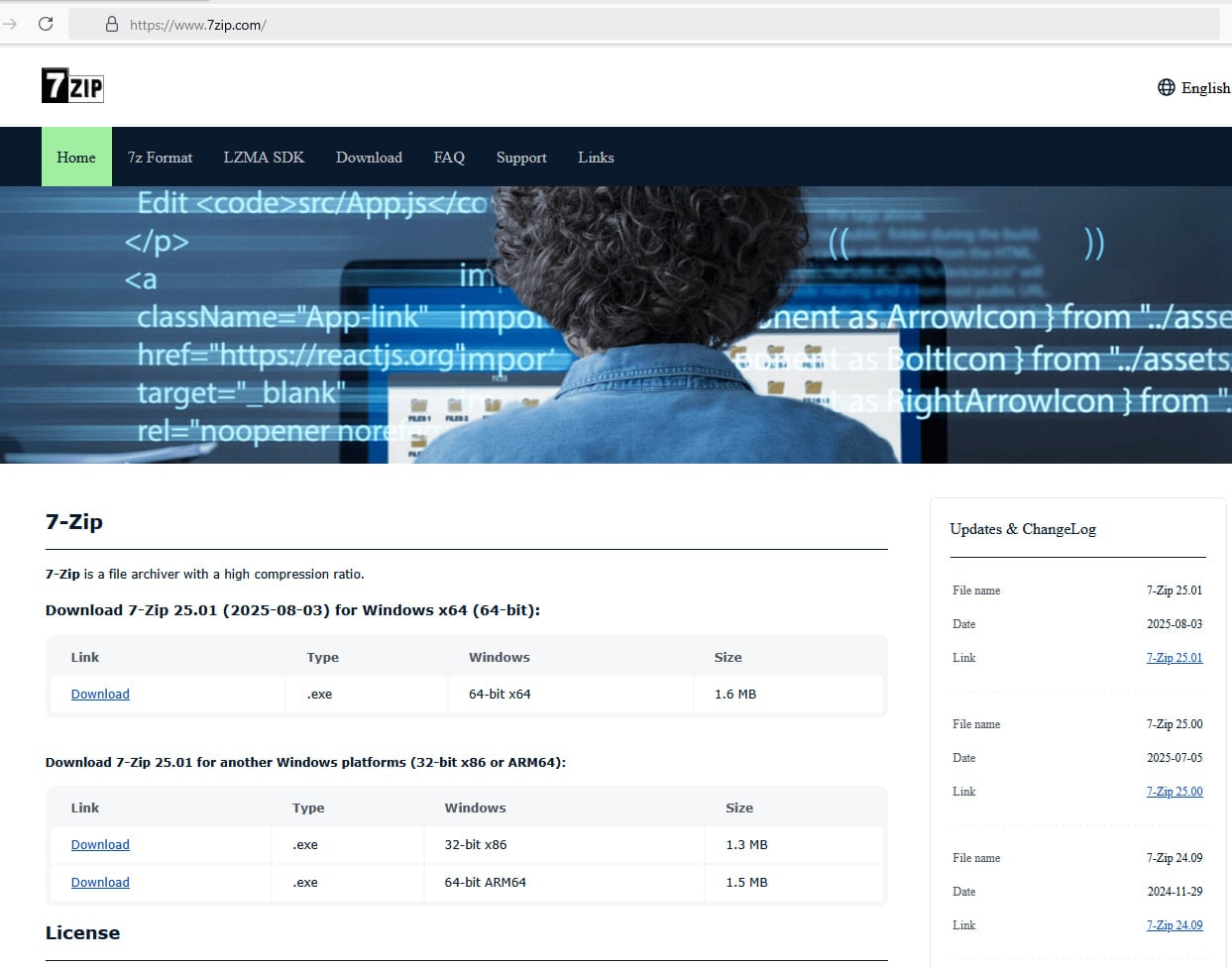
The exposure of this specific threat vector gained significant traction following reports from an end-user who inadvertently downloaded the malicious installer while following instructions gleaned from a seemingly innocuous YouTube tutorial detailing PC system assembly. This highlights a crucial vector: novice users or those seeking quick installation guides are highly susceptible to top search results that often lead to visually convincing but malicious imposter domains. Verification confirmed that the deceptive domain, registered as 7zip[.]com, remains operational at the time of this analysis, continuing to mimic the aesthetic and textual layout of the official, trustworthy project site located at 7-zip.org.
The threat actor’s execution is marked by a high degree of mimicry. The counterfeit site not only duplicates the visual design elements but also meticulously copies the textual content, engineering a near-perfect replica to exploit user familiarity and established trust. This level of dedication to impersonation underscores a growing trend in cybercrime: focusing less on zero-day exploits and more on exploiting human trust and search engine optimization (SEO) manipulation.
Forensic analysis of the delivered installer package, conducted by cybersecurity firm Malwarebytes, revealed several key technical indicators. The installer was found to be digitally signed, albeit with a certificate that has since been revoked, which was originally issued to a known entity, Jozeal Network Technology Co., Limited. This use of a compromised or fraudulently obtained certificate adds a layer of superficial legitimacy during initial execution on some systems, bypassing basic application trust checks.

Crucially, the installation process is dual-natured. It successfully deploys the standard 7-Zip file management binaries, ensuring the user perceives the operation as successful. Concurrently, however, the installer seeds the system with three distinct malicious files. These components are strategically deposited into the non-standard directory C:WindowsSysWOW64hero. Furthermore, persistence is established robustly: an auto-start Windows service is created, configured to run with the highest privilege level (SYSTEM), ensuring the two primary malicious executables launch reliably upon system boot.
To guarantee unimpeded communication with command-and-control (C2) infrastructure, the malware proactively alters local security parameters. It employs the native netsh utility to modify Windows firewall rules, explicitly permitting both inbound and outbound network traffic for its malicious binaries. This preemptive configuration step is indicative of planning designed to maintain long-term covert connectivity.
Once embedded, the malware initiates a comprehensive reconnaissance phase. It interrogates the host system extensively, leveraging powerful native tools such as Microsoft’s Windows Management Instrumentation (WMI) and various Windows APIs. This profiling is designed to gather detailed hardware and software specifications: CPU type, memory allocation, disk configuration, and specific network topology data. This inventory is not for direct exploitation but rather to profile the suitability of the machine for proxy usage and to build a dossier on the potential value of the compromised IP address. The collected system telemetry is subsequently exfiltrated to an external logging endpoint, identified as iplogger[.]org.
Malwarebytes’ deep dive into the malware’s operational goals clarified its primary function. While initial telemetry might suggest capabilities associated with traditional backdoors—tools designed for remote system control or data theft—the core objective is centered on "proxyware." The analysis concludes: "The infected host is enrolled as a residential proxy node, allowing third parties to route traffic through the victim’s IP address." This redefines the threat from simple data theft to the monetization of the user’s identity and internet access.
The operational mechanics of the proxy component, designated as hero.exe, involve dynamically pulling configuration data from a rotating series of C2 domains, typically themed around "smshero." The malware then establishes outbound proxy connections utilizing non-standard communication ports, specifically noted as 1000 and 1002. To obscure the content of these control messages from passive network monitoring, a lightweight XOR encryption key is employed for obfuscation, adding a necessary layer of protection for the attacker’s infrastructure management.
A significant finding expands the scope of this operation beyond the 7-Zip lure. The underlying malware framework is evidently versatile, also being utilized to inject malicious code into installers for other widely used software, including HolaVPN, TikTok, WhatsApp, and Wire VPN. This multi-pronged distribution strategy maximizes the potential victim pool by targeting users across different software needs, from communication tools to VPN services.

The resilience of the C2 infrastructure is noteworthy. The threat actors have constructed a robust, decentralized command-and-control system built around the aforementioned hero/smshero domain naming convention. Furthermore, the use of Cloudflare infrastructure for traffic routing, combined with mandatory TLS-encrypted HTTPS for all communications, presents a considerable challenge to traditional network defenders. This setup effectively masks the ultimate destination of the C2 traffic, routing it through a trusted Content Delivery Network (CDN).
Adding another layer of evasion, the malware explicitly utilizes DNS-over-HTTPS (DoH) resolution, specifically targeting Google’s public resolver. This technique bypasses conventional, unencrypted DNS monitoring points, rendering standard security appliances blind to the initial hostname lookups required to establish contact with the C2 servers.
In a demonstration of advanced evasion tactics, the malware includes self-defense mechanisms specifically designed to thwart automated analysis. It actively checks for the presence of virtualization platforms—such as VMware, VirtualBox, QEMU, and Parallels—as well as for debugging software environments. If such analysis tools are detected, the malware is programmed to cease malicious operations or terminate entirely, preventing researchers from safely mapping its full capabilities.
The comprehensive understanding of this threat stems from collaborative, independent research. The initial breakthrough in identifying the Uphero/hero malware’s core proxy function is credited to independent security researcher Luke Acha. Subsequent technical deep dives followed, with researcher s1dhy successfully reverse-engineering and decoding the XOR-based communication protocol, confirming the proxy behavior. Finally, Digital Forensics and Incident Response (DFIR) engineer Andrew Danis linked the specific fake 7-Zip installer to this broader, multi-brand impersonation campaign.
Industry Implications and Expert Analysis
The deployment of proxyware via trusted software installers marks an evolution in cybercriminal monetization strategies. For cybersecurity professionals, this campaign demands a shift in defensive posture. It moves the focus from simply blocking known malware signatures to scrutinizing the behavior of software during and immediately after installation.
The reliance on social engineering through YouTube tutorials and high-ranking search results underscores the fragility of user-side security hygiene. Experts consistently stress that domain validation is paramount. In this instance, the subtle difference between 7-zip.org (official) and 7zip.com (malicious) is easily missed, especially when users are operating under the pressure of following a multi-step setup guide.
The technical sophistication of the proxy component warrants serious attention. The use of system-level services, firewall manipulation via netsh, and evasion techniques like DoH and virtualization detection elevate this from a simple dropper to a persistent, low-and-slow threat actor toolset. The decision to use residential IPs rather than dedicated bulletproof hosting or compromised servers suggests the operators are focused on long-term, high-anonymity activity that generates sustained revenue through proxy rental services.
From an infrastructure perspective, the use of Cloudflare, while common for legitimate sites, illustrates the blurring lines between benign and malicious actors leveraging established, high-reputation services for cover. Defenders must increasingly rely on behavioral analysis and network flow monitoring, rather than simple IP or domain blacklisting, which these adversaries are adept at rotating.
Future Impact and Trends
This incident is a strong indicator of future attack trends, particularly the "Software-as-a-Service" (SaaS) model applied to cybercrime infrastructure. We are likely to see an increase in campaigns that bundle legitimate-looking applications with auxiliary malicious modules designed to exploit user resources—whether that be processing power (cryptojacking) or network bandwidth (proxying).
The proliferation of proxy networks also has significant implications for digital trust and authentication. As more services rely on IP reputation for fraud detection, the availability of vast residential proxy pools makes synthetic identity fraud and account takeovers significantly easier to execute without triggering automated defenses. This escalates the challenge for financial institutions and e-commerce platforms attempting to distinguish legitimate users from automated attackers.
Furthermore, the tactics observed here—deep content copying, leveraging social media tutorials, and implementing advanced anti-analysis measures—will likely be integrated into broader initial access brokers’ toolkits. Software vendors, particularly those offering popular, free utilities, must invest heavily in monitoring domain registrations that closely resemble their own and proactively educating their user bases on the exact, verified download URLs.
In summary, the fake 7-Zip campaign is a high-fidelity example of modern cyber-espionage evolving into a lucrative infrastructure service model. The immediate defense requires vigilance from end-users to strictly bookmark and use only verified software sources, coupled with robust endpoint detection and response (EDR) systems capable of flagging the subtle, yet persistent, network activity characteristic of proxyware operations.

