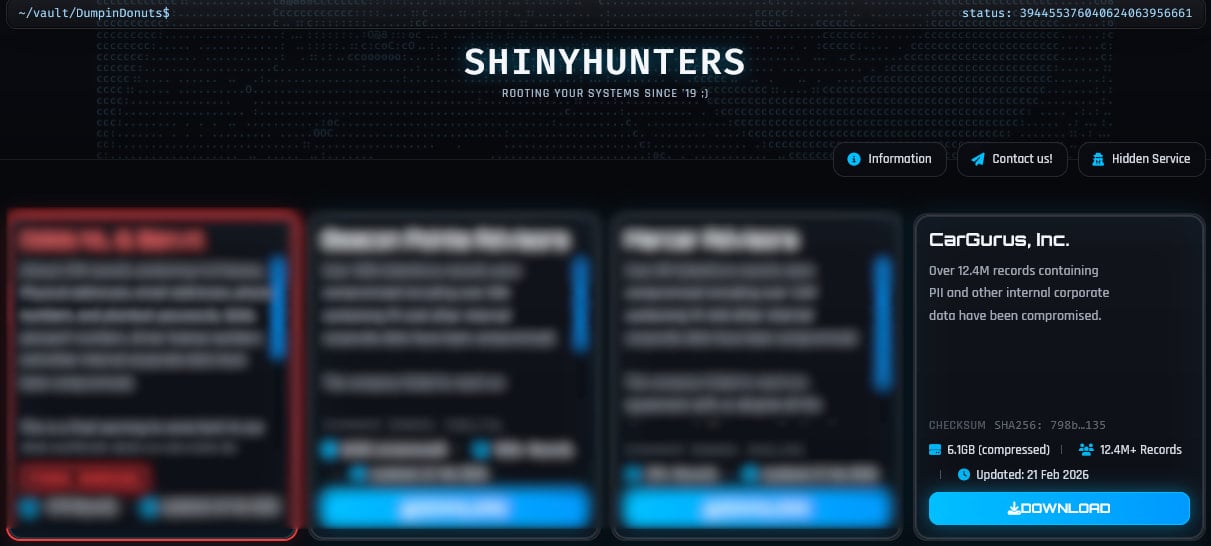
The digital landscape for automotive commerce has been shaken by the alleged data exfiltration from CarGurus, a prominent, publicly traded entity facilitating vehicle research and sales across the United States, Canada, and the United Kingdom. Reports surfaced around February 21st indicating that the notorious cybercriminal collective known as ShinyHunters had published a substantial dataset, purportedly containing personal information harvested from the platform’s extensive user base. This incident immediately raises significant concerns regarding consumer data security within the burgeoning digital auto marketplace sector, an industry that has seen explosive growth as consumers increasingly rely on online platforms to navigate complex, high-value transactions like purchasing a vehicle.
CarGurus, boasting an estimated forty million monthly unique visitors to its platform, serves as a critical intermediary, connecting potential buyers with dealerships and private sellers. The sheer volume of traffic underscores the value of the data it processes and stores, making it an attractive target for financially motivated threat actors. The published archive, reported to be approximately 6.1 gigabytes in size, allegedly encompasses records belonging to 12.4 million distinct accounts.
The immediate confirmation of the dataset’s presence on the dark web marketplace was followed swiftly by its indexing on the widely recognized data breach monitoring service, HaveIBeenPwned (HIBP). HIBP’s inclusion of the dataset, which typically involves a verification process to assess the authenticity of the leaked material, lends a measure of credibility to the threat actor’s claims. While CarGurus has, at the time of this reporting, refrained from issuing a formal public disclosure acknowledging a security incident or responding to direct inquiries from technology journalists, the indexing by HIBP is a significant indicator that the exposed data possesses demonstrable validity.
A detailed analysis of the indexed data reveals several critical elements compromised, including user names, email addresses, and potentially encrypted passwords or password hashes, alongside other personally identifiable information (PII) associated with user accounts on the platform. The exact breadth of compromised fields, such as geographical location data, search history, or contact preferences, remains a central point of concern for affected users and regulatory bodies alike.
HIBP’s preliminary assessment provided a nuanced view of the breach’s novelty. According to their telemetry, approximately 70% of the records found within the 12.4 million set already existed in their database, stemming from previous, unrelated security compromises. This suggests that while the breach might not be entirely novel for a significant portion of individuals, the remaining roughly 3.7 million records represent newly exposed data points. In the ecosystem of cybercrime, the introduction of fresh PII into the marketplace dramatically increases the risk profile for those users. This newly available data is immediately weaponized by threat actors for targeted spear-phishing campaigns, identity theft attempts, and credential stuffing attacks across other online services.

The modus operandi of the ShinyHunters group is crucial to understanding the context of this alleged compromise. ShinyHunters is not typically known for sophisticated zero-day exploitation but rather for a highly effective, aggressive campaign relying heavily on social engineering tactics to gain initial access to corporate environments. Their preferred entry vector often targets the human element, utilizing sophisticated phishing—specifically voice phishing (vishing)—to trick employees into revealing credentials or authorising malicious access.
This methodology frequently targets high-value Software-as-a-Service (SaaS) environments such as Salesforce, Okta identity management systems, and Microsoft 365 productivity suites. Once initial credentials are stolen through these deceptive channels, the attackers can often pivot laterally within the network. In previous campaigns attributed to the group, a common tactic involved convincing an employee to authorize a malicious OAuth application. This authorization grants the attackers API-level read access to sensitive data tables, particularly within CRM systems like Salesforce, allowing them to systematically exfiltrate customer databases without necessarily triggering traditional intrusion detection systems that monitor for bulk file transfers or malware execution.
The sustained activity of ShinyHunters is notable. In recent months, the group has claimed responsibility for high-profile incidents across diverse industries. Examples include breaches targeting the Dutch telecommunications provider Odido, the advertising technology firm Optimizely, the fintech company Figure, luxury outerwear brand Canada Goose, the restaurant giant Panera Bread (where the scale of the breach was later revised upward), the dating conglomerate Match Group (affecting Tinder, Hinge, and OkCupid), and the music streaming service SoundCloud. This diverse victimology underscores the group’s adaptability and their focus on data-rich organizations regardless of sector.
For CarGurus users, the immediate imperative is heightened vigilance. The availability of their personal identifiers and contact information makes them prime targets for phishing attempts masquerading as legitimate communications from the auto platform, financial institutions, or even related service providers. Users should scrutinize any unsolicited emails, text messages, or phone calls requesting personal verification, password resets, or financial details.
Industry Implications and Digital Trust Erosion
The automotive retail sector is undergoing a profound digital transformation. Companies like CarGurus have built significant market capitalization by promising efficiency, transparency, and a streamlined customer experience online. However, incidents like this severely erode the digital trust foundation upon which these platforms operate. Consumers entrust these sites not just with browsing history but with the sensitive details required to facilitate high-value transactions.
From an industry perspective, this breach highlights vulnerabilities inherent in the interconnectedness of modern digital commerce. Many automotive platforms rely on complex stacks involving third-party integrations, cloud services, and extensive data sharing between dealers and the central platform. If the initial compromise vector utilized by ShinyHunters was indeed related to compromised employee credentials accessing a centralized SaaS platform (like Salesforce, as is their known pattern), it points toward systemic weaknesses in identity and access management (IAM) protocols across the sector.

The reliance on multi-factor authentication (MFA) alone is clearly insufficient against sophisticated social engineering attacks like vishing, which can bypass basic MFA prompts by convincing users to approve the login attempt manually. This necessitates a pivot toward more resilient security postures, including implementing phishing-resistant MFA methods, such as FIDO2 hardware keys, or employing continuous adaptive risk and trust assessment (CARTA) models that monitor user behavior for anomalies.
Expert Analysis: The Persistence of Identity-Centric Attacks
Cybersecurity experts consistently point to identity as the new perimeter. When perimeter defenses—firewalls and network segmentation—are bypassed through compromised credentials, the internal controls governing access to data repositories become the last line of defense.
The fact that 70% of the data was already known suggests a degree of "data fatigue" among end-users, where repeated breaches dilute the perceived threat of new leaks. However, the value of this specific dataset lies in its coherence. A single, clean dataset belonging to a known entity like CarGurus is more valuable to an attacker than disparate fragments. They can cross-reference email addresses with known password dumps to increase the success rate of credential stuffing on other platforms—a practice known as "credential stuffing."
Furthermore, the nature of the automotive buying process means that data related to vehicle interests or credit pre-qualification inquiries might be present. If any financial indicator data was inadvertently included, even if partially masked, the risk for sophisticated financial fraud skyrockets. Security researchers emphasize that while encrypted passwords are safer than plaintext, the presence of password hashes necessitates immediate, mandatory global password resets for all affected users, even if the hashes are considered strong.
The current silence from CarGurus, while perhaps reflecting a desire to complete a thorough internal investigation before making public statements, creates an information vacuum that benefits the threat actors. In the modern regulatory environment, transparency—even during the investigative phase—is often favored as it allows users to take timely protective measures. The delay in official confirmation contrasts sharply with the swift public dissemination by the threat group and HIBP, placing the onus entirely on the consumer to monitor external breach intelligence.
Future Impact and Security Trends
This incident serves as a potent case study illustrating the evolving threat landscape targeting data-rich digital marketplaces. The future of cybersecurity resilience for such companies must move beyond reactive patching to proactive threat hunting centered on identity compromise.
-
Defense Against Social Engineering: Organizations must invest heavily in continuous security awareness training that specifically simulates vishing and sophisticated phishing attempts. The training must evolve beyond simple identifying suspicious links to include recognizing subtle conversational manipulation techniques used by social engineers.
-
Zero Trust Architecture Implementation: A full commitment to Zero Trust principles is non-negotiable. This means strictly verifying every access request, regardless of origin, and enforcing the principle of least privilege. If an attacker gains access via a single compromised account, the blast radius must be severely limited, preventing them from accessing entire customer databases via API calls.
-
Supply Chain and Vendor Risk Management: Given ShinyHunters’ typical entry vector via SaaS providers, CarGurus must rigorously audit the security posture of all vendors who have API access or privileged access to their core systems. OAuth authorizations, in particular, need granular scoping and regular re-authorization checks.
-
Regulatory Scrutiny: As data protection regulations tighten globally (e.g., GDPR implications if UK/EU user data is involved, or evolving US state laws), the lack of timely disclosure following the public release of data will likely invite regulatory inquiry, regardless of the eventual findings regarding the breach’s root cause. The perception of delayed notification can itself lead to significant compliance penalties.
The incident involving 12.4 million records attributed to CarGurus underscores a critical reality: the friction points in digital customer journeys—where data is collected, stored, and shared—remain the most vulnerable links in the security chain. For the automotive industry, maintaining the trust necessary for high-value online transactions hinges on demonstrating superior security practices that can withstand determined, identity-focused extortion groups like ShinyHunters. Users must remain alert, and the industry must accelerate its adoption of advanced, identity-centric security frameworks.

