The persistent threat landscape surrounding high-end commercial spyware has just seen a significant technical unveiling, detailing precisely how Intellexa’s sophisticated Predator malware achieves near-total invisibility on compromised Apple iPhones. New analysis by security researchers illuminates a highly targeted maneuver within the core operating system—specifically, the hijacking of the SpringBoard process—to systematically suppress the on-screen indicators mandated by Apple to signal active microphone or camera usage. This capability moves Predator beyond mere data exfiltration; it represents an active camouflage operation designed to deceive the end-user during covert surveillance.
For context, Apple introduced robust visual privacy cues starting with iOS 14: a distinct orange dot illuminates the status bar when the microphone is active, and a green dot signals camera engagement. These features were foundational responses to growing public and regulatory concerns over digital eavesdropping, intended to restore a degree of user control and awareness over device sensor access. Predator’s evasion technique, however, renders these critical safeguards inert, allowing operators to capture audio and video streams without alerting the target.
Crucially, this attack vector does not rely on exploiting a newly discovered zero-day vulnerability in the current iteration of iOS. Instead, the technique presupposes that the spyware has already achieved deep, persistent access—specifically, kernel-level privileges. This level of compromise is typically achieved through the exploitation of prior vulnerabilities, potentially including zero-days that Apple has since patched, or via sophisticated, multi-stage infection chains often associated with nation-state actors or highly targeted professional surveillance campaigns. Once root access is established, Predator shifts from infiltration to operational stealth.
The detailed documentation of this indicator suppression mechanism comes from researchers at Jamf, who dissected active samples of the Predator spyware. Their findings expose a surgical modification within the system’s user interface management layer, SpringBoard, which is responsible for rendering the entire home screen experience, including the status bar indicators.

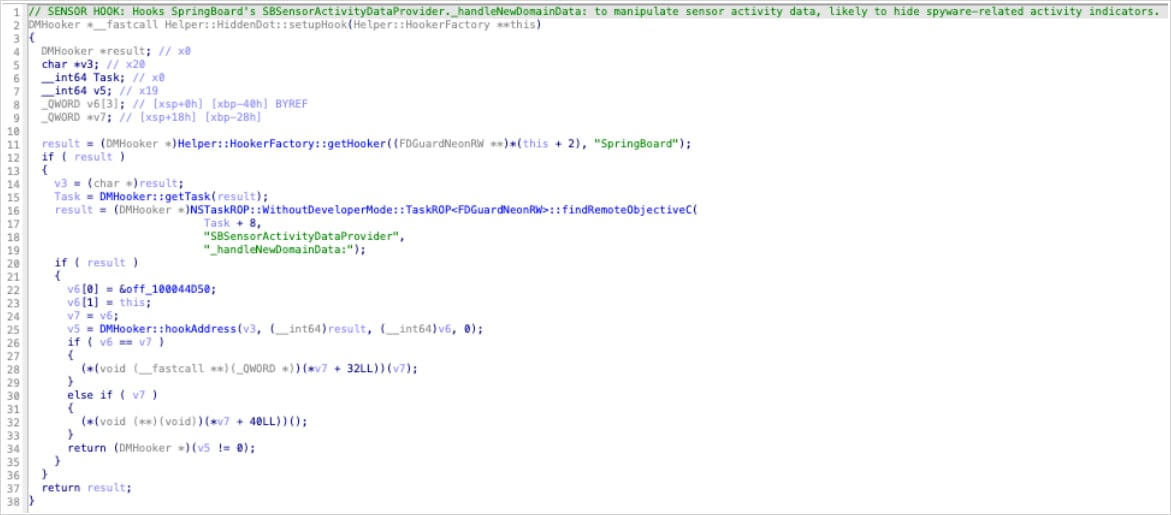
The mechanism hinges on a specific function hook, identified internally by the malware as HiddenDot::setupHook(). This hook is strategically deployed within the SpringBoard environment. The objective is to intercept system calls triggered whenever there is a change in sensor status—meaning, precisely at the moment the camera or microphone is initialized for data capture. By establishing this intercept point early in the processing pipeline, Predator effectively creates a firewall, preventing the notification signal from ever reaching the UI rendering components.
The technical crux of the evasion lies in targeting the method _handleNewDomainData:. As Jamf researchers articulate, this method is the designated iOS trigger for updating sensor status visibility across the system. By successfully hooking this single, critical method, Predator intercepts all upstream updates regarding sensor activity.
The method of suppression is remarkably efficient and subtle. The malware achieves this by nullifying the primary object responsible for aggregating and managing these sensor updates: the SBSensorActivityDataProvider. In the context of Objective-C, the programming language underpinning much of iOS, attempting to call methods on a null object results in silent failure; the operation is ignored without generating an error or crashing the process. Consequently, SpringBoard never receives the command to update the status bar, and the tell-tale green or orange dot remains absent. Because SBSensorActivityDataProvider serves as the centralized hub for all sensor data reporting, neutralizing it via this single hook effectively disables both the camera and microphone indicators simultaneously.
This approach highlights a sophisticated understanding of the internal architecture of Apple’s mobile operating system. Rather than trying to surgically erase the drawing commands for the dots—a complex and brittle process prone to breaking with minor OS updates—Predator intercepts the data source itself, starving the indicator system of the information it needs to function.
Interestingly, the analysis also uncovered "dead code" within the malware payload. This dormant segment suggested an earlier, perhaps abandoned, development path that aimed to hook the SBRecordingIndicatorManager directly. This manager is ostensibly the more direct interface for controlling the visual indicators. The fact that Predator’s final, deployed mechanism targets the data provider (SBSensorActivityDataProvider) upstream suggests the developers prioritized robustness and comprehensive coverage over targeting the final display component, avoiding potential reliance on a structure that Apple might modify more frequently.

The implications extend beyond standard camera/mic usage. Predator is also known to facilitate the recording of Voice over IP (VoIP) calls. For these specific types of recordings, the module responsible for VoIP capture reportedly lacks its own native indicator suppression logic. This deficiency mandates a reliance on the central HiddenDot function within SpringBoard to maintain operational stealth during these specific surveillance activities.
Furthermore, the initial compromise necessary for this level of control involves bypassing standard security protocols for camera access itself. Jamf’s analysis indicates that camera engagement is facilitated by a separate module that employs low-level techniques. This includes identifying relevant internal camera functions through ARM64 instruction pattern matching and utilizing Pointer Authentication Code (PAC) redirection to circumvent established system permission checks. This multi-layered approach—zero-day exploitation for initial access, kernel privilege escalation for persistence, and dynamic patching of UI components for operational concealment—demonstrates a threat actor operating at the pinnacle of mobile exploit development.
The success of this evasion technique underscores a fundamental tension in mobile security: the arms race between platform vendors and sophisticated attackers. While Apple continues to harden iOS with features like Secure Boot, hardware-backed security enclaves, and mandatory visual indicators, advanced persistent threats (APTs) and well-funded commercial surveillance entities continuously probe these defenses. The fact that a mechanism exists to negate a fundamental user trust feature, leveraging only post-exploitation privileges, raises serious questions about the efficacy of OS-level defenses against an adversary that has achieved kernel control.
Industry Implications and the Commercial Spyware Market
The development and deployment of tools like Predator have profound ramifications extending far beyond the individual victim. Intellexa, the developer behind Predator, has faced international scrutiny, including sanctions from the U.S. government for its alleged role in spying operations targeting American citizens. This incident reinforces the reality that commercial spyware is not merely a tool for nation-states but a marketable product sold to various state and non-state actors globally.
The existence of such a refined, post-exploitation evasion module significantly increases the market value and perceived effectiveness of the spyware package. For governments or agencies purchasing such tools, the ability to monitor targets without leaving digital breadcrumbs—the blinking dot being a major breadcrumb—is paramount. It ensures long-term, undetected access, allowing for sustained intelligence gathering over months or years.

This development forces security vendors and enterprise mobility management (EMM) providers, like Jamf, into a reactive posture. While EMM platforms are excellent at managing configuration and detecting known malware signatures, they often struggle against novel, highly evasive runtime manipulations within core system processes like SpringBoard, especially on jailbroken or compromised devices. The technical details uncovered by Jamf are vital precisely because they provide the necessary intelligence for defensive vendors to develop advanced runtime integrity checks capable of spotting these dynamic function hooks.
The reliance on kernel access also highlights the ongoing vulnerability of the mobile ecosystem to supply chain attacks or targeted spear-phishing campaigns capable of delivering the initial jailbreak or kernel exploit. Even if Apple patches the initial infection vector, the consequences of a successful compromise—the installation of persistent surveillance software capable of this level of invisibility—remain dire.
Expert Analysis: The Significance of SpringBoard Hooking
From a security engineering perspective, hooking SpringBoard is the ultimate privilege escalation in terms of visibility control. SpringBoard is essentially the privileged application shell for the entire user experience. Manipulating it is akin to editing the script of a play while it is being performed; the audience sees only the revised actions, not the cues that triggered them.
The technique utilized by Predator—targeting the data provider upstream rather than the display manager downstream—is architecturally superior for persistence and evasion. The SBRecordingIndicatorManager might be subject to signature-based checks or integrity monitoring by Apple’s internal security mechanisms. However, intercepting the SBSensorActivityDataProvider before data serialization and presentation effectively hides the activity at the source. This is a classic example of "covering your tracks" by manipulating the system’s internal state rather than trying to patch the visual output itself.
Furthermore, the mention of "dead code" suggests an iterative development process where operators refine their methods based on internal testing or feedback. The shift away from directly hooking the indicator manager toward nullifying the data provider indicates a calculated decision favoring a more fundamental, less traceable form of system manipulation.
The reliance on ARM64 instruction pattern matching and PAC redirection for camera access speaks to a deep expertise in low-level mobile architecture. Pointer Authentication Codes (PACs) are a modern security feature designed to prevent memory corruption attacks by signing pointers. Bypassing this requires an understanding of how PACs are generated and verified within the execution flow, suggesting the developers are leveraging knowledge gained from either exhaustive reverse engineering or access to extremely detailed internal documentation or exploits.
Future Impact and Defensive Trends
This technical disclosure serves as a stark warning for the future of mobile security. As operating systems like iOS become increasingly locked down and rely on hardware-backed security features, the value of achieving kernel-level compromise skyrockets. Once achieved, the attacker can leverage software engineering techniques, rather than complex vulnerability chains, to maintain dominance.
The future of mobile defense against this caliber of threat will likely shift toward more rigorous runtime application self-protection (RASP) capabilities integrated deeply into endpoint security solutions. These next-generation defenses must move beyond traditional signature matching and focus on behavioral analysis of system processes, particularly SpringBoard and critical services like mediaserverd.
Defenders will need to develop specialized monitors capable of:
- Integrity Checking of Critical System Objects: Continuously verifying that system objects, such as
SBSensorActivityDataProvider, have not been replaced, nullified, or had their method dispatch tables hijacked. - Anomaly Detection in Process Communication: Monitoring for unusual communication patterns or exception port activity between core system daemons (like SpringBoard) and user-space processes, as noted in Jamf’s observations.
- Hardware-Assisted Monitoring: Leveraging advancements in processor security features to detect unauthorized modifications to executable memory regions, even at the kernel level, though this remains challenging on production devices without specialized hardware access.
The case of Predator hiding its presence by manipulating the very indicators designed for transparency highlights a fundamental challenge: if a user cannot trust the basic signals provided by the operating system, the entire concept of user privacy on that platform is undermined. The ongoing cat-and-mouse game between platform developers and sophisticated spyware manufacturers necessitates a perpetual escalation in defensive research to ensure that transparency controls remain trustworthy, even in the face of adversaries equipped with resources approaching those of state actors.

