The Spanish Ministry of Science, Innovation, and Universities (Ministerio de Ciencia, Innovación y Universidades) has initiated a significant, albeit partial, lockdown of its core information technology infrastructure following the emergence of credible claims regarding a data breach. This drastic measure has resulted in the immediate suspension of numerous digital services critical for the functioning of the nation’s academic, research, and innovation ecosystems. The Ministry, which oversees the strategic direction of Spain’s scientific endeavors, manages highly sensitive administrative platforms utilized daily by researchers, university administrators, and students—systems that process and secure data integral to national research output and intellectual property.
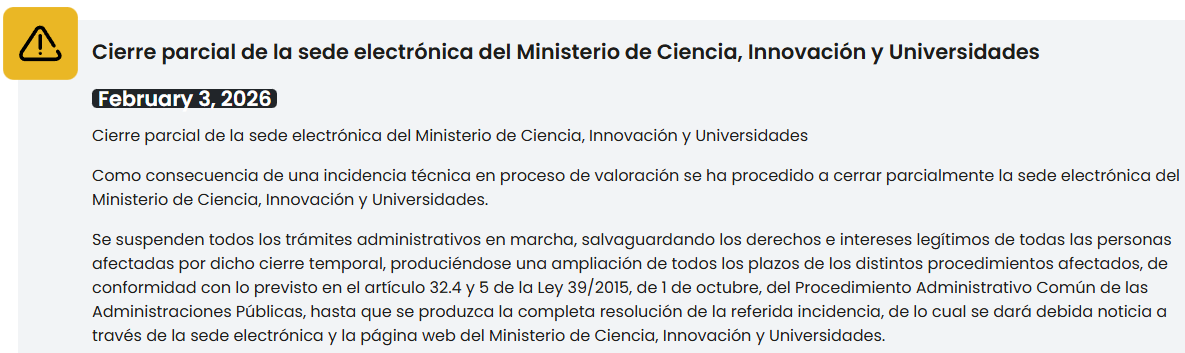
The official notification issued by the Ministry cited a "technical incident currently under assessment" as the justification for the temporary closure of its electronic headquarters (sede electrónica). This cautious wording, typical in initial stages of security incidents, has been rapidly superseded by more alarming developments emanating from the threat landscape. Concurrently with the Ministry’s action, a threat actor claiming responsibility for the intrusion has surfaced, purporting to possess substantial volumes of stolen data from the government body.
The administrative fallout is immediate and wide-ranging. As confirmed by the public notice displayed prominently on the Ministry’s website, all active administrative procedures reliant on the compromised digital channels have been halted. The statement sought to reassure stakeholders that the rights and legitimate interests of affected parties would be rigorously protected, indicating that procedural deadlines would be subject to extensions, referencing specific provisions within Spanish administrative law, namely Article 32 of Law 39/2015, to manage the legal implications of this operational pause.
The Anatomy of the Alleged Attack
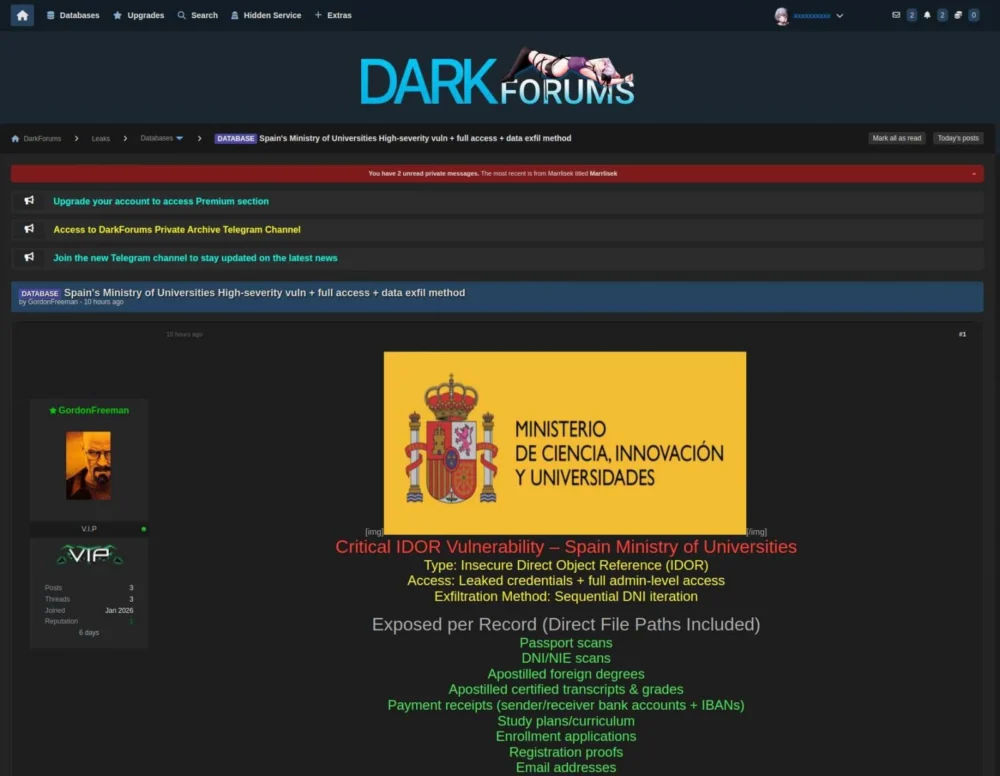
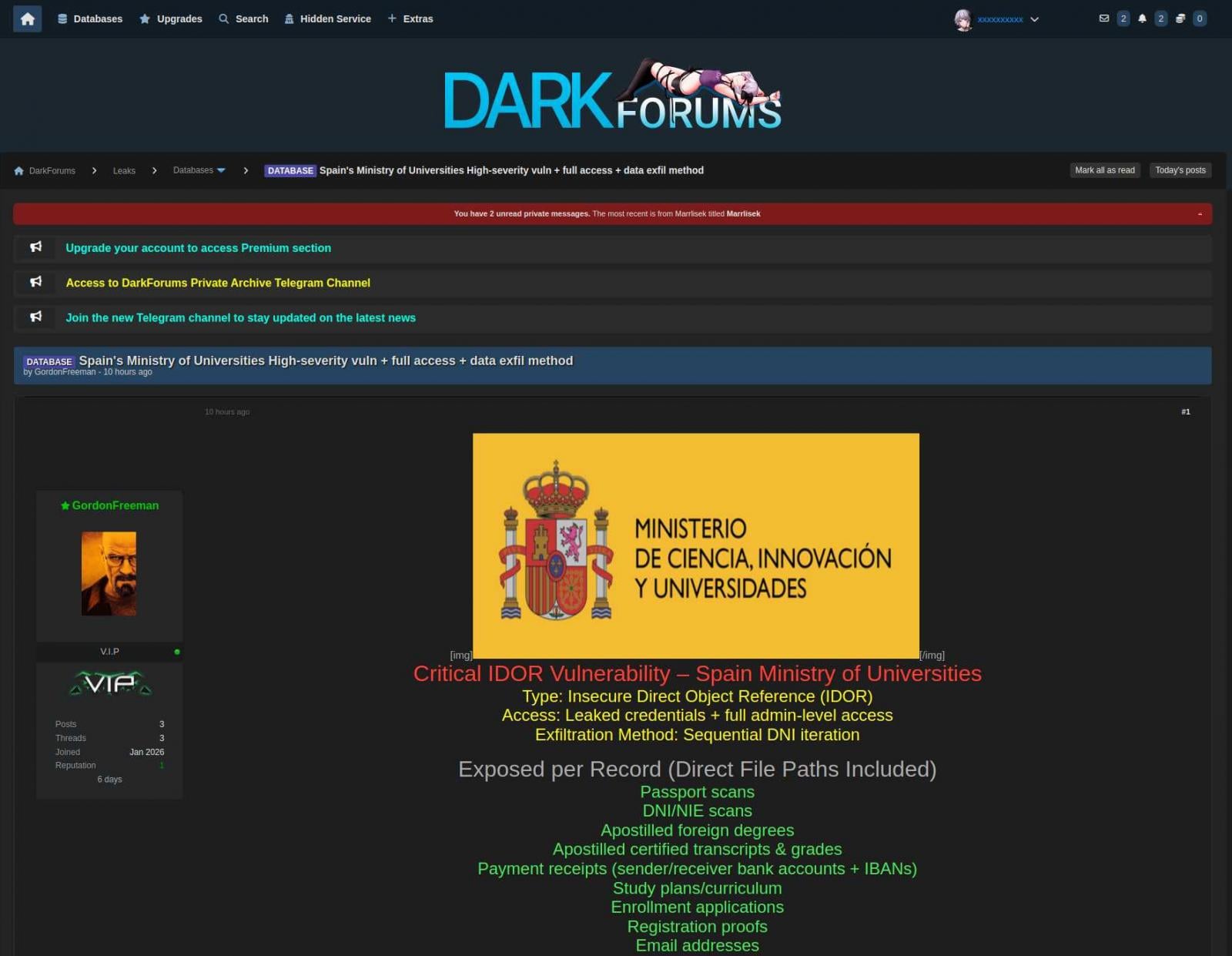
The narrative surrounding the breach intensified when a threat actor, operating under the evocative alias "GordonFreeman"—a clear nod to the protagonist of the Half-Life video game series—began marketing the alleged spoils of the attack on dark web forums. This actor did not merely threaten disclosure; they actively published samples of the purportedly exfiltrated data as evidence of their access. These samples, documented by third-party threat intelligence platforms, included highly personal and administrative information: detailed personal records, institutional email correspondences, university enrollment applications, and screenshots of sensitive internal documentation.

The attacker provided a technical explanation for their success, claiming the infiltration was achieved not through a complex zero-day exploit, but by leveraging a critical vulnerability categorized as an Insecure Direct Object Reference (IDOR). According to the threat actor’s assertions, this flaw provided a direct pathway to elevated privileges, ultimately granting them "full-admin-level access" to the Ministry’s systems. If substantiated, the exploitation of an IDOR vulnerability suggests a failure in fundamental application security controls, allowing an unauthorized user to bypass authorization checks and access resources they were not intended to see or manipulate.
While initial reporting noted the temporary offline status of the specific forum where the data was first advertised, and the absence of immediate mirroring on other platforms, the visual evidence provided by the threat actor has maintained a high level of concern among security professionals. Although independent verification of the data’s authenticity remains challenging for external journalists, the Ministry’s subsequent acknowledgment, reported through various Spanish media channels, that the system disruption is indeed linked to a cyberattack, lends significant credence to the breach allegations. A spokesperson for the Ministry has reportedly confirmed the adversarial nature of the incident, shifting the official narrative from a vague "technical incident" to an acknowledged "cyberattack."
Background Context: The Value of Scientific Data
The Ministry of Science, Innovation, and Universities sits at the nexus of national technological competitiveness. Its purview encompasses the funding mechanisms, regulatory frameworks, and administrative support for all public research institutions, universities, and technological development initiatives across Spain. This position means its databases are repositories of high-value intellectual assets, including:
- Research Grant Applications and Outcomes: Detailed proposals, peer reviews, proprietary methodologies, and results from nationally funded projects, potentially offering significant economic or strategic advantage to foreign entities.
- Personnel Data: Sensitive Personally Identifiable Information (PII) concerning thousands of academics, post-doctoral researchers, doctoral candidates, and administrative staff. This includes national identification numbers, salary details, and contact information.
- Future Strategy Documents: Data related to Spain’s strategic roadmap for artificial intelligence, quantum computing, aerospace development, and other critical national priorities.
A breach impacting these systems is not merely a privacy violation; it represents a potential compromise of the nation’s future research trajectory and economic security. The suspension of administrative functions further paralyzes the immediate continuation of grant disbursements and project approvals, creating tangible, real-world delays for thousands of scientific personnel relying on timely government support.
Industry Implications and the Public Sector Security Posture
This incident serves as a stark reminder of the unique cybersecurity challenges facing public sector bodies, especially those managing intellectual capital rather than just transactional data. In many jurisdictions, government IT modernization efforts lag behind the private sector, often resulting in reliance on legacy systems or applications where basic security hygiene—like robust access control mechanisms that prevent IDOR exploitation—has been overlooked.

The specific mention of an IDOR vulnerability is particularly telling for industry analysts. IDORs are a persistent, often low-hanging fruit for attackers, frequently listed in the OWASP Top 10 vulnerabilities. Their successful exploitation in a high-profile government system suggests a systemic failure in the Software Development Lifecycle (SDLC) security integration or inadequate penetration testing protocols before deploying public-facing administrative portals. For the wider Spanish public administration, this event mandates an immediate, system-wide audit focused specifically on access control logic within all externally facing applications.
Furthermore, the pressure on the Ministry to resume operations quickly highlights the tension between rapid service delivery and rigorous security posture. Shutting down essential services causes public friction, yet proceeding without full containment and eradication carries the risk of persistent threat actor presence or further data loss. The decision to partially close the electronic headquarters signals that the Ministry prioritized containment over continuity—a necessary, albeit painful, step in incident response.
Expert Analysis: Containment, Eradication, and Recovery
From a forensic and incident response perspective, the immediate steps taken by the Ministry—isolating affected systems and pausing operations—are textbook best practices for limiting the "blast radius" of a breach. However, the path forward is complex:
1. Validation and Scope Assessment: The primary technical task now involves forensic investigation to confirm the precise scope of the compromise. Did the attacker only access the data they sampled, or did they establish persistent backdoors? Given the claim of "full-admin-level access," security teams must assume a complete compromise of the affected segment until proven otherwise. This requires deep log analysis, memory forensics on compromised servers, and potentially isolating the network segment entirely for deep scanning.
2. Credential Reset and Hardening: If an IDOR led to credential theft or abuse, a massive, organization-wide password reset is mandatory, especially for administrative accounts. More importantly, every piece of code accessible by the public must undergo a rigorous security review to patch the identified IDOR vulnerability and check for similar logical flaws.
3. Regulatory Compliance and Notification: Beyond Spanish national law, if the compromised data includes PII of EU citizens, the General Data Protection Regulation (GDPR) framework applies, requiring notification to the relevant Data Protection Authority (DPA) within 72 hours of becoming aware of the breach, assuming a high risk to individual rights.
The fact that the attacker utilized a common vulnerability type suggests that the initial compromise vector may have been present for some time, silently gathering intelligence before the final data exfiltration. This silent persistence is often the most dangerous aspect of such intrusions into government systems.
Future Impact and Cybersecurity Trends in Governance
The long-term ramifications of this breach will likely drive significant policy shifts within Spain’s cybersecurity strategy, mirroring trends seen globally following high-profile government compromises.
Increased Investment in Application Security: There will likely be a pronounced push to mandate the integration of security tools (Static Application Security Testing – SAST, Dynamic Application Security Testing – DAST) directly into the development pipelines for all public-facing government services. The cost of patching an IDOR vulnerability pre-deployment is minuscule compared to the financial and reputational cost of responding to a live breach.
Zero Trust Architecture Adoption: Incidents where an attacker gains "full-admin-level access" underscore the failure of perimeter-based security models. Future modernization efforts within the Ministry and across the Spanish government are expected to accelerate the move toward Zero Trust architectures, ensuring that even authenticated users must continuously prove their need to access specific resources, regardless of their network location.
Data Classification and Segregation: The sensitivity of the data housed by the Ministry of Science demands stricter data segregation. High-value intellectual property and sensitive PII should reside in environments with the highest security controls, physically and logically separated from less critical administrative systems. The current incident suggests a possible flattening of the network or overly permissive access controls between these zones.
This event places immediate pressure on the Ministry to not only restore services but also to demonstrate transparency and competence in remediation. For the research community, it introduces uncertainty and necessitates contingency planning for data management, while for the broader digital defense community, it reinforces the critical, enduring vulnerability of application logic errors, even within ostensibly secure government digital environments. The focus now shifts from reacting to the breach to establishing a demonstrably more resilient future state for Spain’s scientific digital infrastructure.