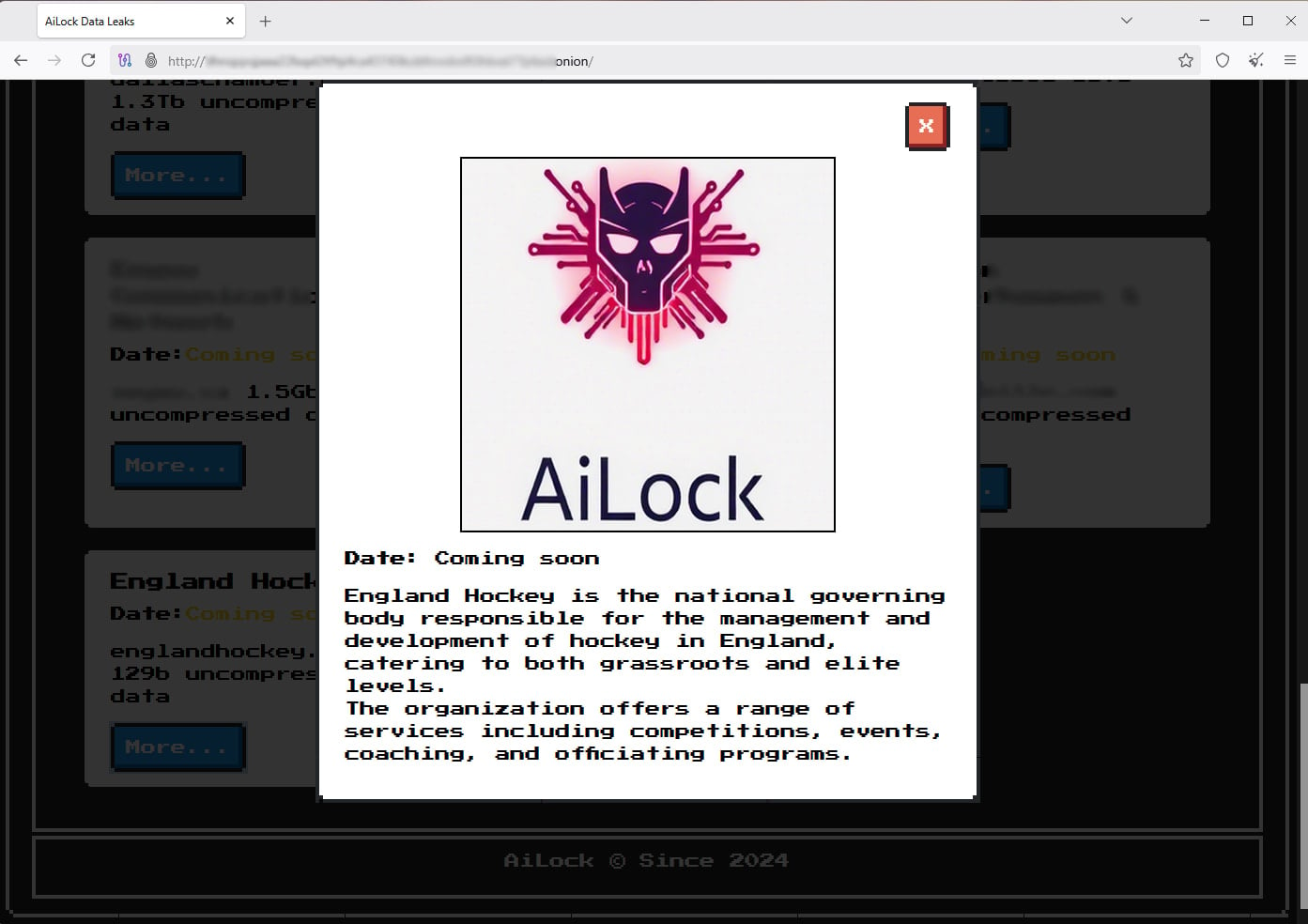
England Hockey, the national governing body responsible for the stewardship, development, and regulation of field hockey across England, is currently navigating a significant cybersecurity incident following public claims made by the AiLock ransomware syndicate. The organization has confirmed it is treating the matter as a high-priority investigation after the threat actor surfaced on their data leak site, alleging the compromise and exfiltration of a substantial cache of organizational data—reportedly amounting to 129 gigabytes. This development casts a shadow over the institution that oversees operations for approximately 150,000 registered club players, 15,000 coaches and officials, and a network spanning over 800 affiliated clubs nationwide, highlighting vulnerabilities that resonate far beyond the pitch.
The gravity of the situation stems not only from the purported volume of data stolen but also from the nature of the entity targeted. National sports governing bodies, while sometimes perceived as soft targets compared to major financial institutions, hold sensitive information pertaining to minor participants, financial records, administrative strategies, and potentially sensitive personal data of elite athletes and staff. The mere public assertion by AiLock puts England Hockey immediately on the defensive, necessitating swift, transparent, yet cautious communication regarding the scope of the potential impact.
In response to the allegations, England Hockey released a measured statement confirming awareness of the incident and the subsequent claims made by the group. Their immediate action plan has centered on comprehensive internal triage, augmented by the engagement of specialized external cybersecurity forensics experts. Furthermore, the organization has confirmed proactive engagement with relevant regulatory and law enforcement agencies, a crucial step in managing a modern data breach scenario that involves extortion demands. The organization has explicitly stated its inability to provide granular details concerning the specifics of the compromised data at this juncture, citing the imperative to allow the ongoing investigation to proceed without prejudice. They emphasized, however, that data security remains paramount, and establishing precisely what data, if any, has been affected is the absolute core focus of their current operational efforts.
The Profile of the Adversary: Understanding AiLock’s Modus Operandi
The identity of the threat actor involved provides critical context to the potential risk profile. AiLock is identified as a relatively emergent ransomware strain that has rapidly adopted the established tactic of "double extortion." This method involves two primary pressure points: the encryption of the victim’s internal systems, rendering data inaccessible, and the theft and threatened publication of that sensitive data. This dual threat is designed to maximize the pressure on the victim to comply with ransom demands, as both operational continuity and reputational integrity are held hostage.
Cybersecurity documentation, notably reports tracing the group’s emergence around early April 2025, indicates that AiLock employs sophisticated techniques. Researchers have observed the group leveraging privacy and data protection legislation violations as a specific bargaining chip during negotiations. Their standard timeline imposes a strict 72-hour window for victims to initiate contact and begin dialogue, followed by a five-day ultimatum before the exfiltrated data is publicly dumped onto their leak site. This structured, time-sensitive approach is designed to capitalize on organizational panic and slow internal decision-making processes.

From a technical standpoint, analysis of the AiLock payload reveals a robust encryption mechanism utilizing a combination of modern cryptographic standards, including ChaCha20 for file encryption, often paired with NTRUEncrypt, a form of lattice-based cryptography that presents unique challenges for decryption. Encrypted files are typically marked with the distinctive .AILock extension, and a ransom note is strategically deposited across all compromised directories, serving as immediate proof of compromise. While the initial breach that led to data exfiltration may have been achieved through standard vectors—such as exploiting unpatched vulnerabilities, compromised remote access tools, or successful phishing campaigns—the subsequent encryption and extortion phase is what defines the AiLock threat.
Industry Implications for UK Sports Bodies
The potential compromise of England Hockey serves as a stark reminder to the wider ecosystem of national and regional sports organizations across the United Kingdom. These bodies are custodians of vast amounts of personally identifiable information (PII), particularly concerning youth participation, medical records for elite athletes, and the proprietary administrative data required to run national leagues.
For many non-profit or semi-commercial entities like sports governing bodies, the financial impact of a ransomware attack extends beyond the potential ransom payment. The costs associated with forensic investigation, mandatory regulatory notification (especially under GDPR guidelines), system rebuilding, and reputational damage can cripple budgets designed for grassroots development or athlete support. In the context of UK sports, where funding is often closely scrutinized, a major security failure can trigger audits and jeopardize future grant funding from bodies like Sport England.
The implications also extend to the volunteer and coaching infrastructure. If the compromised 129GB includes sensitive details related to background checks (DBS checks for coaches), disciplinary records, or internal communications, the organization faces complex legal and ethical obligations regarding the protection of these individuals, many of whom operate on a voluntary basis. A failure to adequately secure this data undermines the trust placed in the governing body by parents, participants, and volunteers alike.
Expert Analysis: Beyond the Initial Breach
From a cybersecurity perspective, the focus must rapidly shift from initial intrusion to data residency and impact assessment. The fact that AiLock claims to have exfiltrated 129GB suggests a significant lateral movement within England Hockey’s network environment before the data was packaged for extraction. This level of data staging implies that the threat actors likely maintained persistence for some time, probing various network segments.
The key technical question for investigators will be the segregation of data. Were operational technology (OT) systems—if they interface with any facility management or scheduling software—isolated from the main administrative networks holding PII? Furthermore, the role of cloud services, often used by modern sports organizations for membership management or communication platforms, must be thoroughly examined. Did the threat actors pivot from an on-premise vulnerability to gain access to third-party cloud environments?
The decision by England Hockey not to comment on the specific nature of the data is standard protocol, but it places the onus on them to conduct a rapid and definitive classification. If GDPR-protected PII (names, addresses, dates of birth, financial data) is confirmed to be present in the exfiltrated set, the timeline for reporting to the Information Commissioner’s Office (ICO) becomes critically short, typically within 72 hours of becoming "aware" of the breach. The threat actor’s tactic of weaponizing privacy law violations suggests they are highly attuned to these regulatory timelines, potentially using the impending regulatory deadline as further leverage during ransom negotiations.
The threat actor’s use of advanced encryption like NTRUEncrypt—a post-quantum cryptographic concept gaining traction in malware—is noteworthy. While the immediate threat is data leakage, the encryption itself signifies a technologically aware adversary, moving beyond commodity malware toward techniques that may offer greater operational resilience or evasion capabilities against standard security tooling.
Future Trajectories and Resilience Building
This incident compels a systemic review across the UK sporting sector regarding cyber maturity. Many smaller sports organizations operate with legacy IT infrastructure, minimal dedicated security staff, and often rely on basic off-the-shelf antivirus solutions. The AiLock incident should serve as a loud wake-up call, emphasizing that comprehensive, defense-in-depth strategies are no longer optional luxuries but foundational requirements for any entity managing public trust and personal data.
Future resilience efforts must incorporate several key areas:
- Zero Trust Architectures: Moving away from perimeter-based security to ensure that even if an attacker gains a foothold, their ability to move laterally and access high-value data repositories is severely restricted through micro-segmentation and strict access controls.
- Proactive Threat Hunting: Relying solely on detection tools is insufficient. Organizations must adopt continuous monitoring and proactive hunting for indicators of compromise, especially looking for signs of data staging and reconnaissance activity that precedes an actual exfiltration event.
- Incident Response Maturity: Regular, unannounced tabletop exercises simulating ransomware scenarios—including media management and regulatory reporting timelines—are essential. England Hockey’s current reliance on external specialists highlights the need for pre-vetted, on-call cyber response teams.
- Supply Chain Vigilance: Given the interconnected nature of modern operations, England Hockey must audit the security postures of its primary technology vendors and membership management platforms, as these often represent the weakest links exploited by ransomware groups.
While England Hockey manages this immediate crisis, the broader community must learn from the potential fallout. The incident underscores a growing trend where cybercriminals are increasingly targeting mid-tier organizations—those with significant data holdings but potentially less sophisticated defenses than FTSE 100 companies—as a lucrative and less scrutinized avenue for profit. The resolution of this investigation will not only determine the fate of England Hockey’s data integrity but will also serve as a crucial case study for national sports bodies on managing the high-stakes theatre of modern cyber extortion. Until confirmation is provided, all stakeholders associated with English field hockey are advised to implement heightened vigilance against social engineering tactics and unsolicited digital communications, recognizing that the attacker’s primary goal is exploitation, whether through payment or public embarrassment.

