The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a stark warning to federal civilian agencies, designating two recently remediated vulnerabilities within the widely deployed RoundCube Webmail client as actively exploited in the wild. This designation automatically triggers a binding operational directive, mandating that all affected Federal Civilian Executive Branch (FCEB) agencies must fully patch their environments against these specific security weaknesses within a compressed three-week deadline, set for March 13th. This aggressive timeline underscores the immediate and significant risk CISA perceives these flaws pose to critical government infrastructure, aligning with the mandate established under Binding Operational Directive (BOD) 22-01, which emphasizes rapid remediation of cataloged threats.
RoundCube Webmail, a foundational component in many digital ecosystems, serves as the default web interface for email access across numerous hosting environments, notably integrating deeply with the cPanel web hosting control panel since 2008. This extensive deployment footprint means that a vulnerability in RoundCube instantly scales into a systemic risk across a vast swath of public-facing internet services and internal agency communication portals.
The first vulnerability compelling this emergency action is cataloged as CVE-2025-49113. This flaw represents a critical Remote Code Execution (RCE) vulnerability. Its inclusion in CISA’s Known Exploited Vulnerabilities (KEV) Catalog signifies that threat actors are not merely scanning for it but are actively leveraging it to gain unauthorized control over vulnerable servers. This particular exploit path was first brought to wider attention by the Shadowserver Foundation shortly after its patch release in June 2025, revealing a troubling gap between vendor disclosure and operational security implementation. At that initial warning stage, security researchers identified an alarming potential exposure, estimating that over 84,000 RoundCube installations globally remained susceptible to attack, presenting an immediate, large-scale attack surface.
The second entry demanding immediate attention is CVE-2025-68461. This vulnerability, patched approximately two months prior in December 2025, presents a fundamentally different, yet equally insidious, risk: a low-complexity Cross-Site Scripting (XSS) flaw. The specific vector involves the improper handling of the animate tag within Scalable Vector Graphics (SVG) documents rendered by the webmail client. Crucially, the advisory noted that exploitation does not require prior authentication, meaning any unauthenticated external actor could potentially inject malicious scripts into the browser sessions of legitimate RoundCube users. When exploited, such an XSS flaw can lead to session hijacking, credential theft, or the redirection of users to malicious sites, severely compromising user trust and data integrity. In response to the discovery of CVE-2025-68461, the RoundCube security team issued urgent advisories alongside the release of maintenance versions 1.6.12 and 1.5.12, strongly urging administrators to migrate immediately from the affected 1.6.x and 1.5.x branches.
CISA’s decision to incorporate both flaws into the KEV Catalog on a Friday underscores the severity assessment—flaws are added only when CISA has credible evidence of active exploitation in the wild that poses a demonstrable risk to the federal enterprise. While CISA’s public documentation often omits the specific details of the ongoing exploitation campaigns, the inclusion itself acts as a digital tripwire for federal IT and security teams.
The Broader Ecosystem Under Scrutiny
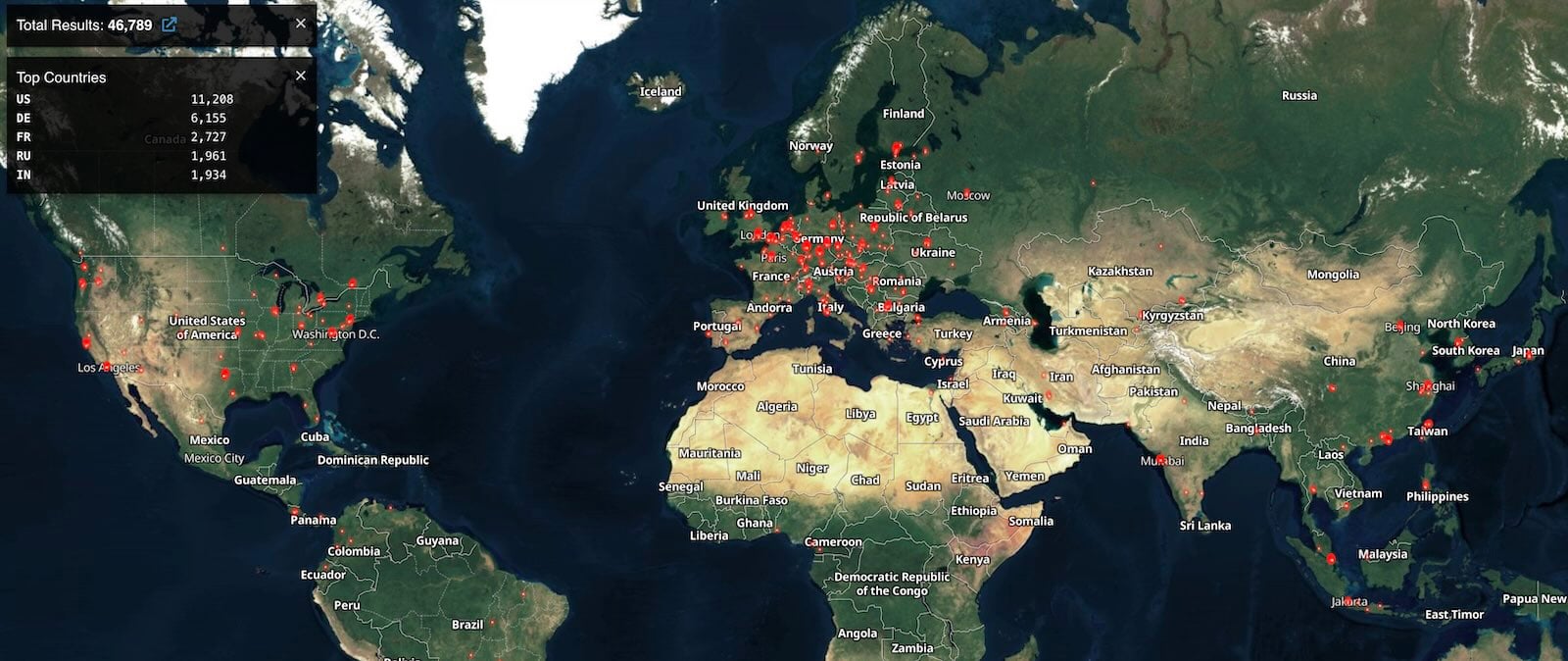
The threat landscape surrounding RoundCube is not new; it is a recurring pattern that reflects the inherent risks associated with legacy or widely adopted open-source web applications. Internet scanning services, such as Shodan, currently map more than 46,000 active RoundCube instances accessible via the public internet. While the exact correlation between these discoverable instances and the specific vulnerabilities CVE-2025-49113 and CVE-2025-68461 remains obscured by attacker tradecraft, the sheer volume of internet-facing assets suggests that a significant portion of the federal network perimeter is running potentially exposed software.
This situation highlights a perennial challenge in cybersecurity governance: the disparity between when a patch is released and when it is universally applied across diverse organizational infrastructures. For federal agencies, where procurement cycles, change management protocols, and legacy system maintenance can create significant lag times, zero-day exploitation often begins almost immediately upon patch release, capitalizing on this inherent delay.
The KEV Catalog is not merely a patch reminder; it functions as a prioritized risk management tool based on observed adversary behavior. The inclusion of these two RoundCube flaws elevates them above thousands of other known but currently unexploited vulnerabilities. Furthermore, these are not isolated incidents. CISA’s catalog already lists ten other historical or currently active RoundCube vulnerabilities, demonstrating that this platform has historically been a favored vector for espionage and cybercrime operations.
Industry Implications and Expert Analysis
The active exploitation of both an RCE (CVE-2025-49113) and a high-impact XSS (CVE-2025-68461) concurrently within the same software suite presents a multi-vector attack opportunity for sophisticated adversaries.
From an expert perspective, the RCE flaw is the more immediately catastrophic. RCE grants an attacker the ability to execute arbitrary commands on the underlying server. This typically leads to full system compromise, allowing the installation of persistent backdoors, data exfiltration, or lateral movement into internal agency networks. For state-sponsored actors, an RCE in an email gateway is an invaluable foothold for intelligence gathering.
The XSS vulnerability, while less destructive at the server level, is highly effective for targeted, large-scale phishing or credential harvesting campaigns against end-users. In a government context, compromising the browser session of an authenticated user can bypass multi-factor authentication (MFA) protections if the session cookie is stolen, leading to direct access to sensitive correspondence or internal portals. The low complexity reported for the SVG-based XSS means that rudimentary scripts can be crafted, lowering the barrier to entry for less sophisticated criminal groups seeking quick financial gains or data reconnaissance.

This dual-threat scenario forces security architects to adopt a layered defense strategy. Patching for RCE must be immediate to protect the infrastructure integrity, while implementing web application firewalls (WAFs) capable of inspecting and blocking malicious SVG payloads becomes critical to mitigating the XSS risk until the patch is fully deployed across all endpoints.
Historical Context: RoundCube as a Geopolitical Target
The history of high-profile compromises involving RoundCube underscores why CISA treats these updates with such urgency. The platform has repeatedly been targeted by well-resourced, state-affiliated threat actors, often in campaigns designed to breach sensitive government and corporate communications.
A notable precursor involved a stored XSS vulnerability (CVE-2023-5631). This specific flaw was leveraged in coordinated operations by the Russian hacking group Winter Vivern (also known as TA473) to conduct zero-day attacks specifically aimed at European governmental organizations. Such campaigns illustrate a pattern: compromise the common entry point (email) to achieve strategic intelligence objectives. Furthermore, the Russian state-sponsored cyber-espionage group APT28 has also historically exploited RoundCube weaknesses to compromise Ukrainian government email systems, confirming the software’s status as a prime target in geopolitical cyber conflict.
For system administrators, the recurring nature of these high-severity flaws in RoundCube suggests that simply applying patches reactively is insufficient. There must be a proactive review of the application’s configuration, isolation from core network services, and strict adherence to input validation best practices, even for vendor-supplied components.
Future Impact and Mitigation Trends
The current situation serves as a powerful case study for the ongoing evolution of vulnerability management. The three-week deadline for FCEB agencies is a critical benchmark, but the real challenge lies in the thousands of non-federal organizations—state and local governments, educational institutions, and private sector entities relying on cPanel environments—that do not fall under BOD 22-01’s direct mandate.
The future impact of these exploited flaws will likely be seen in two areas: first, an increase in related forensic investigations across government and allied sectors; and second, a heightened scrutiny on the software supply chain security of widely used open-source components.
Security experts anticipate that organizations that fail to meet the March 13th deadline will likely face detection by threat intelligence feeds tracking the active exploitation of CVE-2025-49113 and CVE-2025-68461. The forensic trail left by attackers exploiting known, patched vulnerabilities often reveals systemic weaknesses in patching cadence rather than sophisticated zero-day discovery techniques.
Moving forward, the industry trend points toward greater reliance on automated vulnerability scanning and compliance tooling integrated directly into Continuous Integration/Continuous Deployment (CI/CD) pipelines and infrastructure monitoring. Relying on manual monthly patch cycles for externally facing services like webmail is proving operationally unsustainable against adversaries who move at machine speed. Infrastructure-as-Code (IaC) solutions and automated remediation platforms are increasingly being adopted by mature organizations to shrink the window between patch release and deployment from weeks to mere hours, effectively neutralizing the window of opportunity that threat actors currently exploit following public advisories.
For RoundCube administrators globally, the directive from CISA should serve as a universal catalyst: prioritize the update to versions 1.6.12 or 1.5.12 immediately. Given the critical nature of RCE and the pervasive threat of XSS, treating these vulnerabilities as if they were actively being used against one’s specific organization—even outside the federal mandate—is the only prudent cybersecurity posture. The persistence of these RoundCube compromises confirms that foundational email infrastructure remains a high-value target, demanding continuous vigilance far beyond the initial release of vendor security bulletins.