The digital supply chain is once again under siege as the persistent threat actor behind the GlassWorm malware campaign launches a significantly amplified and highly coordinated operation. Security researchers from multiple leading analysis groups—including Aikido, Socket, Step Security, and the OpenSourceMalware community—have collectively cataloged an alarming 433 distinct compromised software components this month alone. This latest surge demonstrates an unprecedented level of breadth, stretching across the ubiquitous development platforms of GitHub, the Node Package Manager (npm) registry, and the extension marketplaces of Visual Studio Code (VSCode) and OpenVSX.
This is not an isolated incident but a systematic campaign escalation. The attribution linking these diverse attacks to a single, determined threat actor is robust, derived from several converging indicators. Most notably, the threat group consistently employs the same unique Solana blockchain address for its Command-and-Control (C2) communications. Furthermore, the payloads discovered across the various ecosystems—from Python repositories to JavaScript extensions—are either identical or functionally equivalent, reinforcing the hypothesis of a centralized command structure managing this expansive operation.
The Evolution of a Sophisticated Threat
GlassWorm first surfaced to security analysts last October, immediately signaling a new level of sophistication in software supply chain exploitation. Its initial modus operandi relied on the deceptive use of "invisible" Unicode characters embedded within package metadata or source code. This technique was specifically engineered to bypass rudimentary static analysis tools and manual code review, allowing malicious code—designed to pilfer cryptocurrency wallet data and sensitive developer credentials—to remain concealed.
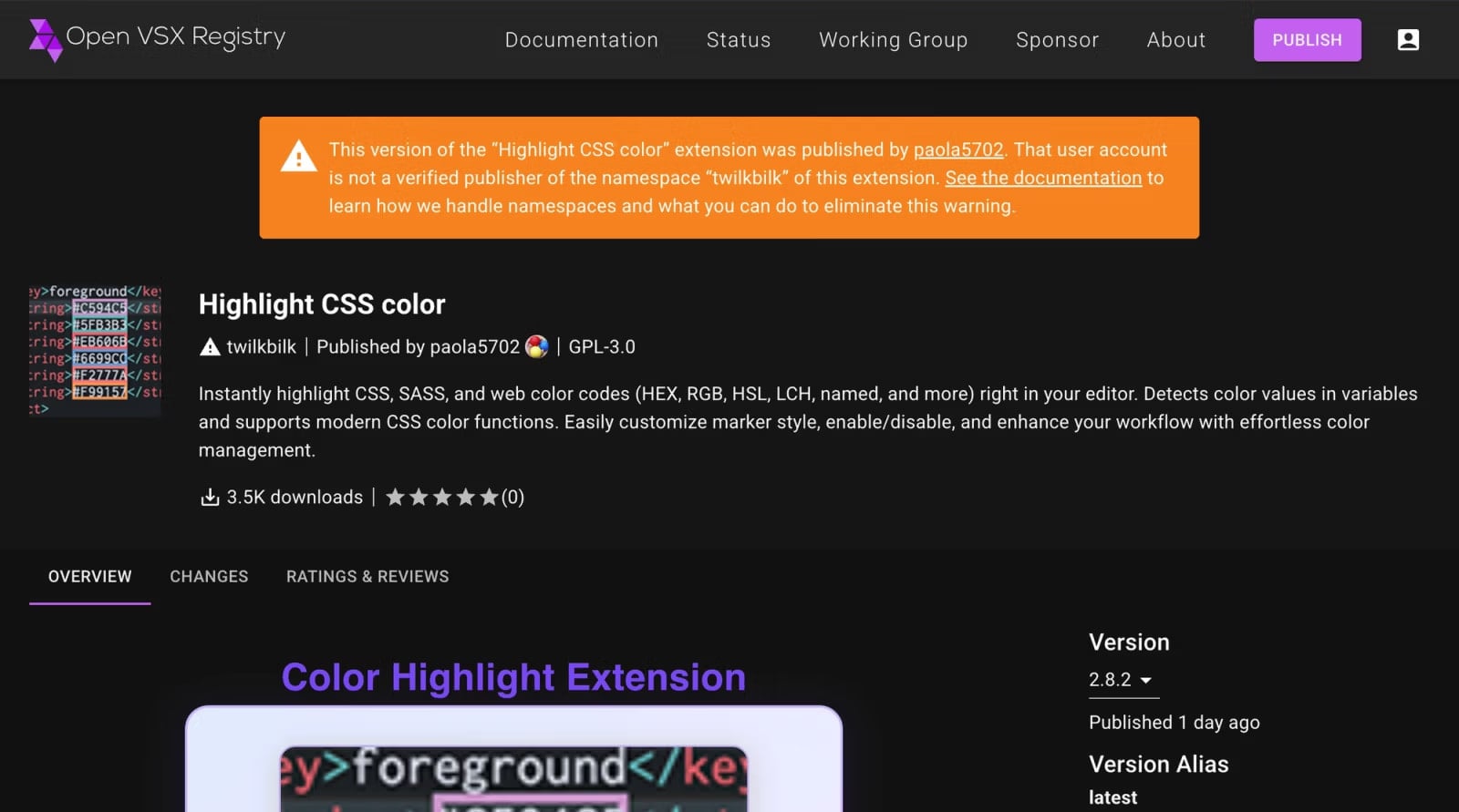
Since its initial detection, GlassWorm has proven resilient and adaptive, resurfacing in successive, escalating waves. The campaign demonstrated a clear strategic goal of maximizing reach by aggressively targeting platform extensions. Subsequent attacks successfully breached Microsoft’s official Visual Studio Code marketplace, alongside the OpenVSX registry, which serves as a crucial distribution point for IDEs that do not natively integrate with the proprietary VSCode marketplace. This expansion into IDE extension ecosystems, as noted by independent researchers like John Tuckner of Secure Annex, signifies a pivot toward directly compromising the developer’s immediate working environment.

The threat actor has also shown a capacity to tailor malware variants to specific operating systems. Earlier iterations included trojanized clients disguised as legitimate software for hardware wallets like Trezor and Ledger, specifically targeting macOS users. This was followed by an expansion that leveraged compromised OpenVSX extensions to distribute payloads aimed at macOS developers.
The current wave dwarfs previous efforts in scale and scope. While the exact list of affected repositories remains under active collation, the breadth indicates a systematic effort to saturate developer resources across multiple languages and tooling environments.
Technical Deep Dive: Compromise Vectors and C2 Infrastructure
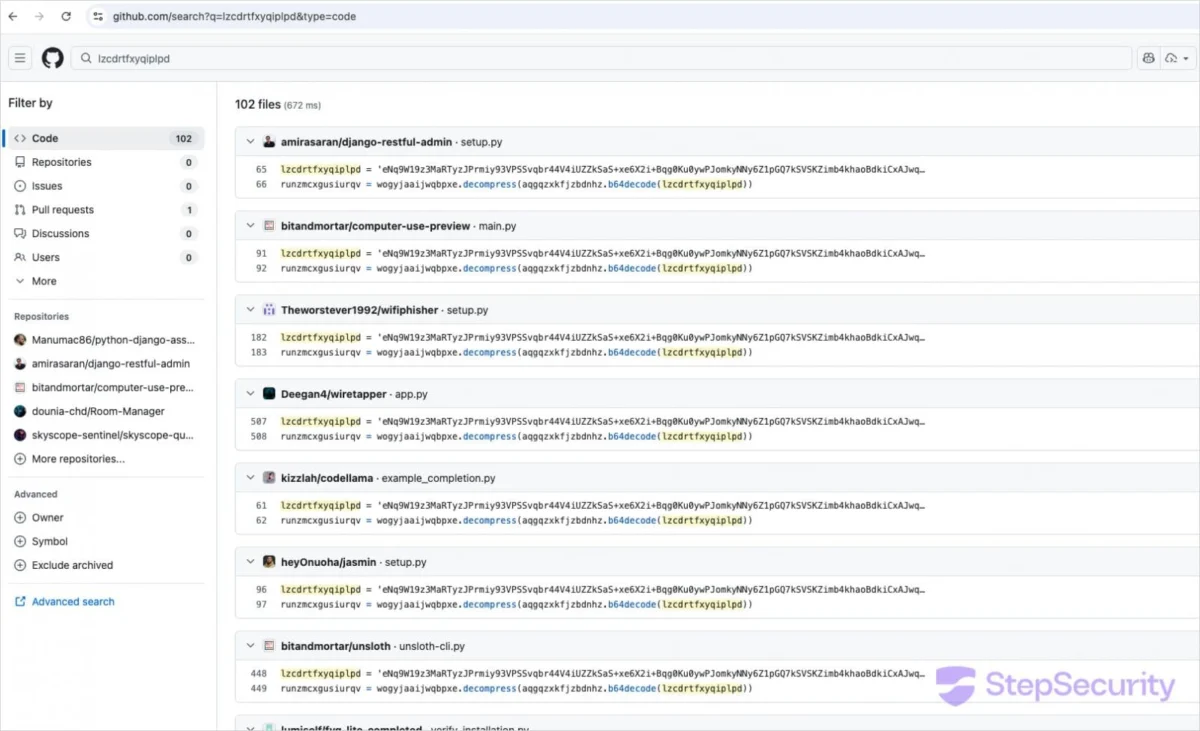
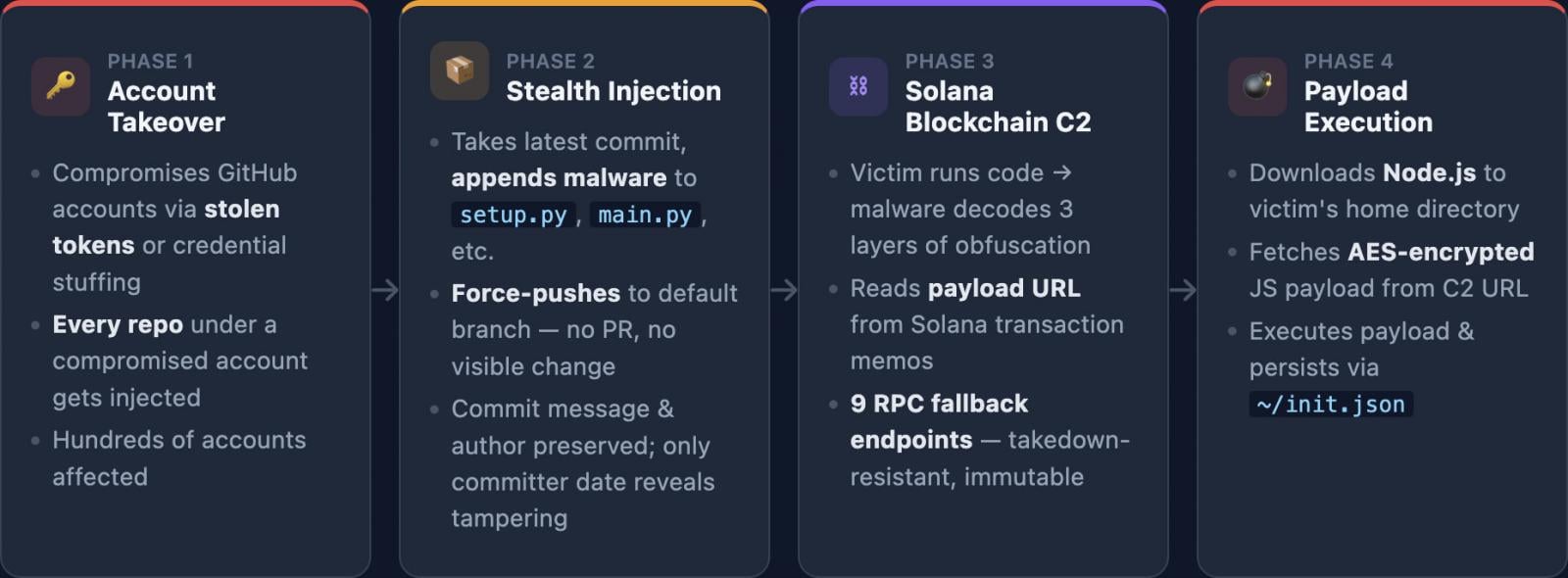
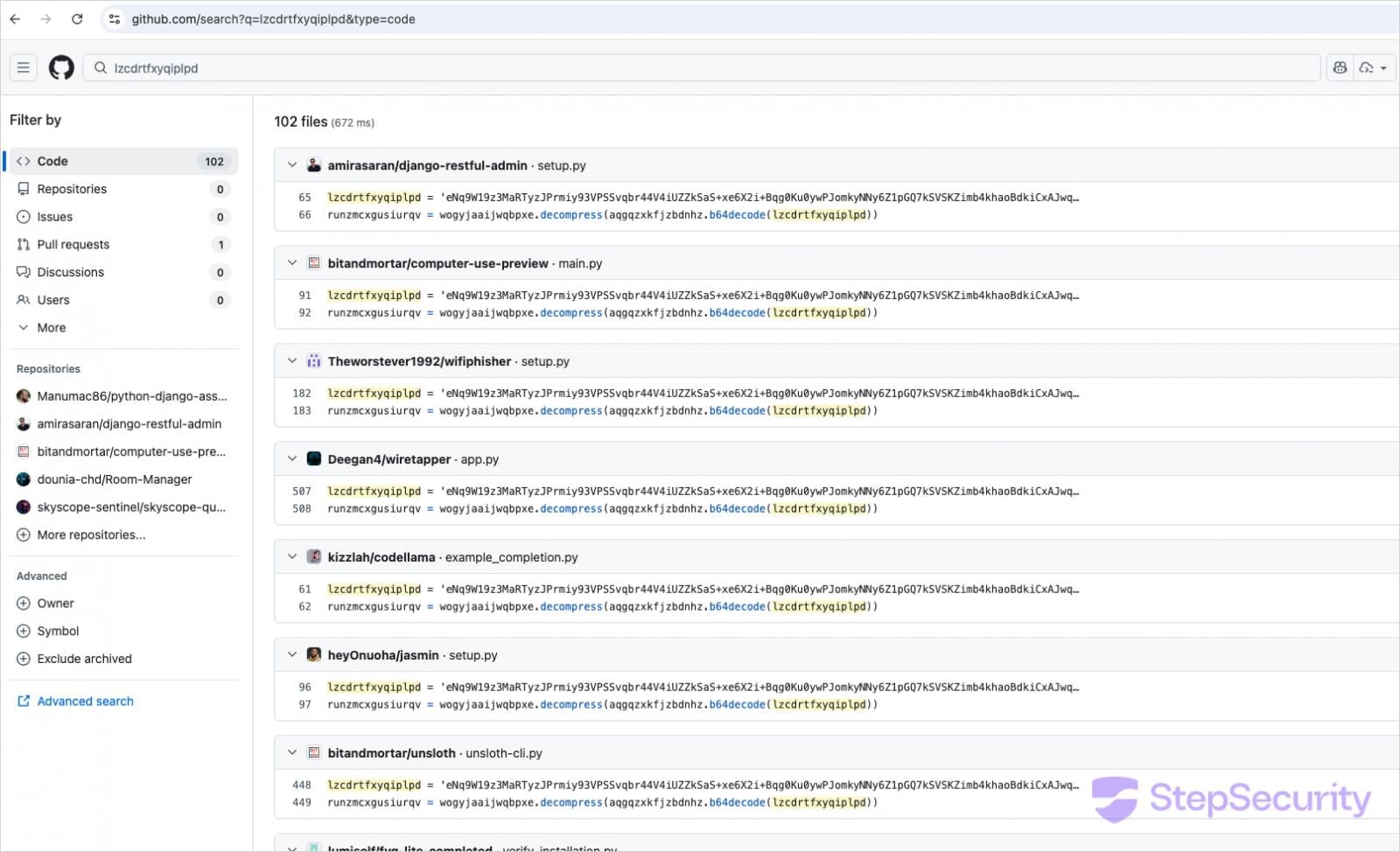
The attack methodology follows a predictable, yet highly effective, chain reaction. The initial point of intrusion appears to be GitHub. Threat actors gain unauthorized access to developer accounts—likely through credential stuffing, phishing, or token theft—and then utilize the force-push command. This Git function overwrites existing commit history, allowing the attacker to inject malicious changes directly into the main branch of the repository without triggering standard pull request reviews or history checks.
Once the repository is compromised, the malicious code is packaged and published across the downstream dependency managers. For JavaScript environments, this means deploying tainted packages to npm. For IDE users, it involves uploading compromised extensions to the relevant marketplace or registry. The key to evading real-time detection lies in the persistent use of obfuscation techniques, notably the "invisible" Unicode characters, which disrupt string matching and character-based scanners.
A central element of the GlassWorm infrastructure is its reliance on the Solana blockchain for dynamic command delivery. This is a cutting-edge C2 technique that leverages a public, high-throughput ledger to distribute instructions while maintaining a degree of operational security. The malware component, once executed on a victim’s machine, queries the Solana blockchain at highly frequent intervals—reportedly every five seconds—seeking new instructions embedded within transaction memos.
Analysis of transaction history, spanning from late November 2025 to mid-March 2026, reveals approximately 50 distinct transactions dedicated to payload updates. This demonstrates an agile response capability; the threat actor can quickly shift the target URL or update the malware’s behavior without having to reissue the compromised packages themselves, effectively bypassing repository takedowns.
The execution chain is highly specialized. The instructions retrieved from Solana direct the malware to download and execute the legitimate Node.js runtime environment, even if one is not already present, to facilitate the execution of a custom, JavaScript-based information stealer. This reliance on a common runtime minimizes the introduction of suspicious binaries, aiding evasion.
The data exfiltration targets are high-value: cryptocurrency wallet credentials (a consistent theme), general system credentials, authentication tokens, SSH keys vital for infrastructure access, and a broad spectrum of developer environment configurations, which can yield further access vectors.
Industry Implications and Geopolitical Context
Initial code comment analysis suggests that the operators of GlassWorm may be affiliated with Russia-speaking threat groups. This assessment is partially supported by the malware’s programmed "self-sabotage" mechanism: it refuses to execute if the system locale is detected as Russian. While this linguistic filtering is often used by state-sponsored or organized crime groups to limit exposure within their own geographical sphere, security professionals caution against making definitive attribution based solely on such indicators, which can be easily spoofed or misinterpreted.
The impact of this campaign on the software industry is profound, highlighting critical vulnerabilities not just in specific tools, but in the fundamental trust models underpinning modern software development.
For Software Vendors and Platform Owners: The continuous success of GlassWorm across GitHub, npm, and VSCode/OpenVSX demonstrates that perimeter defense is inadequate. These platforms must enhance real-time anomaly detection, particularly focusing on post-compromise activities like Git force-pushes and rapid package version updates that deviate from normal developer workflow patterns. The use of blockchain for C2 necessitates that security monitoring tools begin incorporating blockchain transaction analysis as a potential indicator of compromise (IOC).
For Enterprise Security Teams: This incident mandates a drastic re-evaluation of software supply chain risk management. Relying solely on signature-based detection for downloaded packages is clearly insufficient. Enterprises must enforce strict policies regarding dependency provenance, potentially utilizing internal artifact repositories that vet and quarantine third-party packages before deployment. The scope of the compromise—targeting credentials, SSH keys, and environment data—means that an infection in a single developer’s environment can cascade into complete network compromise.
Expert Analysis and Future Trends
The sophistication of GlassWorm represents an advanced phase in software supply chain attacks, moving beyond simple typo-squatting or dependency confusion. It employs a multi-vector approach: account takeover (GitHub), stealthy code injection (Unicode obfuscation), and resilient C2 architecture (Solana).
Dr. Anya Sharma, a lead researcher specializing in software integrity at a major cybersecurity firm, notes that the reliance on the Solana ledger is particularly telling. "We are seeing threat actors weaponize the decentralization and transparency of public blockchains not just for cryptocurrency laundering, but as a highly effective, low-cost, and resilient mechanism for delivering malware instructions," she explains. "It bypasses traditional network firewalls and threat intelligence feeds that are not yet equipped to monitor blockchain memo fields as C2 traffic."
Furthermore, the malware’s execution strategy—using the victim’s own Node.js runtime—is a classic example of "living off the land" (LotL) techniques, making forensic analysis difficult as the malicious activity blends into standard runtime processes.
Looking ahead, this incident suggests several emerging trends:
- Hyper-Targeted Obfuscation: Attackers will continue to explore non-standard character sets and encoding tricks to defeat static scanners, pushing the burden of security onto dynamic execution analysis and behavioral monitoring.
- Blockchain C2 Proliferation: Expect to see other threat groups adopt this method, perhaps using different decentralized ledgers, as it offers superior resilience compared to traditional C2 servers that are easily sinkholed.
- IDE-Centric Attacks: As development environments become more integrated and complex, extensions and plugins will remain prime targets. Attacks focusing specifically on VSCode, IntelliJ, and related tooling will intensify, as compromising an extension grants immediate, trusted access to a developer’s active workspace.
Mitigation and Immediate Remediation Steps
Organizations and individual developers must take immediate, targeted action based on the forensic indicators provided by researchers:
- GitHub Repository Audit: Developers who use Python packages installed directly from GitHub or who frequently clone repositories should immediately scrutinize their local codebases. The specific marker variable
lzcdrtfxyqiplpdshould be used as a high-priority search term across all recently cloned or modified project files. - Persistence Check: Inspect user home directories (
~) for the presence of the~/init.jsonfile. This file is strongly associated with establishing persistence mechanisms for the GlassWorm malware. - Runtime Environment Scrutiny: System administrators and developers should search the home directory for unexpected installations of the Node.js runtime, particularly directories named with version numbers like
~/node-v22*. Malicious activity often involves installing a specific runtime to ensure payload execution consistency. - File Anomaly Detection: Look for suspicious JavaScript files, specifically those named
i.js, located within the context of recently cloned projects. - Git History Review: A critical, albeit time-consuming, step involves reviewing Git commit histories in compromised repositories. A key giveaway is a significant discrepancy between the "Author Date" (when the change was originally written) and the "Committer Date" (when the malicious change was forced onto the branch). Large gaps or reversed timelines here are strong indicators of account takeover and force-push manipulation.
The GlassWorm campaign serves as a stark reminder that the security of software is intrinsically linked to the security of the tools and platforms used to build it. As integration deepens, the supply chain becomes a single, complex attack surface demanding continuous, sophisticated defense strategies that look beyond conventional network boundaries.