A significant security breach, stemming from a lapse in digital asset handling protocols by a major governmental body, has resulted in the immediate loss of approximately $4.8 million in cryptocurrency. South Korea’s National Tax Service (NTS) inadvertently broadcast the mnemonic recovery phrase—the master key to a hardware cryptocurrency wallet—during a public announcement detailing the successful seizure of illicitly held digital assets. This incident serves as a stark, high-stakes demonstration of the critical difference between physical asset forfeiture and the immutable, unforgiving nature of decentralized finance (DeFi) security.
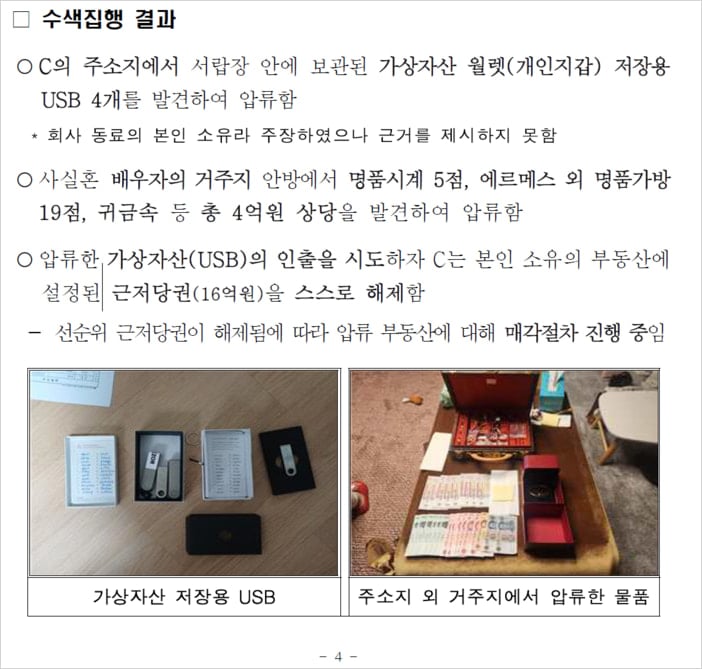
The confiscated cryptocurrency was part of a broader operation targeting 124 high-net-worth tax evaders, netting digital assets valued initially at around 8.1 billion Korean Won, equivalent to approximately $5.6 million USD at the time of seizure. The NTS, aiming to publicize the success of their enforcement action against tax avoidance, released photographic evidence showcasing the hardware device used to secure these funds—a Ledger cold wallet, a widely recognized standard for secure, offline cryptocurrency storage. In a devastating oversight, however, the accompanying imagery prominently featured a handwritten note containing the full 12- or 24-word seed phrase, which grants absolute, unrestricted access to the wallet’s contents without requiring the physical device or any associated PIN.
The failure to redact this single, critical piece of information effectively neutralized the security measures of the cold storage solution. Within a short timeframe following the press release, opportunistic actors leveraged this exposed seed phrase to restore the wallet onto their own hardware. On-chain forensic analysis, scrutinized via explorers like Etherscan, revealed the precise methodology of the theft. The perpetrator first initiated a small transaction, depositing a negligible amount of Ethereum (ETH) into the compromised wallet solely to fund the necessary gas fees for subsequent transfers. Following this preparatory step, the attacker systematically drained the primary holding: 4 million units of the Pre-Retogeum (PRTG) tokens, valued at the moment of extraction at roughly $4.8 million, were moved across three distinct transactions to an address under the thief’s control.
This event transcends a simple procedural error; it represents a fundamental breakdown in understanding the security paradigm of self-custody cryptocurrency. Dr. Cho Jae-woo, a blockchain analysis expert and professor at Hansung University in Seoul, articulated the severity of the blunder by drawing a potent analogy: the action was equivalent to "leaving a safe unlocked, posting the combination on a national billboard, and inviting the entire citizenry to empty the contents." Professor Cho further emphasized that the root cause was the tax authority’s demonstrable "lack of basic understanding of virtual assets," a deficit that resulted in the tangible loss of tens of billions of Won that the state had successfully recovered through legal enforcement.

The immediate aftermath saw the NTS rapidly retracting the offending press release from its official website. However, the digital trail remains indelible. While the status of any internal investigation into locating the perpetrator or tracing the dispersed assets is currently opaque, the industry has been left grappling with the implications of a government agency falling victim to one of the most elementary security pitfalls in the crypto space.
The Immutable Nature of Seed Phrases: Context and Industry Ramifications
To appreciate the magnitude of this failure, one must understand the architecture of hardware wallets. Devices like Ledger function by generating and storing a private key sequence—the seed phrase—in a secure, isolated enclave that never leaves the device during normal operation. This phrase is the cryptographic master key. Possession of the seed phrase is functionally equivalent to possessing the assets themselves; it allows immediate recreation of the wallet on any compatible device, bypassing hardware PINs, biometrics, or any other secondary security layers.
In traditional finance, seizing assets often involves taking physical possession of bearer bonds or securing access credentials to a centralized account. These processes have established, albeit complex, legal and physical protocols for chain of custody and secure storage. Cryptocurrency, by contrast, operates on a principle of "code is law." Once the seed phrase is compromised and used, the transfer is irreversible by any central authority. The NTS’s act of photographing and publicly displaying this phrase converted what should have been a highly secured, seized asset into an open-source target.
This incident has profound implications for government handling of digital assets globally. As regulatory bodies worldwide become more aggressive in seizing and managing cryptocurrency related to criminal activity, money laundering, or tax evasion, this South Korean case establishes a dangerous precedent. It highlights a critical gap: many law enforcement and tax agencies possess the legal authority to seize digital assets but lack the requisite, specialized digital forensics and security expertise to handle them appropriately post-seizure. The standard operating procedures developed for physical evidence—where documentation often involves photographs—are dangerously inadequate when applied to cryptographic secrets.
For the broader cryptocurrency industry, this event acts as a high-visibility, cautionary tale reinforcing established best practices. It validates the decade-old mantra: "Not your keys, not your crypto," and more specifically, "If someone else has your keys, it’s not really yours." This is particularly relevant for institutional custodianship and government holdings, where the expectation of robust security infrastructure is paramount. The theft underscores that the greatest vulnerability in self-custody is not a flaw in the blockchain or the hardware wallet itself, but human error in managing the root secret.

Expert Analysis: Security Protocols and Procedural Failures
From a technical security standpoint, the NTS violated several cardinal rules of cryptographic key management. First, Never Digitize the Secret: Seed phrases should ideally be recorded physically, etched in metal or stored on paper in multiple, geographically dispersed, and physically secure locations (e.g., high-security vaults). Digitizing the phrase—whether by writing it down and photographing it, saving it in a password manager, or storing it in cloud storage—introduces vectors for digital compromise, from phishing to insider threat access. The NTS combined the worst of both worlds: they digitized the secret (via photograph) and then published that digital representation publicly.
Second, Need-to-Know Access and Information Sanitization: When documenting the seizure of a hardware wallet for evidentiary or public relations purposes, security protocols must mandate the complete redaction of all mnemonic phrases and recovery data. Any image of the device should only show the exterior casing or the screen displaying a non-sensitive status update, such as a locked state or general menu interface. The fact that the recovery phrase was handwritten suggests an attempt at physical security, but this physical note was then carelessly photographed and released into the digital ether without proper scrubbing.
Security architects specializing in zero-trust environments often emphasize that the system owner must assume compromise at every layer. In this context, the NTS failed to establish a secure perimeter around the most sensitive piece of data they held. The attacker’s swift, calculated move—funding the gas first—demonstrates operational awareness, suggesting the perpetrator was likely monitoring public sources for just such an opportunity, indicating that the window between exposure and theft was likely very short.
Future Impact and Evolving Standards for Digital Asset Custody
The fallout from this multi-million dollar loss will likely force significant shifts in how governmental and large-scale institutional entities approach digital asset forfeiture and custody. We can anticipate several immediate and long-term industry impacts:
1. Mandatory Security Audits for Government Agencies: This incident will almost certainly trigger internal reviews and potentially regulatory mandates requiring specialized third-party security audits for any government division tasked with handling private cryptographic keys. These audits will need to specifically address documentation standards for hardware and on-chain evidence.
2. Shift Towards Multi-Signature (Multi-Sig) Architectures: For assets seized in large volumes, reliance on single-signature wallets secured by a single seed phrase (as was the case here) is proving too risky, even for professional custodians. Future government seizure protocols will likely pivot towards multi-signature wallets, requiring approvals from multiple, geographically and organizationally distinct parties to authorize a transfer. This introduces redundancy and prevents a single point of failure, such as an exposed recovery sheet.
3. Development of Specialized Forensic Chain of Custody Tools: The current tools for evidence handling are ill-equipped for digital assets. There will be increased demand for specialized, auditable software solutions designed to transfer seized crypto from the original owner’s wallet to a government-controlled, multi-sig vault, all while generating tamper-proof logs and ensuring that no single technician ever has access to the complete recovery mechanism.
4. Enhanced Public Relations Vetting: Agencies will become far more cautious about what they publicize regarding seized assets. The desire to demonstrate successful enforcement must be strictly balanced against the overriding imperative to protect the security of the assets themselves. Future press releases will likely rely solely on aggregate data or heavily obfuscated visual evidence.
Ultimately, the theft of $4.8 million was not a sophisticated hack against a blockchain or an encrypted server; it was a successful exploitation of administrative negligence. It serves as a critical lesson that in the realm of cryptocurrency, operational security (OpSec) surrounding the seed phrase is the single most important defense layer. The incident reinforces that while blockchain technology provides mathematical finality, human procedures dictate whether that finality protects or surrenders value. For any entity taking custody of digital wealth, the lesson is clear: assume the public has access to your documentation until you have proven otherwise, and treat the recovery phrase with the same reverence as the physical keys to a nuclear arsenal.

