The landscape of personal and small-scale digital security is undergoing a subtle but significant evolution with the introduction of a new capability within the Bitwarden ecosystem, formally dubbed the "Cupid Vault." This feature represents a strategic move by the open-source password manager to democratize secure credential sharing, extending functionality traditionally reserved for premium tiers down to its free user base. At its core, Cupid Vault leverages the established architecture of Bitwarden Organizations but configures it specifically for intimate, two-person collaboration, offering a protected channel for users to exchange sensitive login details, such as streaming service credentials or shared utility account access, without relying on insecure communication methods like plain text email or messaging applications.
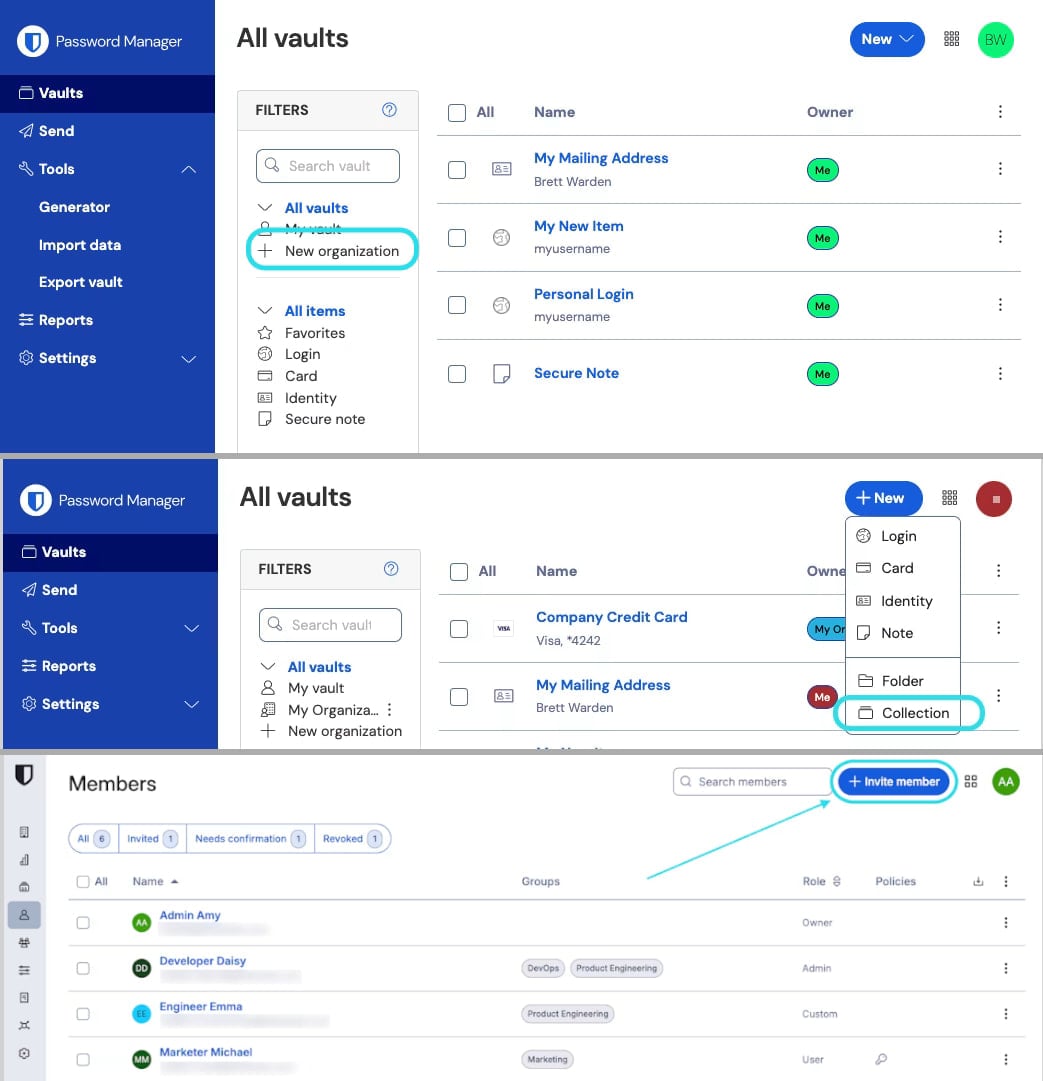
This new mechanism hinges on the creation of a minimalist "Organization," which is strictly capped at two members. For users operating on Bitwarden’s complimentary tier—a significant demographic for any open-source security tool—this provides a dedicated, cryptographically secured space. The primary account holder, the vault owner, initiates the process, essentially spinning up a two-person shared vault. The crucial step involves inviting a second trusted individual, often a family member, partner, or close associate, via their registered email address. Once accepted, this shared space, or "Organization," functions as an isolated container, entirely separate from the members’ personal vaults, ensuring that shared secrets remain compartmentalized.
The technical implementation focuses heavily on maintaining the integrity of the sharing relationship. Access to the shared items is granted through credentials assigned specifically within the context of this Organization, managed by the owner. Furthermore, Bitwarden has integrated a critical security checkpoint to mitigate potential man-in-the-middle enrollment vulnerabilities. This verification process involves the presentation of a fingerprint phrase—a cryptographic confirmation that the intended recipient is indeed the party being onboarded. This emphasizes the importance of out-of-band, trusted communication during the initial setup phase, a best practice in any zero-trust security model, even one deployed at a personal scale.

A key architectural decision underpinning Cupid Vault is the egalitarian management structure imposed on the shared items. Unlike scenarios where a creator retains sole dominion over shared content, items placed within this two-person Organization are not bound by their creator’s ownership status. Both members possess the necessary permissions to edit or delete shared credentials. This bidirectional control is vital for scenarios where shared access needs to be dynamically managed—for instance, if one party needs to update a password and immediately share the new credential with the other. Conversely, the owner retains the immediate ability to sever the link; access can be revoked unilaterally and instantaneously, making the unsharing process as secure and straightforward as the initial sharing.
The availability of Cupid Vault through the free tier is noteworthy. Bitwarden, which has built its reputation on providing robust, end-to-end encrypted storage utilizing open standards, is now directly challenging the friction points inherent in casual, secure sharing among trusted circles. Historically, while individuals might use a single password manager for personal use, sharing a Netflix password with a spouse or a cloud storage login with a co-parent often devolved into risky practices. Cupid Vault addresses this common security gap by providing a zero-cost, purpose-built bridge.
However, the limitations of the free implementation are clearly defined. The constraint limits the shared Organization to just two users and a maximum of two distinct "Collections"—subdivisions within the vault used to logically group related credentials. This configuration strongly suggests the feature is calibrated for bilateral relationships, such as romantic partnerships or small, highly intimate domestic arrangements, rather than small business collaboration, which requires greater flexibility.
For users already subscribed to Bitwarden’s premium offerings—Family, Teams, or Enterprise plans—the Cupid Vault functionality is, by design, redundant. These paid tiers already provide sophisticated mechanisms for sharing, including multi-user support, unlimited collections, and granular Role-Based Access Control (RBAC). It is crucial for the user base to understand this distinction; Cupid Vault is a specialized enhancement for the free tier, not a rebranding or addition to the advanced administrative controls available to paying subscribers.

Background Context and Industry Implications
The introduction of Cupid Vault must be viewed within the broader context of password manager market evolution. As password managers transition from niche security tools to mainstream digital necessities, the pressure increases on vendors to offer seamless sharing capabilities. Traditional enterprise sharing models, which focus on team management and audit trails, are often overly complex or simply unavailable for personal use cases.
Bitwarden’s approach here is strategically astute. By embedding a simplified sharing utility within the free product, they lower the barrier to entry for individuals who might otherwise avoid sophisticated security tools due to perceived complexity or cost. This move directly addresses the "last mile" problem in personal security—the gap between securing one’s own data and securely interacting with a trusted few.
From an industry perspective, this forces competitors to re-evaluate their free-tier offerings. If secure, two-party sharing becomes a standard expectation for a free password manager, vendors who restrict this feature exclusively to paid tiers may see user migration toward the Bitwarden ecosystem. It positions Bitwarden not just as a secure vault, but as a foundational layer for small-scale digital trust networks.
Expert-Level Analysis of Security Architecture
The security foundation of Cupid Vault remains tethered to Bitwarden’s robust, open-source architecture. All data within any Bitwarden vault, including those established as Cupid Vaults, is protected by end-to-end encryption. This means that data is encrypted on the user’s device before transmission and remains encrypted at rest on Bitwarden’s servers, accessible only via the user’s master password and key material.
The shared nature of the Organization means that the master key material for the shared vault is synchronized between the two members. While this is necessary for shared access, it underscores the absolute necessity of the fingerprint phrase verification. If an attacker could successfully perform an adversary-in-the-middle attack during the invitation process, they could potentially intercept the necessary cryptographic material to decrypt the shared collection. Bitwarden’s emphasis on cryptographic verification during enrollment is therefore not just a feature but a necessary safeguard against social engineering or network interception targeting the initial trust establishment.
Furthermore, the shared item ownership model warrants careful consideration. When both parties can edit or delete items, the security model shifts from centralized control to consensus or mutual trust. This is suitable for high-trust relationships (e.g., married couples managing shared accounts) but could be problematic in lower-trust or semi-professional collaborations where clear administrative boundaries are essential. For complex scenarios, users are rightly guided toward the paid plans which offer the necessary fine-grained permissions. The elegance of Cupid Vault lies in its minimalism, which inherently sacrifices administrative granularity for simplicity and security in a binary relationship.
Future Impact and Trends in Secure Sharing
The launch of Cupid Vault anticipates a growing trend: the merging of personal and small-group digital management. As digital lives become increasingly intertwined—sharing family cloud storage, managing joint streaming subscriptions, coordinating access for remote work among a very small contract team—the need for secure, temporary, or bilateral sharing mechanisms will only intensify.
This feature points toward a future where identity and access management (IAM) principles are applied more rigorously to domestic life. Users are beginning to demand the same level of cryptographic rigor for sharing a $15/month streaming login as they do for securing their banking credentials. Cupid Vault’s success may spur further innovation in this niche, potentially leading to:
- Time-Bound Sharing: Offering the ability to grant access to a credential for a fixed duration (e.g., 72 hours) before automatic revocation, a feature that would be invaluable for temporary collaborations.
- Granular Permission Scoping within Free Tiers: While current limitations restrict this, future iterations might allow free users to designate whether a shared item can only be viewed, or if it can also be edited, without migrating to a full paid Organization structure.
- Enhanced Recovery Mechanisms for Shared Vaults: Developing secure protocols that allow the remaining trusted party to regain sole control if one member becomes entirely unreachable, without compromising the encryption integrity.
Bitwarden’s decision to anchor this functionality in the free offering is a potent market signal. It suggests that the company views widespread adoption of secure sharing practices—even at the simplest level—as a net positive for overall digital hygiene, thereby strengthening the entire user base and fostering loyalty toward the platform as the default choice for all digital credential management needs. The cross-platform compatibility—spanning browsers, desktops, and mobile environments—ensures that this secure sharing mechanism is accessible wherever the users operate, reinforcing its utility across the modern, multi-device digital environment. The reliance on established, audited, end-to-end encryption protocols ensures that while the setup is simple, the security posture remains enterprise-grade for the data contained within that specialized, two-person Organization.

