The modern web browser has evolved far beyond a simple portal for rendering static documents. Today, platforms like Chrome, Firefox, and Edge are sophisticated application environments, heavily reliant on third-party extensions to tailor functionality, enhance productivity, and integrate specialized services. This symbiotic relationship, while empowering for the end-user, introduces a critical, often underestimated, vector for digital insecurity: the browser extension supply chain. The fundamental trust users place in an extension—often granting it broad permissions over browsing activity, form data, and potentially sensitive session information—is not immutable. It is conditional upon the integrity and continued ethical stewardship of the original developer. This premise forms the bedrock of a growing cybersecurity concern: what happens when an extension changes hands?
This digital handover scenario—where a developer sells their popular, trusted add-on to an unknown or potentially malicious entity—represents a stealthy form of digital hijacking. A previously benign utility, endowed with permissions to read browsing history or inject scripts, can instantaneously pivot into a data exfiltration tool or a persistent vector for adware delivery. For users accustomed to installing an extension once and forgetting about it, the lack of notification regarding such a fundamental shift in ownership creates a significant, blind vulnerability.
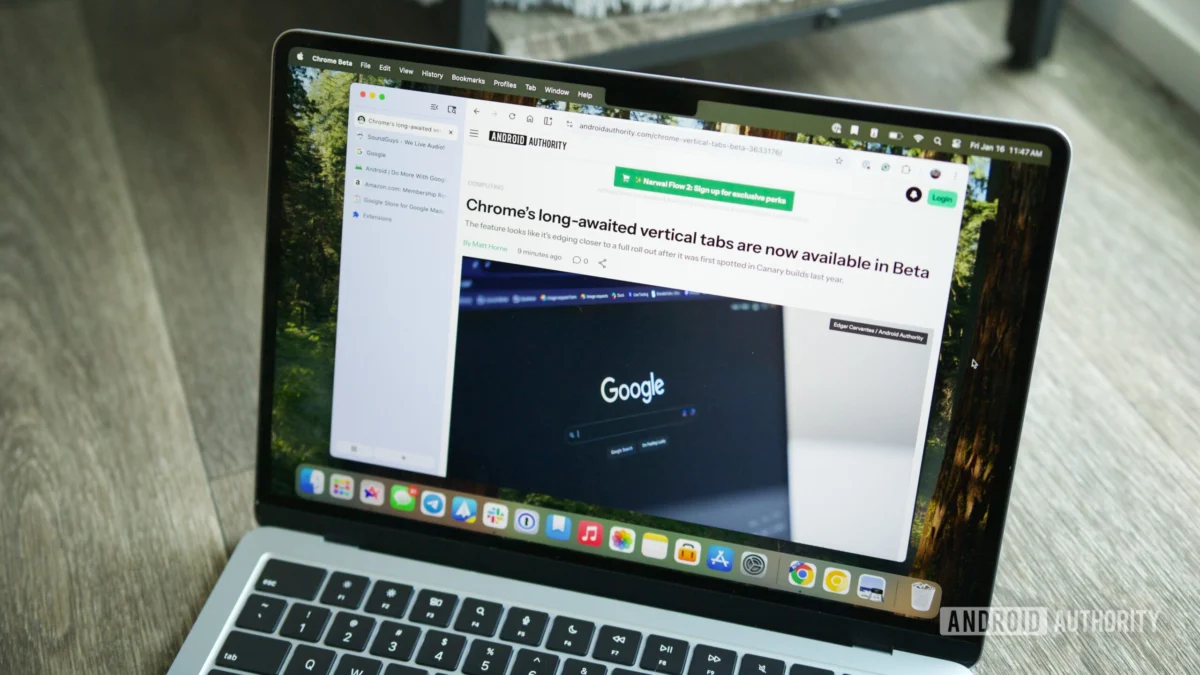
It is precisely this gap in transparency that has spurred the development of specialized tools designed to monitor and flag these critical ownership transitions. A notable example highlighting this specific security niche is a utility designed for the Chromium-based ecosystem, which functions as an autonomous auditor for the user’s installed add-ons. This tool is engineered to observe metadata associated with installed extensions and cross-reference it against known developer records, issuing an alert the moment a change in the publishing entity is detected within the extension store’s backend.
The necessity for such a proactive monitoring solution is underscored by real-world incidents. The digital landscape is littered with cautionary tales where extensions with millions of users, once deemed safe, were acquired by actors who subsequently monetized that established trust through nefarious means. A prominent case involved an extension focused on image manipulation, which, after acquisition, began systematically harvesting user data, including potentially sensitive input fields, over an extended period. Because the change in behavior often follows a change in ownership, monitoring the latter becomes a powerful proxy for mitigating the former. The original developer’s ethos, which might have guaranteed privacy, is instantly superseded by the new owner’s agenda, which may prioritize revenue generation over user security.
The Mechanics of Trust Erosion and Auditing
The functioning of these browser extensions relies on API access and content scripts, which necessitate permissions that users often grant liberally. When a user installs an extension, they are effectively extending the security perimeter of their browser to include the extension’s code. The core vulnerability arises because the extension stores in the Web Store are typically identified by a unique package ID, which remains constant even if the associated developer account changes. This persistence allows the malicious actor to inherit the established reputation and trust score of the extension, bypassing the initial user skepticism that a newly published, unknown extension would face.
The auditing extension addresses this by continuously polling the backend metadata provided by the browser’s extension marketplace—the central repository of truth for package authorship. When the name or ID associated with the package undergoes an update, the auditing software recognizes this as a significant change in stewardship. This mechanism bypasses the superficial checks a user might perform, such as reading the changelog, because the critical event—the transfer of ownership—occurs silently at the repository level.
For the solo developer who created such an auditing tool, the endeavor often stems from personal experience with compromised trust. In the case of the specific utility mentioned, it remains a relatively small project, supported by a handful of thousands of users. This low profile is, paradoxically, a security feature in itself. A smaller user base means less immediate appeal to large-scale data harvesting operations, and its open-source nature, typically hosted on platforms like GitHub, allows technically proficient users to inspect the code themselves. This transparency mitigates the "trusting the auditor" paradox: if users are wary of the auditor being compromised, they can verify the auditor’s integrity independently. Furthermore, a lack of recent, frequent updates can indicate a stable, focused tool, rather than one actively being developed for potentially exploitable changes.
Industry Implications: A Call for Platform-Level Security Enhancements
The existence of third-party solutions like this ownership auditor points to a recognized gap in the native security features offered by major browser vendors, particularly Google with Chrome. While platforms employ sophisticated malware scanning and policy enforcement to prevent overtly malicious submissions, they have historically lagged in providing granular, real-time alerts about post-installation ownership changes.
From an industry perspective, this phenomenon forces a re-evaluation of developer lifecycle management. For software corporations, the acquisition of a product line that includes popular browser extensions requires rigorous due diligence, often extending beyond standard IT asset auditing into a comprehensive security review of the acquired codebase and its active permissions. The risk isn’t just reputational; it’s the direct liability associated with user data exposure traced back to an asset under their control.
Security researchers suggest that browser vendors could implement several proactive measures to address this systemic weakness:
- Mandatory Re-Authorization: Any change in the registered developer account for an installed extension should automatically trigger a prompt requiring the user to explicitly re-authorize the extension’s permissions, essentially forcing a "new installation" security review.
- Version Tagging for Ownership: Metadata within the extension package itself could be flagged to indicate the current known owner, making integrity checks faster and more robust than relying solely on external store APIs.
- Developer Vetting and Bonding: For extensions exceeding a certain user threshold (e.g., 100,000 active users), stricter identity verification or even a form of escrow or bonding system could be implemented, ensuring financial or legal recourse exists if the extension is later sold to a malicious actor.
These platform-level changes would shift the burden of vigilance away from the end-user, who is already overwhelmed with security alerts, and back to the centralized gatekeepers of the ecosystem.
Future Trends: Decentralization and Zero Trust Browsing
Looking ahead, the issue of extension integrity intersects with broader trends in digital security, notably the move toward zero-trust architectures and decentralized identity management. If browser extensions increasingly adopt decentralized identifiers (DIDs) or verifiable credentials issued by the platform, tracking the lineage of authorship becomes cryptographically verifiable rather than relying on the mutable database records of a centralized store.
Furthermore, the industry is exploring more granular permission models. Instead of granting an extension blanket access to "all tabs," future systems might enforce context-specific permissions that only activate when the user is on a whitelisted domain or explicitly invokes the extension’s functionality. This limits the "blast radius" of a compromised extension, even if its ownership has shifted maliciously.
The development and utilization of tools like the ownership auditor serve as an important, if informal, stress test for the current state of browser security. They highlight that user empowerment through choice—the freedom to extend functionality—must be balanced by robust, automated safeguards against the inevitable exploitation of that freedom. As extensions become more deeply integrated into professional workflows, the concept of monitoring the stewardship of the software, rather than just its code, will transition from a niche concern to a mainstream security requirement. The digital environment demands constant vigilance, and proactive, specialized tools are the necessary infantry in this ongoing defense against subtle supply chain attacks. The ability to know who is running the code you trust is quickly becoming as vital as knowing what the code does.