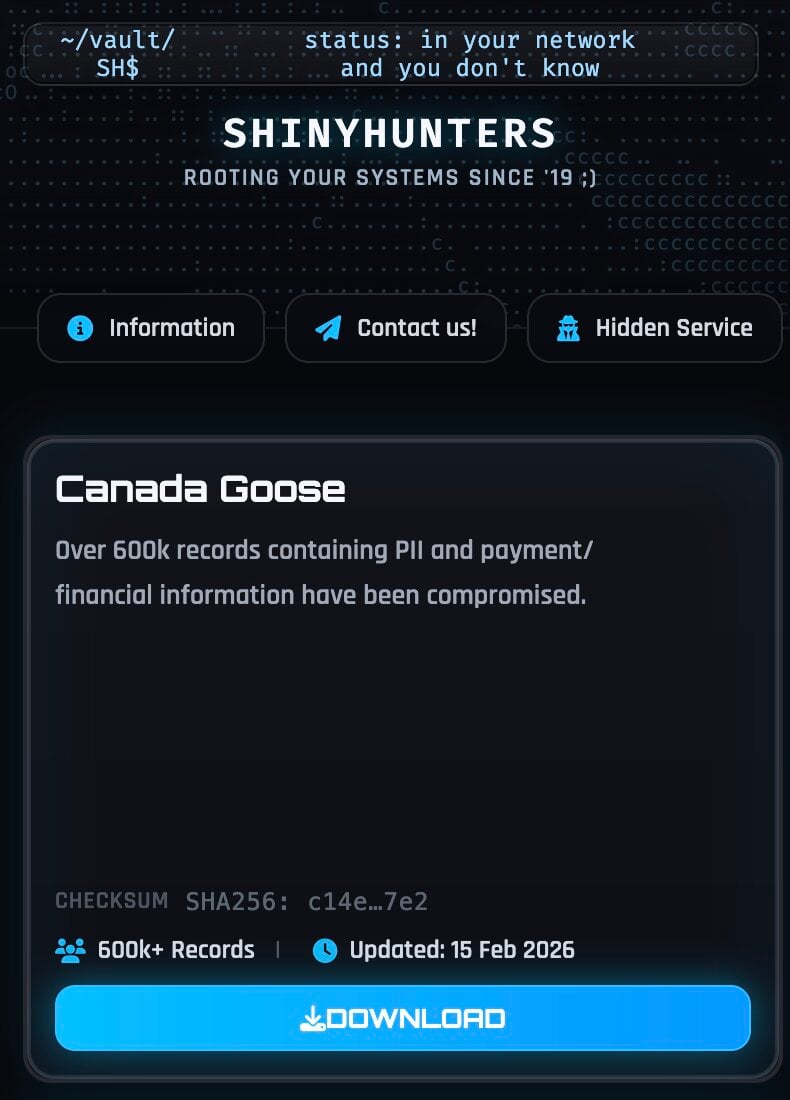
The digital security landscape for high-end consumer brands is once again under scrutiny following claims by the notorious data extortion collective, ShinyHunters, that they have successfully exfiltrated a substantial dataset containing records pertaining to over 600,000 patrons of Canada Goose. The Toronto-based performance luxury outerwear purveyor, established in 1957 and recognized globally for its premium cold-weather gear, is now engaged in an intensive internal investigation, even as the alleged breach data circulates on illicit online forums.
Canada Goose has issued a statement acknowledging the existence of the publicly surfaced dataset. Crucially, the company maintains that its preliminary assessment indicates the data pertains strictly to historical customer transactions and, as of the current review, there is no corroborating evidence suggesting a direct compromise of Canada Goose’s proprietary internal systems or primary infrastructure. This distinction—whether the breach occurred within the brand’s perimeter or at a connected third-party vendor—is pivotal in understanding the scope of liability and the subsequent remediation roadmap. The company has stressed its commitment to customer data protection while it meticulously evaluates the veracity and extent of the exposed information, specifically confirming that unmasked financial data was not part of the disclosure.
Anatomy of the Alleged Exposure
ShinyHunters, a group known for aggressively monetizing stolen corporate information, publicized the alleged cache on their dedicated leak site this week. The purported archive totals 1.67 gigabytes and was distributed in the standardized JSON format, a common output for e-commerce data dumps. Initial forensic sampling of the leaked files reveals a trove of personally identifiable information (PII) linked to online transactions. This includes comprehensive customer identifiers such as full names, email addresses, associated telephone numbers, detailed billing and shipping addresses, timestamps of user sessions, IP addresses, and complete records of prior purchase histories.
Perhaps more concerning for consumers is the inclusion of partial payment card details. While the threat actors claim—and Canada Goose’s initial review supports the assertion—that full, primary account numbers (PANs) were not compromised, the exposed fragments present a significant risk vector. The data reportedly includes the card brand (e.g., Visa, Mastercard), the final four digits of the card number, and, critically, the Bank Identification Number (BIN)—the first six digits that identify the issuing institution and card type. This BIN information, coupled with transaction metadata and specific authorization details, is highly valuable to cybercriminals. Even without the full card number, this data facilitates sophisticated phishing campaigns, highly personalized social engineering attacks, and identity theft escalation, as it allows criminals to cross-reference data points across other compromised databases to reconstruct more complete profiles.
Furthermore, the dataset provides granular insights into consumer behavior, including precise purchase values, device fingerprints, and browser configurations. For a luxury brand like Canada Goose, this information enables threat actors to construct detailed profiles of high-net-worth individuals, making subsequent extortion attempts or targeted fraud significantly more potent.
The Third-Party Nexus and Operational Security
The narrative surrounding the origin of this data is complex and points toward a growing industry vulnerability: reliance on third-party service providers. When questioned about the source, ShinyHunters explicitly denied any connection to their recent, highly publicized social engineering campaigns that targeted corporate Single Sign-On (SSO) environments, as documented by cybersecurity firms like Mandiant. Instead, the group asserted that the Canada Goose records originated from a breach affecting a payment processor or an e-commerce platform provider, dating back to August 2025.
While Canada Goose has not independently validated this third-party claim, forensic analysis of the data structure lends credence to the possibility. The schema identifiers observed in the JSON—fields such as checkout_id, shipping_lines, cart_token, and cancel_reason—are highly characteristic of exports generated by hosted storefront solutions or integrated payment gateway platforms common in modern retail environments. This suggests that the vulnerability may not reside in the primary merchant’s core database, but rather in the extended supply chain responsible for facilitating and processing online commerce.
This scenario is becoming the archetypal breach narrative in the mid-2020s. Brands increasingly offload complex technical burdens, such as payment processing, inventory management, and customer relationship management (CRM) hosting, to specialized SaaS providers. While this optimizes operational efficiency, it exponentially increases the attack surface. A single vulnerability in a widely adopted payment processor or logistics partner can instantaneously expose the customer data of dozens or hundreds of their retail clients.
Industry Implications: The Erosion of Trust in E-commerce Ecosystems
The exposure of 600,000 records, regardless of the precise point of failure, sends ripples through the luxury retail sector. For brands like Canada Goose, whose value proposition is intrinsically tied to quality, exclusivity, and trust, a data leak is not just a compliance issue; it is a brand integrity crisis. Consumers paying a premium expect commensurate security protocols.

The fact that partial payment data was exposed—even if insufficient for direct card cloning—erodes consumer confidence in the security assurances made by online retailers. Financial regulatory bodies and consumer protection agencies worldwide are tightening scrutiny on data minimization practices. If a retailer retains partial payment data associated with historical records, it must demonstrate robust encryption and access controls, even if the data is deemed "non-PCI scope" by some standards. The presence of BIN data alone justifies heightened regulatory inquiry in jurisdictions with strict consumer protection laws, such as the GDPR in Europe or evolving state laws in the US.
Furthermore, the nature of the exposed data—PII combined with purchase history—presents a significant opportunity for targeted adversarial profiling. Attackers can use this information to craft hyper-realistic spear-phishing emails impersonating customer service, offering "exclusive loyalty rewards" or "order verification" prompts, thereby tricking victims into divulging more sensitive information, such as passwords or full financial credentials, in subsequent steps.
The Evolving Tactics of ShinyHunters
ShinyHunters remains one of the most persistent and adaptable data extortion groups operating today. Their operational profile has evolved beyond simple database scraping. Recent security intelligence has linked them to sophisticated, multi-stage campaigns that leverage social engineering, specifically Vishing (voice phishing) attacks targeting employees to compromise corporate SSO credentials.
While the group denies linking this Canada Goose incident to those SSO compromises, their continued activity underscores a strategic pivot toward exploiting the weak links in the digital chain—whether that is a direct network intrusion or an exploited third-party vendor. Their goal remains consistent: rapid monetization through public shaming on their leak site when ransom demands are refused. Their continued success relies on exploiting the complexity inherent in modern, interconnected digital ecosystems, where data traverses numerous vendor boundaries.
The group’s history includes successful data extractions from major SaaS providers, e-commerce platforms, and cloud infrastructure deployments. This pattern suggests that ShinyHunters possesses a sophisticated understanding of modern cloud architecture and the common misconfigurations that allow data exfiltration from environments that are ostensibly segmented but interconnected.
Future Impact and Data Security Trends
This incident highlights several critical trends that organizations, particularly in the high-value retail space, must address proactively:
- Supply Chain Diligence: The onus is increasingly falling on primary brands to audit the security posture of their entire vendor ecosystem. Contracts must mandate stringent security standards, evidence of regular penetration testing, and robust breach notification protocols. A brand’s security is only as strong as its least secure partner.
- Data Minimization as a Security Strategy: The long-term retention of historical transaction records containing even partial payment data must be re-evaluated. Regulatory compliance often dictates retention periods, but retailers must invest in advanced tokenization or cryptographic shredding techniques to ensure that if a historical database is breached, the data retrieved is rendered useless for financial fraud.
- Adaptive Threat Detection: Given the alleged August 2025 timeframe of the data, it implies that the compromise may have gone undetected by standard intrusion detection systems for months, if not longer. This necessitates a shift toward continuous monitoring of data egress points and anomalous activity within third-party connected systems, rather than relying solely on perimeter defense.
Canada Goose’s immediate response—investigating the dataset’s veracity while publicly stating its internal systems appear secure—is standard procedure. However, the true test will be in the transparency and speed with which they identify the root cause in the vendor chain and communicate directly with affected individuals. In the age of sophisticated data extortion, the time lag between compromise and customer notification is a crucial metric that directly impacts regulatory fines and, more importantly, long-term brand reputation. The industry watches to see if this incident serves as a catalyst for deeper integration of security requirements across the entire luxury retail fulfillment chain.

